Everyone wants to find the flashy zero-day. The wild chains, the weird parser bugs, the stuff that gets you into hall-of-fame territory.
But honestly, most bounties? They're hiding in plain sight — right where everyone else just walks by without a second glance.
The quiet bugs. The endpoints nobody cares about. The "too boring to matter" stuff.
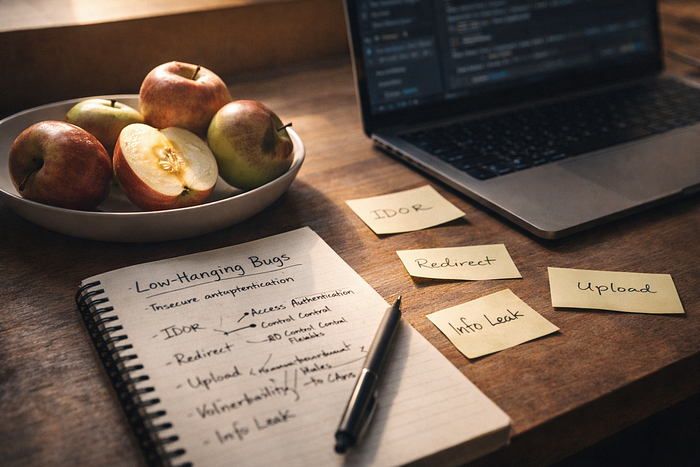
Low-hanging fruit. And here's the truth nobody likes to admit: most bug hunters don't fail because they're bad. They fail because they skip the obvious stuff.
This is about five of those doors. The ones that are still unlocked, still pay out, still lead to career-changing reports.
Nobody really digs into them. So let's actually look.
— -
🍏 1. The Forgotten ID Parameter
It always looks simple.
?id=1023 ?user=889 /order/44521
Just numbers. Nothing fancy.So you scroll past, thinking, "Nah, too easy. What else?"But ask any experienced hunter — they'll tell you: identifiers are never just numbers.
They're trust boundaries. Places where developers made assumptions about who owns what. And in modern apps, relationships leak everywhere.So — change the number. Trim a UUID. Try different encodings. Switch from mobile to web to API. Mix it up.
Then push further.
Check for:
* Bulk actions * Export/downloads * Soft-deleted stuff * Background jobs * Async processing
IDOR isn't just "swap the ID and win" anymore. You're following the data graph. Mapping ownership logic. Once you see that graph, chaining bugs together gets easy.
One IDOR can unlock:
* Emails * API keys * Internal IDs * Organization maps
So now your "low" bug is a pivot. You're in. Skipping ID-based testing? That's like ignoring a safe with the door wide open.
— -
🍏 2. The Silent Security.txt
Everyone loves big recon tools and scanning everything. But sometimes, the best recon comes down to a tiny, quiet file:
/.well-known/security.txt
It's almost invisible. Most people don't even look.
But inside, you might find:
* Private emails * Internal domains * Expiry dates * Encryption keys * Scope hints nobody's announced
Here's the cool part: security teams usually update this before public launches.
If you read it closely, you'll spot:
* Quiet VDP launches * Freshly acquired companies * New targets nobody knows about
While everyone else is fighting over the same bug bounty programs, you're off in the quiet corners, finding things first. This isn't a direct vulnerability it's your edge. And leverage leads to opportunity.
— -
🍏 3. The "Harmless" Open Redirect
People shrug at redirects.
"Low impact." "Doesn't pay." "Everyone reports these."
But context changes everything. Redirects aren't just bugs — they amplify other problems. Alone, they're tiny. But drop them into the right place — say, OAuth, password resets, SSO, email links, or mobile deep links — and they turn dangerous.
Now pair them with:
* Token leaks * Referer info * CSP bypasses * Phishing tricks
Suddenly, your harmless redirect is:
* Account takeover * Token theft * Brand abuse
Real hunters don't just report redirects. They weaponize them.
Ask yourself:
Where does trust flow? Where do tokens go? Where do users drop their guard?
That's where a "low" redirect goes critical.
— -
🍏 4. The Boring Misconfigured Upload
File uploads feel old-school. You test .php — blocked. .exe — blocked. Move on. But upload bugs today are sneaky.
They hide in:
* MIME type confusion * Extension tricks * Image processing * Cloud storage settings * CDN transformations
You're not trying to upload a shell anymore. You're testing the pipeline.
Ask: what happens after upload?
Is the file:
* Resized? * Parsed? * Indexed? * Run through AI? * Publicly cached?
Every step is a new bug waiting to happen.
These days, upload bugs mean:
* Stored XSS in metadata * SSRF through image fetchers * IDOR in storage buckets * RCE in file converters
The bug isn't the upload — it's the journey.
Follow the file, and you'll find the gold.
— -
🍏 5. The Ignored "Minor" Info Leak
This one gets overlooked the most. It doesn't look like a bug — it just looks like noise. A stack trace. A version header. Debug info. An internal hostname. So people skip it.
But info leaks start chains.
They answer:
* What framework is this? * Which version? * How are things named inside? * Are there hidden environments? * Any legacy stuff running?
Attackers don't use leaks directly. They use them to remove randomness.
Lose the randomness, and suddenly:
Blind attacks work every time. Fuzzing gets focused. Attack chains appear out of nowhere.
Information leaks don't deliver impact by themselves. But they speed everything up.
And speed gets you paid.
— -
Why Low-Hanging Bugs Matter More Than You Think
Because real life isn't a movie.
Most compromises don't begin with some genius-level exploit. They start with: Small misses. Trust in the wrong place. And the bugs everyone else thought were too boring.
How to Chain Low-Hanging Fruits Like a Pro
Think in layers. Not bugs. Layers.
Layer 1 — Discovery A small info leak reveals structure.
Layer 2 — Access An IDOR exposes relationships.
Layer 3 Trust Abuse A redirect manipulates flows.
Layer 4 Payload Delivery An upload carries execution.
Individually: low. Together: catastrophic. Chaining is not luck. It's patience plus pattern recognition
Final Thoughts
If you're new — Master these first. If you're experienced — Return to them. If you feel stuck — Slow down and revisit the basics. Because the difference between struggling hunters and successful ones is rarely knowledge. It's attention. And attention turns low-hanging fruit into career-defining wins. Thanks , Hope You Learn Somethings this writeup.