Introduction
In this challenge from picoCTF 2026, we explore a common web security issue related to improper session management.
Web applications use sessions to keep users logged in. Normally, sessions should expire after a certain time or when the user logs out. However, if sessions do not expire properly, attackers may reuse old sessions to gain unauthorized access.
Recon
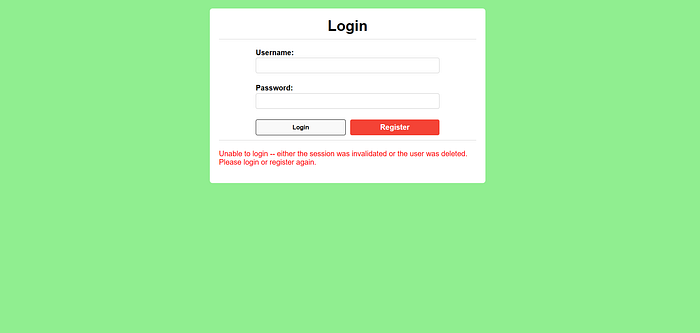
After launching the challenge instance, I logged into the website normally.
While inspecting the page , I noticed a comment in the code that contained a message from a user named: mary_jones_8992
The message was: Hey I found a strange page at /sessions
This comment hinted at the existence of a hidden endpoint within the application, which encouraged me to investigate further.
I then navigated to the following path:
/sessions
Vulnerability Discovery
When I navigated to /sessions, I found a list of active sessions on the website.

Surprisingly, one of these sessions belonged to an admin user.
This indicates a serious vulnerability:
- Sessions are publicly accessible
- Sessions are not expiring
- Sensitive session data is exposed
Exploitation
To exploit this vulnerability, I took the following steps:
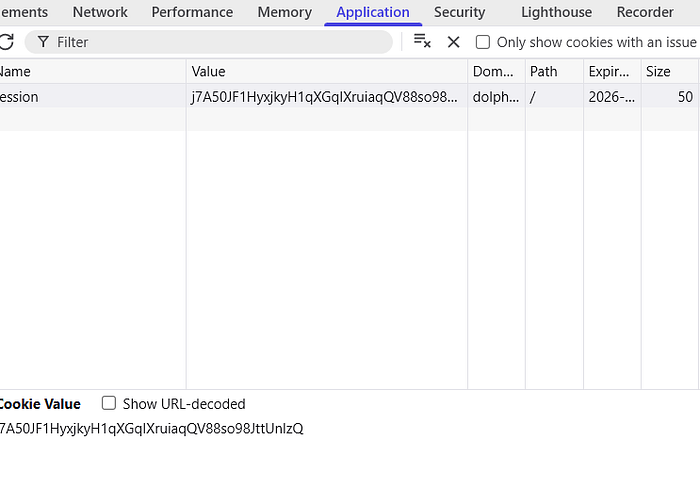
- Opened the browser Developer Tools
- Went to the Application → Cookies section
- Located my current session cookie
- Replaced it with the admin session ID obtained from
/sessions
After modifying the cookie, I refreshed the page.

Written by Ayman Hany CTF Player | Web Exploitation Enthusiast
Learning cybersecurity by solving challenges and exploiting real-world vulnerabilities.