💰 How I Earned $200 in 5 Minutes Using a Simple Broken Link Hijacking Bug
Most beginners think bug bounty rewards come from complex vulnerabilities.
But in reality, some of the easiest money comes from:
👉 Simple bugs that others ignore
This is a practical, real-style walkthrough of how a $200 bug can be found in minutes using Broken Link Hijacking — including social media and subdomain checks that most people miss.
---
🎯 Target Selection
Instead of large, crowded programs, I chose:
- A mid-sized company - Active website with blog and footer links - Public bug bounty program
👉 Less competition = faster results
---
🔍 Step 1: Quick Recon (2 Minutes)
I opened the website and focused only on:
- Footer - Contact page - Blog posts - Social media icons
No tools. Just manual observation.
---
💣 Step 2: Finding the Broken Link
In the footer, I found:
<a href="https://old-support-service.com">Support</a>
When I clicked:
👉 ❌ "This site can't be reached"
---
⚡ Step 3: Check Domain Availability
I searched:
👉 "old-support-service.com"
💥 Result: Available for registration
---
🔥 Step 4: Take Control (Proof of Concept)
I registered the domain (low cost).
Then hosted a simple page:
<h2>PoC - Security Research</h2> <p>This domain is controlled for security testing</p>
---
💥 Step 5: Verify the Impact
- Go back to target website - Click "Support"
👉 It now opens my controlled page
---
🔗 Bonus Checks (What Most Hunters Miss)
After this, I continued checking two more areas:
---
🔍 1. Social Media Links
I checked links like:
<a href="https://twitter.com/company_support">Twitter</a>
Result:
👉 ❌ Account does not exist
💥 I could create the same username
👉 This allows:
- Brand impersonation - Fake support messages - Phishing attacks
---
🔍 2. Subdomain Check (Advanced but Easy)
I found a subdomain:
support.target.com
It was not loading properly.
After checking DNS:
👉 It pointed to an unused service
💥 Possible subdomain takeover
---
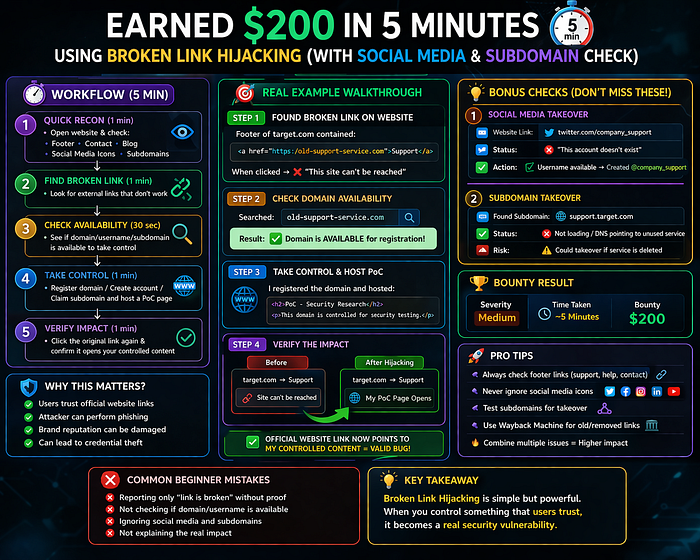
🚨 Why These Checks Matter
Most beginners stop at one bug.
Top hunters think:
👉 "What else can I take control of?"
Because combining issues increases impact:
- Broken link → external control - Social media → user trust - Subdomain → full domain authority
👉 Together = stronger report
---
🧠 Why This Was Accepted
Because:
- Official website pointed to attacker-controlled resource - Clear user trust impact - Demonstrated real exploitation
---
💰 Result
- Severity: Medium - Bounty: $200 - Time taken: ~5 minutes to find (core bug)
---
⚡ Pro Tips
- Always check footer links 🔥
- Never ignore social media icons
- Look for: - support - help - contact
- Test subdomains for takeover
- Think beyond one bug
---
❌ Beginner Mistakes
- Only checking main pages - Ignoring social links - Not testing subdomains - Reporting without proof
---
🏁 Final Thoughts
This bug proves:
👉 You don't need advanced exploits to earn money
You need:
- Observation - Curiosity - Execution
Because:
👉 Easy bugs exist everywhere — most people just don't see them
---
🔥 Action Plan
Try this today:
1. Open any website 2. Check footer links 3. Check social media links 4. Look for subdomains 5. Test everything
---
💬 One simple check can earn you your first $200.
🚀 Start now. Stay consistent. Results will follow.
