Most beginners think Open Redirect is a low-impact vulnerability. Many even skip testing for it.
But experienced bug bounty hunters know something different.
When discovered in the right context, Open Redirect can lead to $100–$500+ payouts — sometimes even more.
The trick isn't just finding an Open Redirect.
The real skill is:
- Finding it in high-value locations
- Demonstrating real security impact
- Writing a strong bug bounty report
In this guide, you'll learn exactly how bug hunters find and exploit Open Redirect vulnerabilities in real applications.
In this article you'll learn:
- 🔓 What an Open Redirect vulnerability is
- 🔎 How hackers find Open Redirects in real targets
- 🧪 Practical testing techniques
- 💰 How to turn a low severity bug into a $500 bounty
- 📝 How to write a strong vulnerability report
Let's start hunting. 🔎
🔓 What is an Open Redirect Vulnerability?
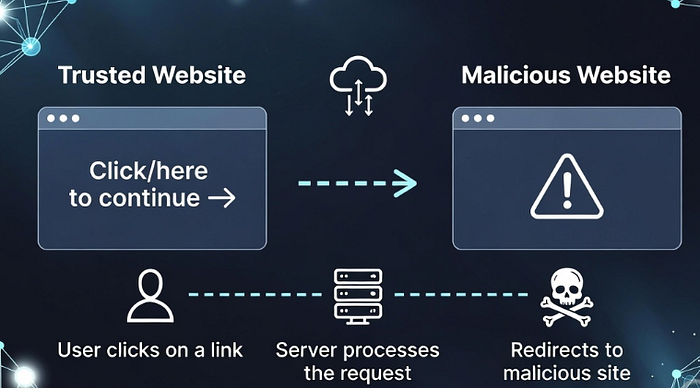
An Open Redirect occurs when a website allows users to control the redirect destination without proper validation.
This means an attacker can create a link that appears to belong to a trusted website, but actually redirects users to a malicious site.
Example:
https://example.com/redirect?url=https://malicious-site.comA victim sees the domain example.com and trusts it.
But after clicking the link, they are redirected to:
https://malicious-site.comThis vulnerability can be abused for several attacks, including:
- 🎣 Phishing attacks
- 🔑 Token theft
- 🔓 OAuth account takeover
- 🦠 Malware distribution
Because these attacks exploit trusted domains, many bug bounty programs still reward Open Redirect reports.

🎯 Why Bug Hunters Still Earn Money From Open Redirect
Many beginners ignore Open Redirect because platforms often mark it as low severity.
However, experienced hunters know that context changes everything.
Open Redirect becomes far more dangerous when combined with:
- OAuth authentication
- Password reset flows
- Login redirects
- SSO systems
- Trusted domains in email links
In these scenarios, an Open Redirect can become a serious security risk.
That's why some reports still earn $300–$500+ bounties.
🔎 Step 1 — Finding Redirect Parameters
The first step in discovering Open Redirect vulnerabilities is identifying parameters that control redirection.
Common redirect parameters include:
redirect
url
next
return
returnUrl
continue
dest
destination
redir
redirect_uri
callbackExample URLs you might encounter:
https://target.com/login?next=/dashboard
https://target.com/redirect?url=https://google.com
https://target.com/auth?redirect_uri=https://example.comWhenever you see these parameters, it's a strong signal that redirection may be happening internally.
These are perfect candidates for Open Redirect testing.

🕵️ Step 2 — Discovering Endpoints Using Google Dorking
Search engines can also reveal redirect endpoints.
Bug hunters often use Google Dorks to discover them.
Examples:
site:target.com inurl:redirect
site:target.com inurl:returnUrl
site:target.com inurl:url=
site:target.com inurl:redirect_uriThese search queries help uncover hidden redirect parameters across a target domain.
Sometimes you'll find endpoints that developers forgot to secure.
⚡ Step 3 — Testing the Redirect
Once you discover a redirect parameter, the next step is testing how it behaves.
Example test URL:
https://target.com/redirect?url=https://google.comIf the website redirects you to Google, the parameter is controlling the redirect.
Now replace the value with your own domain:
https://target.com/redirect?url=https://evil.comIf the website redirects to evil.com, congratulations — you may have discovered an Open Redirect vulnerability.
🧪 Step 4 — Bypassing Weak Filters
Some applications attempt to block external redirects.
However, poorly implemented filters can often be bypassed.

Here are some common payload techniques.
1️⃣ Double Slash Bypass
https://target.com/redirect?url=//evil.com2️⃣ Encoded URL
https://target.com/redirect?url=https%3A%2F%2Fevil.com3️⃣ Mixed Format Trick
https://target.com/redirect?url=https://target.com@evil.com4️⃣ Backslash Technique
https://target.com/redirect?url=https:\\evil.comMany real-world vulnerabilities are discovered using simple bypass tricks like these.

💰 Turning an Open Redirect Into a $500 Bug Bounty
Simply reporting:
"Open redirect exists."
is unlikely to earn a bounty.
Instead, you need to demonstrate real-world impact.
Here are some powerful attack scenarios.
🎣 Phishing Attacks
Attackers can create malicious links that appear to come from a trusted domain.
Example:
https://trustedsite.com/redirect?url=https://fake-login.comVictims trust the link and unknowingly enter their credentials.
This increases the severity of the vulnerability.
🔑 OAuth Token Theft
OAuth systems often rely on redirect URLs during authentication.
Example:
https://auth.target.com/login?redirect_uri=https://evil.comIf the redirect is not properly validated, attackers could capture authentication tokens.
This dramatically increases the security impact.
📧 Password Reset Abuse
If password reset workflows include redirect parameters, attackers could:
- Redirect victims to fake password reset pages
- Perform credential harvesting attacks
This scenario can significantly increase bounty payouts.
🧰 Tools That Help Discover Open Redirects
Professional bug bounty hunters rely on tools to speed up reconnaissance.
Popular tools include:
- 🛠 Burp Suite
- 🕷 ParamSpider
- 🔎 Arjun
- 📂 Wayback URLs
- 🕸 Katana crawler
These tools help you discover hidden parameters and endpoints quickly.
📋 Writing a Strong Bug Bounty Report
A well-written report increases the chance of getting rewarded.
Example structure:
Title
Open Redirect via redirect_uri parameterSteps to Reproduce
- Visit the vulnerable endpoint
- Modify the redirect parameter
- Observe redirection to an external domain
Proof of Concept
https://target.com/redirect?url=https://evil.comImpact
Explain how the vulnerability could enable:
- Phishing attacks
- OAuth token theft
- Credential harvesting
Clear impact explanations often lead to higher bounty rewards.
🚀 Pro Tips From Bug Bounty Hunters
Experienced hunters recommend always checking:
✔ Login and logout pages ✔ OAuth authentication flows ✔ Email verification links ✔ Marketing redirect links ✔ Mobile application deep links
These areas frequently contain Open Redirect vulnerabilities.
🎯 Final Thoughts
Open Redirect is one of the most underestimated vulnerabilities in bug bounty hunting.
While many hunters ignore it, those who understand how to demonstrate real impact can turn a simple bug into a $500+ payout.
Remember the process:
🔎 Find redirect parameters 🧪 Test them carefully ⚡ Demonstrate real attack scenarios
That's how vulnerabilities turn into bug bounty rewards.
📢 Want to Learn More About Bug Bounty Hunting?
If you're interested in learning practical ethical hacking techniques, vulnerability hunting, and real bug bounty strategies:
👉 Join our Telegram for daily cybersecurity tips 👉 Visit our website for in-depth hacking guides
Stay curious. Stay ethical. And keep hunting. 🐞
