Hey Hunters!
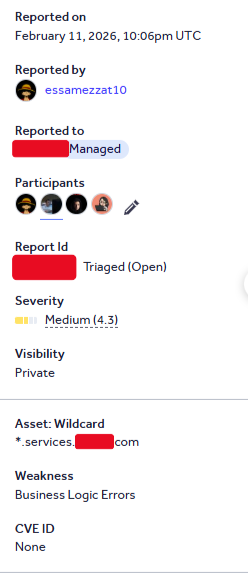
What are Business Logic Vulnerabilities?
Business logic vulnerabilities arise from how an application is designed to function, rather than from low-level technical flaws.
In simple terms, they occur when an application does not properly enforce its own rules, allowing an attacker to achieve unintended behavior using legitimate functionality. As a result, normal features can be manipulated in ways the system never intended.
These issues usually occur because the application fails to handle unexpected scenarios or edge cases securely.
1. Initial Discovery: Hitting the Paywall
While starting my hunt on the program, I explored the available features.
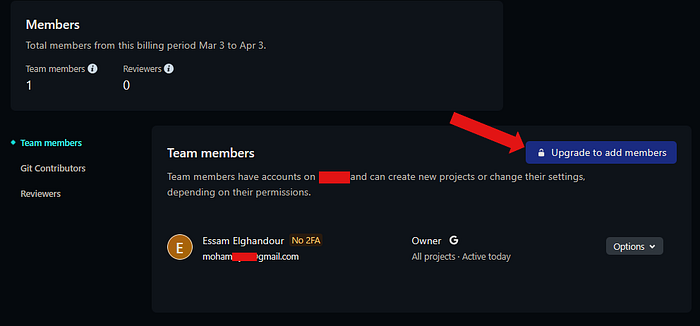
At one point, I had a team and wanted to add another user to test different scenarios and vulnerabilities. However, I quickly noticed a restriction: the application prevented me from inviting users on the Free plan.
In other words:
As a Free plan user, I was the only member in the team. Adding others was not allowed. To invite someone, upgrading to a paid plan such as Pro was required.
2. Identifying the Business Rule
This immediately highlighted a clear business rule:
"You cannot invite users unless you upgrade your subscription."
Instead of accepting this limitation, I questioned:
Is this restriction enforced on the backend, or is it just a UI limitation?
3. Under the Hood: Investigating the Request
I intercepted the request responsible for sending team invitations and noticed it included multiple parameters: an `id`, an `email`, and a role-related value defining the type of invited user.
Initially, I modified only the email to one I control. The request failed because the id`parameter seemed mandatory, and I didn't have a valid one.

4. Breaking the Assumption: The Power of Omission
Rather than providing a valid `id`, I decided to remove it entirely and observe the backend's behavior.
I modified the request body as follows:

After sending this request, the server accepted it successfully, proving that the `id` was not strictly required and that the backend was not validating the request structure properly.
This was a key turning point.
5. Confirming the Bypass
To validate further, I invited another user using the same modified request.
The server responded with:
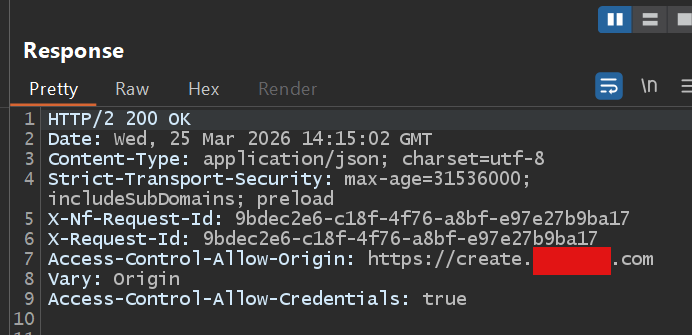
This confirmed that the backend accepted the request, even though Free plan users should not be able to perform this action. The restriction was clearly only enforced on the client side.
6. Verifying the Impact: Extracting the Token
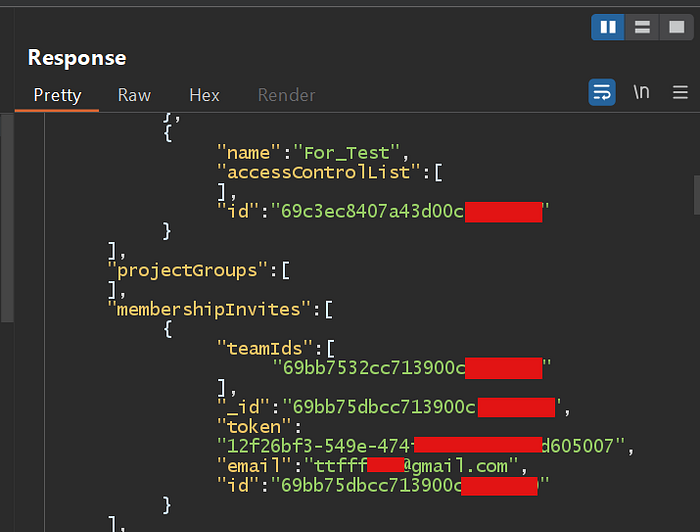
Inspecting the application responses, I found that the invitation was indeed created.
Surprisingly, the response also included:
- An invitation ID
- A valid invite token
7. The Final Result
This confirmed that the backend fully processed the request and generated a legitimate invitation.
It was clear that:
The application was generating valid invitation tokens for Free plan users, despite the intended restriction.
This is a complete Business Logic Bypass, allowing restricted functionality without meeting the required conditions.
Conclusion
The root cause of this issue is the lack of server-side validation for subscription-based restrictions.
By relying on client-side enforcement, the application allows attackers to bypass intended business rules by directly interacting with backend APIs.
Great work with my bro : Belal
الْحَمْدُ للّهِ رَبِّ الْعَالَمِينَ
In the end, I hope this write-up inspires careful thinking and curiosity, reminding us that understanding how systems work is just as important as finding vulnerabilities.

