Before you probe anything, you need to know what you're looking at. Here's a repeatable, technology-aware methodology — from passive header inspection to a confirmed proof-of-concept.
Scope notice: All techniques described here are for authorized security testing only — bug bounty programs, CTFs, penetration tests with written permission, or your own controlled lab environments. Unauthorized testing is illegal and unethical. Always test within the defined scope of your engagement.
Introduction
Every successful security test begins with the same question: what am I looking at?
Before you can probe a target meaningfully, you need to know what technology it runs — its web server, its language, its framework, its plugins. That identification process is called fingerprinting, and it cascades directly into every attack decision you make after.
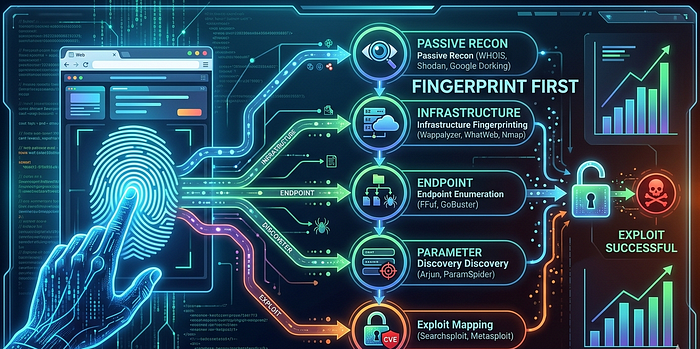
This article walks through a structured, repeatable methodology: fingerprint first, then map the detected technology to its known vulnerability classes, then prioritize which parameters to test and why. The framework is organized into eight parts — from passive header inspection all the way to a full recon-to-exploit workflow.

Part A — Target Fingerprinting: Knowing What You're Up Against
Fingerprinting happens in two phases. The first is passive — you learn what you can from normal responses without triggering anything unusual. The second is active — you send deliberate, minimal requests to provoke identifying behavior.
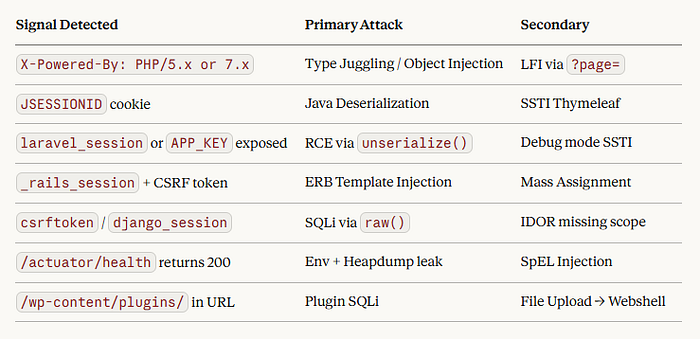
Passive Fingerprinting — HTTP Headers and URL Patterns
A single curl -sI command against a target reveals an extraordinary amount. Response headers are designed for browsers, not for hiding information, so servers routinely broadcast their identity in plain text:
# Step 1: read the headers
curl -sI https://target.com | grep -i 'server\|x-powered\|x-generator\|set-cookie'
# Common signals and what they reveal
Server: Apache/2.4.41 (Ubuntu) → Apache on Ubuntu Linux
X-Powered-By: PHP/7.4.3 → exact PHP version
X-Powered-By: Express → Node.js + Express
Set-Cookie: PHPSESSID=xxx → PHP
Set-Cookie: JSESSIONID=xxx → Java (Spring/Struts/Tomcat)
Set-Cookie: laravel_session=xxx → Laravel (PHP)
Set-Cookie: _rails_session=xxx → Ruby on Rails
Set-Cookie: csrftoken=xxx → Django (Python)
X-Generator: Drupal 9 → Drupal CMSURL patterns add another layer. A path containing /wp-content/plugins/ tells you WordPress immediately. /_next/static/ points to Next.js. /actuator/health screams Spring Boot and is worth checking even before you do anything else.
Active Fingerprinting — Error Pages and File Probing
Requesting a page that doesn't exist is one of the most information-rich things you can do early in a test. Different frameworks return distinctive error messages:
# Trigger a 404 and read the response carefully
curl https://target.com/nonexistent-page-xyz
Whitelabel Error Page → Spring Boot (Java)
DoesNotExist at / → Django (Python)
Whoops! There was an error → Laravel (PHP)
ActionController::RoutingError → Ruby on Rails
Cannot GET /xyz → Node.js ExpressThen probe for high-value files that each stack commonly exposes:
# High-priority file probes (check all of these)
curl -s https://target.com/.env # PHP/Node credential leak
curl -s https://target.com/actuator/env # Spring Boot env dump
curl -s https://target.com/phpinfo.php # PHP info page
curl -s https://target.com/web.config # IIS/.NET config
curl -s https://target.com/graphql # GraphQL endpoint checkCritical: A
.envfile returning HTTP 200 is not a misconfiguration — it is a critical vulnerability. Stop, document it, and report immediately.

Part B — From Fingerprint to Attack: The Decision Matrix
Once you have a fingerprint, the attack class follows almost automatically. This is the core of the methodology — not guessing, but mapping:

Part C — Backend Framework Attack Map
Each framework has a distinct fingerprint and a predictable set of vulnerability classes that stem from how it handles user input.
Django (Python)
Detection Signatures:
- Cookies:
csrftokenordjango_session - Error Pages: "DoesNotExist at /path"
- Default admin interface at
/admin/
Critical Vulnerabilities:
🚨 /admin/ login page publicly accessible
⚠️ DEBUG=True exposing detailed error pages
⚠️ settings.py visible in exposed repositoriesDjango's ORM is safe by default — but developers frequently bypass it using .raw() or direct cursor calls, both of which are vulnerable to SQL injection when user input is interpolated. Template tag injection via Jinja2 is another common finding, as is IDOR caused by missing filter_by(owner=request.user) checks on querysets.
Ruby on Rails
Detection Signatures:
- Cookie:
_rails_session - URL Pattern:
/resources/:id(RESTful routing) - Error Pages:
ActionController::RoutingError
Critical Vulnerability:
⚠️ Exposed .git folder with Gemfile.lock publicly accessiblRails' greatest historical weakness is mass assignment — passing untrusted params directly into model constructors. Modern Rails mitigates this with strong parameters, but developers frequently whitelist too broadly. ERB template injection and .where()-based SQL concatenation round out the top three findings.
Laravel (PHP)
Detection Signatures:
- Cookie:
laravel_session - Error Messages: "Whoops! There was an error"
- Debug pages with orange styling
Critical Vulnerability:
🚨 .env file publicly accessibleIf you find a Laravel application with APP_DEBUG=true and APP_KEY exposed, the path to forging signed session cookies is straightforward. PHP object injection via unserialize() remains prevalent, and the Blade template engine's {!! $userInput !!} syntax renders raw HTML — a frequent XSS and SSTI source.
Spring Boot (Java)
Detection Signatures:
- Cookie:
JSESSIONID - Server Header:
Apache-Coyote - Error: "Whitelabel Error Page"
Critical Vulnerability:
⚠️ /actuator/health endpoint publicly accessibleSpring Boot's Actuator endpoints are the highest-priority finding in any Java application. /actuator/env can expose every environment variable — database passwords, cloud credentials, API keys — in a single unauthenticated GET request. /actuator/heapdump downloads the entire JVM heap, from which secrets can be extracted with tools like jmap and grep.
Express.js (Node.js)
Detection Signatures:
- Header:
X-Powered-By: Express - Cookie:
connect.sid - Error: "Cannot GET /route"
Critical Vulnerability:
⚠️ package.json accessible at rootPrototype pollution is the defining vulnerability class for Node.js applications that use deep-merge libraries like lodash.merge or _.merge on untrusted request bodies. MongoDB's $where and $gt operators enable NoSQL injection via JSON body parameters. Template engines — Pug, EJS, Handlebars — are all vulnerable when user input reaches the template string directly.
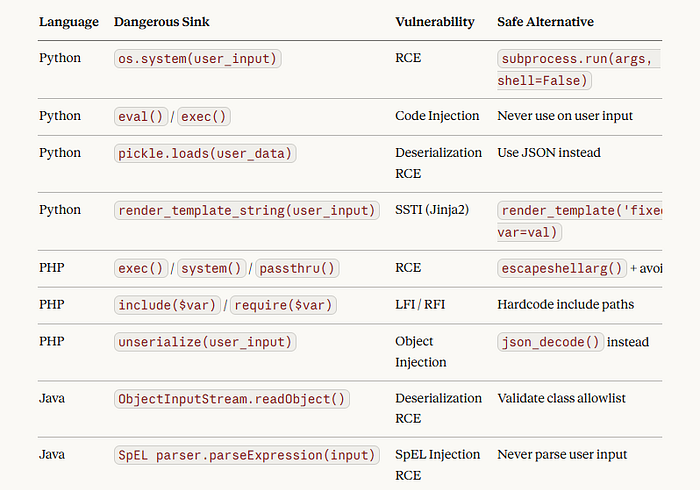
Part D — Language-Level Dangerous Sinks
Regardless of the framework, vulnerabilities ultimately live in specific function calls — sinks where user-controlled data reaches an unsafe operation.

Part E — Parameter Names as Attack Signals
Parameter names are not arbitrary — developers name parameters after what they do. This means the name itself tells you what class of attack to try first.


Part F — CMS and Plugin Attack Map
WordPress
WordPress itself is relatively secure — the risk lives almost entirely in plugins. The /xmlrpc.php endpoint is enabled by default and supports brute-force attacks and SSRF. Check /?author=1 to enumerate usernames. The WPScan Vulnerability Database is the authoritative source for plugin CVEs.
Metabase — CVE-2023–38646 (Pre-Auth RCE)
Critical: If
/api/session/propertiesreturns asetup-tokenwithout authentication, the application is vulnerable to CVE-2023-38646 — a pre-authentication remote code execution via a malicious JDBC connection string. This was actively exploited in the wild in 2023.
Grafana — CVE-2021–43798 (Path Traversal LFI)
Grafana versions before 8.3.0 contain a directory traversal vulnerability via the plugin endpoint. The classic proof-of-concept reads /etc/passwd directly:
GET /public/plugins/../../../../../../../../../../../etc/passwdStrapi — CVE-2023–22621 (SSTI → RCE)
A template injection in Strapi's email templating engine allows an authenticated admin to achieve remote code execution. Check whether admin registration is open at /auth/local/register before assuming authentication is required.
Jenkins
If the Script Console at /script is accessible without authentication, arbitrary Groovy code execution is immediate. Even with authentication, CSRF token bypass vulnerabilities in older versions allow cross-site request forgery to trigger builds and execute code.
Part G — Error Messages as Fingerprints
Error messages are some of the richest sources of technology intelligence available. A properly configured production application should return a generic error page — anything more specific is a finding in itself.

Debug mode deserves special mention. When a framework runs in debug mode in production, it typically exposes file paths, database credentials, secret keys, and full stack traces. Finding SECRET_KEY in a Django debug trace, or APP_KEY in a Laravel Whoops page, allows an attacker to forge signed session cookies — which is effectively full account takeover for any user on the platform.
Part H — The Full Recon-to-Exploit Workflow
Phase 1 — Passive Reconnaissance (zero requests to target)
Use subfinder, httpx, gau, and waybackurls to collect subdomains, live hosts, technology signals, and historical parameter lists without touching the target directly.
Phase 2 — Fingerprint (minimal, careful requests)
Read headers with curl -sI. Request a non-existent page to trigger an error. Check /.env, /actuator/env, and /api/session/properties for immediate critical leaks.
Phase 3 — Parameter Analysis
Sort all collected parameters by name. Group by attack class:
url/dest/redirect→ SSRF firstid/user_id→ IDORsearch/q→ SQLitemplate/name/format→ SSTIfile/path/include→ LFI
Phase 4 — Technology-Specific Attack
Execute the highest-priority attack for the identified stack. PHP + ?page= → LFI. Django + search= → SQLi. Spring Boot actuator → env dump. WordPress xmlrpc.php → SSRF probe.
Phase 5 — Confirm and Escalate
Confirm with a minimal, non-destructive proof-of-concept. Document: screenshot the request and response, write a curl one-liner that reproduces it. Then escalate: SSRF → RCE, SQLi → data dump, IDOR → account takeover chain.
bash
# PHASE 1 — Passive
subfinder -d target.com | httpx -title -tech-detect -server -o live.txt
gau target.com | grep '?.*=' | sort -u > params.txt
# PHASE 2 — Fingerprint
curl -sI target.com | grep -iE 'server|powered|cookie|generator'
curl -s target.com/.env
curl -s target.com/actuator/env
# PHASE 3 — Parameter triage
cat params.txt | grep -E '(url|dest|redirect)=' # SSRF candidates
cat params.txt | grep -E '(id|user_id|doc_id)=' # IDOR candidates
cat params.txt | grep -E '(template|name|format)=' # SSTI candidates
# PHASE 4 — Attack
# FOUND url= param → url=http://169.254.169.254/latest/meta-data/
# FOUND ?page= on PHP → page=../../../etc/passwd
# FOUND Spring actuator → GET /actuator/envConclusion
This methodology is not about memorizing exploits. It is about building a mental model of how technology stacks behave, where they expose themselves, and what their developers commonly get wrong.
The faster you can move from "I see a cookie named _rails_session" to "I should test for ERB injection and mass assignment," the more effective your testing becomes — and the more value you deliver in any authorized engagement.