It's not doing anything dramatic. It's not screaming alerts or crashing systems. Every 60 seconds — quietly, obediently it reaches out across the internet to a server the attacker controls. It asks one simple question:
"Any instructions for me?"
Sometimes the answer is nothing. Sometimes the answer is: "Steal those files. Move to that machine. Stay hidden."
This is Command and Control — the nervous system of a modern cyberattack. And understanding it is one of the most important things you can do as someone entering the security field, whether you're planning to be the attacker in an authorized red team exercise, or the defender trying to catch one.
Let's build the mental model from the ground up.
First: Why Does C2 Even Exist?

Think about how a military operation works. You don't just send soldiers into a city and hope they figure it out. You establish a command post. You maintain radio contact. You issue orders, receive intelligence, and adapt your strategy in real time.
A C2 framework is exactly that — a command post for a cyberattack.
Without C2, an attacker who successfully compromises a machine has a one-time opportunity. They get in, do whatever they can manually, and leave. It's messy, limited, and easy to detect.
With C2, the attacker has persistent, controllable, scalable access. They can:
- Return to the compromised system at any time
- Issue commands without ever touching the machine directly again
- Spread laterally through a network systematically
- Exfiltrate data in slow, quiet trickles designed to avoid detection
- Manage dozens — or thousands — of compromised machines simultaneously from a single dashboard
This is why C2 frameworks exist. Not just as attack tools, but as simulation platforms — because if you're defending a network, you need to understand exactly how this infrastructure operates. You can't hunt what you don't understand.
The Three-Part Architecture: Server, Agent, Client
Before we get into tools, you need to understand the core anatomy. Every C2 framework — commercial or open source, simple or sophisticated — is built on three components.
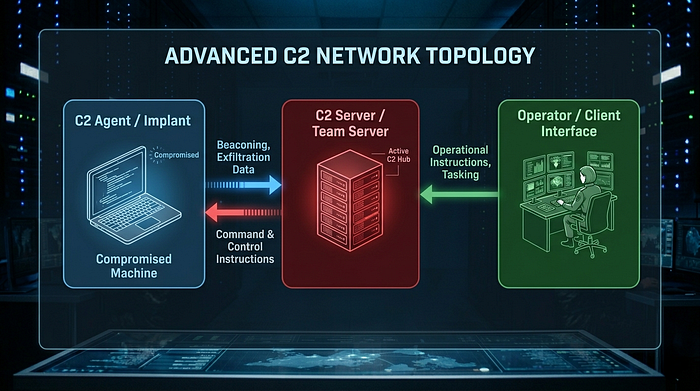
The C2 Agent (Implant or Beacon) This is the software that lives on the victim's machine after compromise. It's designed to be small, stealthy, and persistent. Its primary job is to "beacon" — check in with the server at regular intervals to ask for instructions. A good agent does this quietly, disguising its traffic as something normal (web browsing, DNS queries, etc.).
The C2 Server (Team Server) This is the attacker's central brain. It receives check-ins from all deployed agents, stores stolen data and logs, and queues commands for the next beacon cycle. In red team operations, this is what the whole operation runs on.
The C2 Client (Operator Interface) This is the human-facing dashboard. The red team operator sits here, sees all connected agents, and issues commands. In frameworks like Cobalt Strike, this is a rich GUI. In others, it's a web interface or terminal. This is the "war room" the operator never leaves.
Understanding this triangle — Agent ↔ Server ↔ Operator — is the foundation of everything else.
The Open Source C2 Landscape: Every Major Tool Explained

Here is every major open-source C2 framework a beginner should know, what it does, and when you'd realistically use it.
1. Sliver
What it is: One of the most widely adopted open-source C2 frameworks available today, developed by the Bishop Fox security firm and written entirely in Go.
Why it matters: Sliver supports multiple communication protocols — mTLS (mutual TLS), HTTP/S, DNS, and WireGuard — meaning it can disguise its traffic in multiple ways depending on what the target environment blocks or monitors. It generates unique implants per operation, making signature-based detection harder.
Use case: A red team engagement against a mature enterprise with a well-tuned firewall and EDR. You need protocol flexibility and implants that don't share signatures across operations. Sliver gives you both.
Who should learn it first: Anyone serious about red teaming who doesn't have access to commercial tools. It's the closest open-source equivalent to Cobalt Strike in terms of capability.
2. Havoc
What it is: A modern, free, open-source C2 framework built specifically with evasion as its primary design goal.
Why it matters: Havoc's "Demon" agent is designed with modern EDR bypass techniques baked in — sleep obfuscation, stack spoofing, indirect syscalls. In plain terms: it's built to hide from the endpoint detection tools that modern enterprises rely on.
Use case: Engagements where the target has a well-deployed EDR solution (CrowdStrike, SentinelOne, Microsoft Defender for Endpoint). Havoc is designed specifically to operate in those environments without immediate flagging.
Who should learn it: Intermediate to advanced red teamers who want to understand modern evasion techniques. Not ideal as a first C2 — understand the basics before you learn to hide them.
3. Mythic
What it is: An open-source, multi-agent, multi-operator C2 framework with a web-based interface, designed for maximum flexibility and operational visibility.
Why it matters: Mythic is modular by design. The framework itself is just a container — you plug in different agents (written in any language, for any platform) and different C2 profiles (communication channels) as separate components. It also has excellent logging, which makes it valuable for training and tracking what happened during an operation.
Use case: Large red team operations with multiple operators working simultaneously. Also excellent for training and research because its logging gives you a detailed view of every action taken during a simulated attack.
Who should learn it: Red teamers who want to build custom agents, security researchers studying C2 internals, and teams running complex multi-operator engagements.
4. PowerShell Empire (Empire)
What it is: One of the original post-exploitation frameworks, built around PowerShell — Windows' native scripting language. Now maintained by BC Security, it also supports Python and C# agents.
Why it matters: Because PowerShell is built into Windows, Empire agents can operate in "living off the land" mode — they don't need to drop suspicious executable files. They run entirely in memory using tools that are already present on the target system.
Use case: Windows-heavy enterprise environments where deploying a traditional executable would immediately trigger alerts. Empire lets you abuse legitimate system functionality as your attack channel.
Who should learn it: Anyone studying Windows post-exploitation specifically, or preparing for certifications like OSCP that cover PowerShell-based attack techniques heavily.
5. Covenant
What it is: A .NET-based, collaborative C2 framework with a clean web-based GUI, designed to make red team operations more accessible and trackable.
Why it matters: Covenant's "Grunt" agents are written in C# and run on the .NET framework — which again means leveraging legitimate, trusted software already present on Windows systems. Its GUI is one of the most beginner-friendly among serious C2 frameworks.
Use case: Red teams that want strong operational documentation built into the platform. Covenant logs interactions clearly, making post-engagement reporting significantly easier. Also good for teams new to C2 operations who need a navigable interface.
Who should learn it: Beginners transitioning into red teaming who want a serious tool with a less intimidating learning curve.
6. Merlin
What it is: A cross-platform C2 framework designed specifically around HTTP/2 and HTTP/3 protocols.
Why it matters: Most network monitoring tools and firewalls are tuned to inspect HTTP/1.1 traffic. HTTP/2 and HTTP/3 traffic is multiplexed and encrypted differently — many older detection tools either can't inspect it properly or don't flag it at all. Merlin exploits this blind spot.
Use case: Environments with strong perimeter filtering of standard HTTP/S traffic, where HTTP/2's multiplexing provides a less-monitored communication channel.
Who should learn it: Security researchers studying protocol-level evasion, and red teamers who want to understand how protocol choice affects detection.
7. PoshC2
What it is: A proxy-aware, Python-based C2 framework aimed primarily at penetration testers and post-exploitation workflows.
Why it matters: PoshC2 is built specifically with proxy environments in mind — it can route its traffic through corporate web proxies, which many organizations use for outbound internet access, making its traffic blend in with normal employee browsing.
Use case: Engagements inside corporate networks where all outbound traffic routes through a proxy. Many C2 frameworks struggle in these environments; PoshC2 is designed for them.
Who should learn it: Penetration testers focused on internal network assessments where proxy traversal is a common obstacle.
8. Metasploit Framework
What it is: The foundational open-source penetration testing platform that nearly every security professional learns first. While not a dedicated C2 framework, its Meterpreter payload functions as a capable C2 agent.
Why it matters: Metasploit is the universal starting point. It contains thousands of exploits, payloads, and auxiliary modules. Its Meterpreter agent gives you a full post-exploitation channel including file operations, privilege escalation, and lateral movement.
Use case: Initial exploitation and basic post-exploitation in virtually any penetration testing scenario. Also the most documented, most taught, most supported framework in existence.
Who should learn it: Every single person entering offensive security. Non-negotiable. Learn this before you learn anything else on this list.
Key Concepts Every Beginner Must Understand
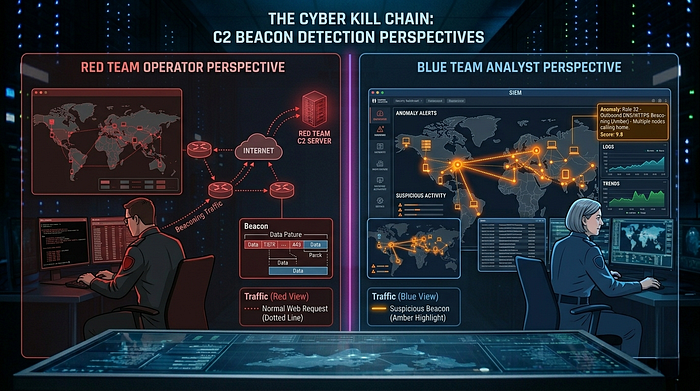
Beaconing and Jitter
A beacon is the heartbeat of a C2 operation. The agent on the compromised machine wakes up at a set interval, connects to the C2 server, asks for instructions, sends back any collected data, and goes quiet again.
The problem with a perfectly regular heartbeat: it's detectable. If your agent checks in exactly every 60 seconds, network monitoring tools will eventually notice the suspicious regularity.
This is why jitter exists. Jitter adds random variation to the beacon interval — instead of checking in at exactly 60 seconds every time, the agent checks in at 47 seconds, then 71 seconds, then 58 seconds. The average is 60, but the pattern is gone. To network monitoring tools, it looks like normal, irregular user traffic.
Living Off the Land (LotL)
"Living off the land" means using tools and software already present on the victim's system to carry out attack actions — rather than introducing new, suspicious files.
PowerShell, WMI (Windows Management Instrumentation), certutil, mshta, regsvr32 — these are all legitimate Windows tools that are also powerful attack primitives. When an attacker uses PowerShell to run an Empire agent instead of dropping a custom executable, they're living off the land. There's no new file for antivirus to flag. The attack runs entirely inside trusted, signed, native processes.
For defenders, this is one of the hardest attack patterns to detect — because the tools making the noise are supposed to be there.
Domain Fronting and Redirectors
Imagine you're an attacker. Your C2 server is at evil-c2.com. If a defender notices your agent's traffic going to evil-c2.com, they block it, and the game is over.
Domain fronting routes your C2 traffic through a trusted third-party service first — often a CDN like Cloudflare or AWS CloudFront. From the outside, the traffic appears to be going to a legitimate, trusted domain. The CDN silently forwards it to your actual C2 server. The defender sees cloudflare.com in the traffic, not evil-c2.com.
Redirectors serve a similar purpose — intermediate servers that forward traffic to the real C2 server, protecting its actual location and IP address.
This is why blocking an IP is rarely enough to stop a sophisticated C2 operation.
DNS Tunneling
DNS is one of the most universally allowed protocols on corporate networks. Even heavily locked-down environments almost always allow DNS queries outbound — because if you block DNS, nothing works.
DNS tunneling exploits this by encoding C2 data inside DNS queries and responses. Instead of asking "what's the IP address of google.com?" your agent asks "what's the IP address of aGVsbG8gd29ybGQ=.evil-domain.com?" — where that long subdomain is actually base64-encoded stolen data or a command response.
The DNS server at evil-domain.com is the C2 server. It reads the encoded data in the query, decodes the command response, and sends it back as a DNS reply.
To most network monitoring tools, this looks like normal DNS traffic.
Fileless Malware
Traditional malware drops a file on disk — an executable, a DLL, a script. Antivirus tools scan files on disk. So attackers stopped writing files to disk.
Fileless malware runs entirely in memory. It's injected into a running legitimate process, executes there, and leaves nothing on the filesystem for a scanner to find. When the machine reboots, it's gone — but by then the damage may already be done.
C2 agents are increasingly fileless. They're injected directly into memory via exploits, weaponized documents, or PowerShell execution chains.
The Defender's Playbook: How Blue Teams Hunt C2
Understanding C2 from the offensive side is only half the equation. Here's how defenders find it:
Network Traffic Analysis — Blue teams look for unusual outbound connections: connections to newly registered domains, connections happening at suspiciously regular intervals, large volumes of DNS queries to single domains (a sign of DNS tunneling), and connections to IPs with no legitimate business association.
RITA (Real-time Internal Threat Analysis) — An open-source tool specifically built to detect beaconing behavior in network logs. It analyzes connection frequency, data size regularity, and destination patterns to mathematically score connections for beacon-like behavior.
Endpoint Detection and Response (EDR) — Modern EDR tools (CrowdStrike, SentinelOne, Microsoft Defender for Endpoint) monitor process behavior at the kernel level. They look for processes making unexpected network connections, PowerShell executing encoded commands, processes injecting into other processes, and memory regions marked as executable that weren't loaded from a file.
SSL/TLS Inspection — Since most C2 traffic is encrypted, defenders need to decrypt and inspect it. Enterprise environments use TLS inspection proxies that act as a man-in-the-middle on outbound encrypted connections, allowing security tools to scan the contents before re-encrypting and forwarding.
Threat Intelligence Feeds — C2 server IPs, domains, and TLS certificate patterns get catalogued and shared across the industry. If an attacker reuses infrastructure, threat intel feeds can match it. Tools like Hunt.io actively track C2 infrastructure across the internet.
Why Red Teams Use C2 Frameworks (The Legitimate Case)

This is the question every beginner should ask — and the answer matters for how you approach learning this material.
Red teams exist because organizations need to know what a real attack against them would look like. Not in theory. In practice.
A red team engagement uses the same tools and techniques as real threat actors — including C2 frameworks — but under a formal, authorized contract with the organization being tested. The red team's job is to:
- Test whether the organization's defenses actually work against modern attack techniques
- Identify gaps in detection before a real attacker does
- Give the blue team something real to practice against
- Generate findings that drive concrete security improvements
Without realistic simulation, you get security theater — organizations spending money on tools they've never verified actually work.
C2 frameworks are the tools that make realistic simulation possible. Cobalt Strike's Beacon behaves like real-world implants used by nation-state threat actors because those actors actually developed the same techniques. Studying these tools is how defenders learn to find them.
This is the core reason every serious security professional — offensive or defensive — needs to understand C2 frameworks. You cannot defend against what you haven't seen. You cannot hunt what you don't understand.
Where to Start If You're Just Entering the Field

If you've read this far and want to start learning hands-on, here's a realistic beginner path:
Start with Metasploit — it's documented to death, has free courses everywhere, and gives you the foundational concepts of exploitation and post-exploitation before you touch anything more specialized.
Build a home lab — two virtual machines on your own computer (one attacker, one victim) gives you a completely legal, safe environment to run every framework on this list. VirtualBox and VMware both have free tiers. Kali Linux as your attacker OS. A Windows 10 VM as your target.
Learn Covenant or Empire next — both have gentler learning curves than Sliver or Havoc, and both will teach you the core concepts of beaconing, listeners, and agents in a navigable way.
Study network traffic alongside the tools — run Wireshark while your C2 agents are beaconing. Watch what the traffic actually looks like. This is the single most important thing you can do to understand both the offensive and defensive sides simultaneously.
Move to Sliver or Havoc once you understand the fundamentals — these are where the modern, sophisticated techniques live, and they'll make much more sense once you have the baseline.
The goal isn't to collect tool knowledge. The goal is to develop a mental model of how post-exploitation infrastructure operates — so whether you're building it or hunting it, you understand what's actually happening.
The Takeaway

C2 frameworks are not inherently evil tools. They're sophisticated infrastructure for maintaining persistent access — and understanding them is non-negotiable for anyone who wants to work at the serious end of cybersecurity.
The attackers already know how this works. Nation-states, ransomware groups, and advanced persistent threat actors have been using this infrastructure for years.
The question is whether the defenders do too.
That's why you're here. That's why this matters.
Written for students entering the security domain who want to understand the real architecture of modern attacks — not the movie version.

