A misconfigured Apache directive just one line can turn your private server filesystem into an open catalogue for anyone with a browser. Here's everything from basics to advanced, so you never need another source on this topic.
Chapter 1: So, What Even Is Directory Listing?
Okay, let's start from zero. Imagine you walk up to someone's house and knock. They open the door but instead of greeting you, they just hand you a complete inventory of every room what's in each drawer, which documents are on the desk, where the spare keys are kept. That's directory listing on a web server.
When you host a website, your files live in a folder on the server. Normally, the web server only serves what you explicitly tell it to the homepage, the images, the API endpoints. But when directory listing is enabled and someone requests a folder that doesn't have an index file (like index.html), the server doesn't return a 403 Forbidden or a 404. Instead, it returns a neat HTML page showing every single file in that directory.
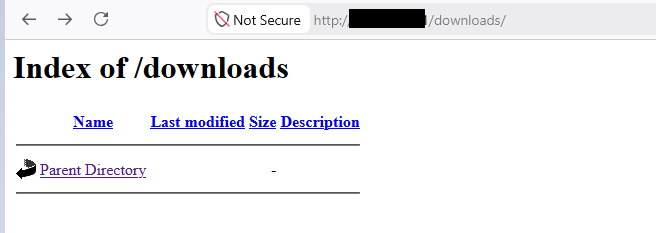
Here's what that actually looks like in a browser:
Index of /uploads
[DIR] ../ [FILE] database_backup_2024.sql 2024–11–12 03:22 48M [FILE] employee_records.xlsx 2024–10–03 14:55 2.1M [FILE] config.php.bak 2024–09–18 09:10 4K [FILE] private_keys.zip 2024–08–22 16:33 12K [FILE] staging_passwords.txt 2024–07–01 11:00 1K
Apache/2.4.52 Server at target-company.com Port 80
Yep. That's what an attacker sees. An open directory is basically a shopping window for your sensitive files. And the scariest part? The server thinks it's being helpful.
Technical Term: Directory listing is also called directory traversal exposure, directory indexing, or directory browsing. In CVE databases and bug bounty reports, it's labeled as CWE-548: Exposure of Information Through Directory Listing.
Chapter 02: Why Does This Happen? Understanding Apache's Brain
To really understand this vulnerability, you need to understand how Apache makes decisions about what to show. Apache has a layered configuration system and the interplay between layers is exactly where things go wrong.
Layer 1: The Global Config (apache2.conf)
This is the master config file that applies to the entire server. Everything here cascades downward unless explicitly overridden. In our finding, this is what was set globally:
# Line 160 — Applies to <Directory /> Options FollowSymLinks
# Line 171 — Applies to /var/www/ Options Indexes FollowSymLinks
# Line 176 — Commented out (has no effect) # Options Indexes FollowSymLinks
Options Indexes tells Apache: "If there's no index file in a directory, generate and display a listing of all files." This is the culprit. A single keyword with massive consequences.
Layer 2: Virtual Host Config
<VirtualHost *:80> ServerName company-internal.prod DocumentRoot /disk1/[redacted]/production/public
<Directory /disk1/[redacted]/production/public> Options Indexes ExecCGI FollowSymLinks # AllowOverride is NOT set here — defaults to None </Directory> </VirtualHost>
Notice ExecCGI sneaking in there too. That allows CGI scripts to execute a separate but equally dangerous misconfiguration. But let's stay focused on Indexes for now.
Layer 3: The .htaccess "Fix" That Does Nothing
Someone on the team knew Indexes was dangerous. So they created a .htaccess file to override it:
# This person tried their best. Unfortunately it does nothing.
RewriteCond %{REQUEST_METHOD} ^(HEAD|PUT|DELETE|TRACE|TRACK|OPTIONS) Options -Indexes
IndexOptions NameWidth=* # Header set X-Frame-Options "SAMEORIGIN" Header set X-Content-Type-Options "nosniff" Options -Indexes should disable directory listing. Should. But here's the thing Apache only reads .htaccess files if AllowOverride is not set to None. And guess what the default is?
The Core Problem: AllowOverride None is the default in modern Apache. When this is set, Apache completely ignores every .htaccess file in every directory. Every security control, every rewrite rule, every header ignored. The .htaccess might as well not exist.
This creates a false sense of security. The developer thinks "I've protected the directory" but the protection is literally invisible to Apache. It's like putting a lock on a door that's already been removed from its frame.
How Apache Processes a Directory Request
Browser requests /uploads/ ↓ Apache checks for index.html ↓ No index.html found ↓ Checks Options → Indexes = ON ↓ Should check .htaccess? → AllowOverride None → SKIP .htaccess entirely ↓ Generate file listing HTML → Send to browser ← VULNERABLE
Shodan & Google Dork Reality: Right now, at this moment, there are hundreds of thousands of servers with directory listing enabled that are indexed by Shodan and accessible via Google dorks. The search intitle:"Index of /" site:*.gov returns real results.
Chapter 3: Server Configuration:
How It Gets Turned On (And Off) Let's go hands-on. Here's a complete picture of how Apache directory listing is configured.
The Options Directive : What Each Keyword Does a) Options IndexesEnables directory listing when no index file exists
b) Options ExecCGIAllows CGI scripts to execute in the directory
c) Options FollowSymLinksApache follows symbolic links can escape web root
d) Options -IndexesExplicitly disables directory listing (minus sign matters)
e) Options NoneDisables all options most restrictive
The AllowOverride Directive -The Gatekeeper a) AllowOverride None.htaccess completely ignored Apache never opens the file
b) AllowOverride All.htaccess fully processed every directive applied
c) AllowOverride OptionsOnly Options directives in .htaccess are processed
d) AllowOverride FileInfo AuthConfigFile handling and auth overrides allowed common for WordPress
Vulnerable Config vs. Secure Config
❌ Vulnerable: apacheOptions Indexes ExecCGI FollowSymLinks # AllowOverride not set (= None by default) # .htaccess fixes silently ignored
✅ Secure: apacheOptions -Indexes -ExecCGI AllowOverride None Require all granted
Full Secure Global Config: apache# /etc/apache2/apache2.conf — Secure defaults
# Deny everything at root level <Directory /> Options -Indexes -ExecCGI AllowOverride None Require all denied </Directory>
# Web root — only what's needed <Directory /var/www/html> Options -Indexes +FollowSymLinks -ExecCGI AllowOverride None Require all granted </Directory>
Full Secure Virtual Host Config: apache<VirtualHost *:443> ServerName company.prod DocumentRoot /disk1/app/production/public
<Directory /disk1/app/production/public> Options -Indexes -ExecCGI -Includes AllowOverride None
Header always set X-Frame-Options "DENY" Header always set X-Content-Type-Options "nosniff" Header always set Referrer-Policy "strict-origin-when-cross-origin"
Require all granted </Directory>
# Block sensitive file types <FilesMatch "\.(env|bak|sql|log|conf|key|pem)$"> Require all denied </FilesMatch> </VirtualHost>
If You Must Use .htaccess: If your application requires .htaccess support (WordPress, Laravel, etc.), you need to explicitly enable it otherwise it does nothing:
<Directory /var/www/wordpress> Options -Indexes # Allow only what the CMS actually needs AllowOverride FileInfo Options Require all granted </Directory>
Now your .htaccess will be read and Options -Indexes inside it will take effect.
Chapter 4: How to Test for Directory Listing
Whether you're doing a pentest, a bug bounty hunt, or auditing your own infrastructure here are the techniques that work, from simple browser checks to advanced bypasses.
Method 1: The Dead Simple Browser Test Navigate to directory paths that likely exist but don't have index.html: https://target.com/images/ https://target.com/uploads/ https://target.com/assets/ https://target.com/files/ https://target.com/backup/ https://target.com/admin/ https://target.com/logs/ https://target.com/tmp/ https://target.com/static/ https://target.com/media/
If you get a page that says "Index of /uploads" with a table of files — you've found it. That simple.
Method 2: Source Code Enumeration View page source on the target. Look for script/link tags: html<script src="/assets/js/bundle.min.js"></script>
Then test the parent directories: GET /assets/js/ → Index of /assets/js ? GET /assets/ → Index of /assets ? GET /assets/img/ → Index of /assets/img ?
Method 3: Google Dorking (Passive Recon) Google has already crawled and indexed many exposed directories: # Generic directory listing pages intitle:"Index of /" site:target.com
# Find exposed backup files intitle:"Index of" "backup" site:target.com
# Find exposed logs intitle:"Index of" "error.log" OR "access.log"
# Find exposed config files intitle:"Index of" ".env" OR "config.php"
# Find exposed SQL dumps intitle:"Index of" ".sql"
Method 4: The Trailing Slash & URL Encoding Bypass Some servers return 403 for a directory path but show the listing with different URL formatting: # Standard request (might get 403) GET /uploads
# Trailing slash triggers different code path GET /uploads/
# URL encoding bypasses GET /uploads%2f GET /%75ploads/ (u encoded as %75) GET /uploads%2F
# Double slash GET //uploads/
# Dot segment GET /uploads/./
# Case variation (on case-insensitive filesystems) GET /Uploads/ GET /UPLOADS/
Method 5: HTTP Method Bypass Some WAF rules block GET requests to directories but forget about other HTTP methods: bash# Standard GET curl -v https://target.com/uploads/
# HEAD method — sometimes bypasses content filters curl -v -X HEAD https://target.com/uploads/
# OPTIONS method curl -v -X OPTIONS https://target.com/uploads/
# POST to a directory curl -v -X POST https://target.com/uploads/ Method 6 — Automation With Tools dirb — classic scanner: bashdirb https://target.com -w -r -o output.txt ffuf — modern fuzzer: bashffuf -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt \ -u https://target.com/FUZZ/ \ -mc 200 \ -t 50
nuclei template-based: bash# Run directory listing template nuclei -u https://target.com -t exposures/configs/directory-listing.yaml
# Bulk scan from target list nuclei -l targets.txt -t exposures/configs/ -severity medium,high Custom bash script: bash#!/bin/bash TARGET=$1 DIRS=("images" "uploads" "backup" "assets" "files" "logs" "tmp" "static" "admin" "media" "config")
echo "[*] Checking $TARGET for directory listing…"
for dir in "${DIRS[@]}"; do BODY=$(curl -s "$TARGET/$dir/" | grep -i "Index of") if [[ ! -z "$BODY" ]]; then echo "[VULNERABLE] $TARGET/$dir/ → Directory listing enabled!" fi done
Method 7: Wayback Machine & Passive Sources bash# Check Wayback Machine for archived directory listings curl "https://web.archive.org/cdx/search/cdx?url=target.com/*&output=text&fl=original&collapse=urlkey" \ | grep "Index of"
# AlienVault OTX passive lookup curl "https://otx.alienvault.com/api/v1/indicators/domain/target.com/url_list"
Chapter 5: What Can an Attacker Do With This? Non-technical stakeholders sometimes hear "directory listing" and think it's a minor cosmetic issue. It is not. Here's exactly what exposure enables, in escalating order of severity.
Step 1: Reconnaissance & Target Profiling File extensions reveal the technology stack. Directory structure reveals app architecture. Naming conventions help guess other paths. Timestamps reveal maintenance windows. All of this before a single exploit is attempted.
Step 2: Sensitive File Harvesting .env files contain database credentials and API keys. .bak and .sql files are database dumps. config.php.old files contain connection strings. Log files reveal internal IPs and usernames.
Step 3: Source Code Exposure Backup copies of PHP/Python/JS files give an attacker white-box visibility into your application. Finding vulnerabilities in your own code is infinitely faster.
Step 4; Authentication Bypass & Privilege Escalation SSH private keys uploaded accidentally. SSL private keys. Session token files. Password hashes from old database dumps. Each of these leads to direct system compromise.
Step 5: Compliance & Legal Exposure If PII is in an exposed directory even accidentally that's a GDPR or HIPAA breach. Regulatory fines don't care that you didn't intend it. The exposure is the violation, not the exploitation.
Real Attack Chain: Directory listing found → db_backup_oct.sql downloaded → Credentials extracted → Credentials reused on SSH → Root access gained. This exact chain has been used in real-world breaches. Each step took minutes, not hours.
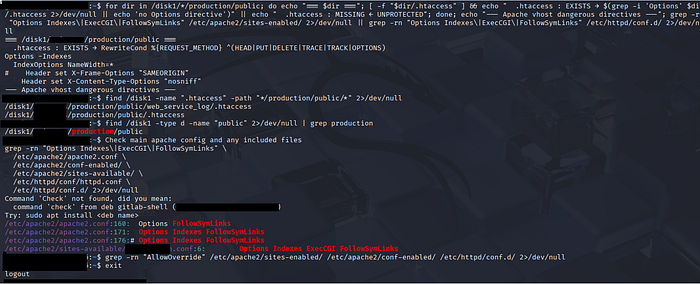
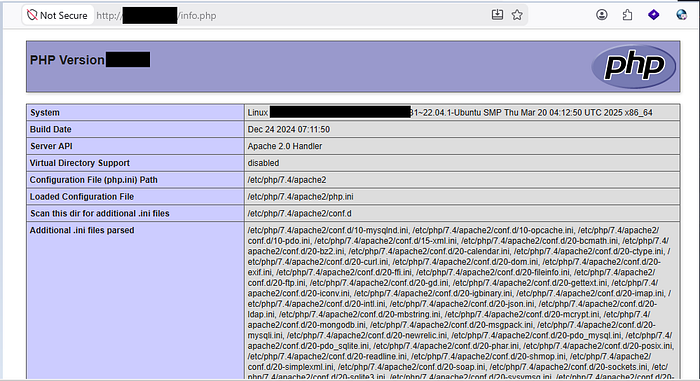
Chapter 6: The Actual Finding, Dissected Line by Line Let's break down exactly what was found and why each piece matters.
Finding Summary:
Type: Apache Directory Listing via Misconfiguration CWE: CWE-548 Exposure of Information Through Directory Listing Severity: High (sensitive production data exposed) Attack Vector: Network (no authentication required) Scope: Multiple production VMs, global and vhost level
Finding #1: Global Config Sets Indexes
apache# apache2.conf:171 Options Indexes FollowSymLinks This single line enables directory listing for the /var/www/ subtree across all virtual hosts. Every VirtualHost that doesn't explicitly override this inherits Indexes. It's a server-wide issue, not isolated to one application.
Finding #2: Virtual Host Amplifies the Problem
apache# sites-available/production.conf:6 Options Indexes ExecCGI FollowSymLinks Not only does the vhost re-enable Indexes, it also adds ExecCGI. If an attacker can upload a file via another vulnerability, they can execute arbitrary code on the server.
Finding #3: .htaccess Protection Is Silent Deadweight
apache# .htaccess file content Options -Indexes ← Correct directive, completely ignored
# Reason: AllowOverride None means Apache never reads this file # This is the most dangerous part false confidence in a non-existent control
Finding #4: Log Directory Exposed bashfind /disk1 -name ".htaccess" -path "*/production/public/*" /disk1/[redacted]/production/public/web_service_log/.htaccess /disk1/[redacted]/production/public/.htaccess The web_service_log/ directory is browseable. Apache access logs contain full request URLs (which can include tokens or session IDs), client IP addresses, user-agent strings, response codes, and timestamps. A gold mine for a follow-up attack.
Chapter 7: Remediation The Complete Fix Guide Here's exactly what needs to happen, step by step.
Step 1: Remove Indexes from Global Config apache# /etc/apache2/apache2.conf
# Change this: Options Indexes FollowSymLinks
# To this: Options -Indexes +FollowSymLinks
# Or better — default deny at root: <Directory /> Options None AllowOverride None </Directory>
Step 2: Fix the Virtual Host Config apache# sites-available/production.conf <Directory /disk1/[app]/production/public> Options -Indexes -ExecCGI +FollowSymLinks AllowOverride None Require all granted </Directory>
# Block log directory entirely <Directory /disk1/[app]/production/public/web_service_log> Require all denied </Directory>
Step 3: Decide on .htaccess Strategy apache# OPTION A If you need .htaccess support (CMS, etc.): <Directory /disk1/[app]/production/public> AllowOverride Options FileInfo ← Now .htaccess Options -Indexes works </Directory>
# OPTION B Recommended for production (no .htaccess): <Directory /disk1/[app]/production/public> Options -Indexes -ExecCGI AllowOverride None ← All controls live here, not in .htaccess </Directory>
Step 4: Block Sensitive File Extensions apache<FilesMatch "\.(env|bak|sql|log|conf|key|pem|old|orig|inc|swp|git|DS_Store)$"> Require all denied </FilesMatch>
# Also deny dot files <FilesMatch "^\."> Require all denied </FilesMatch>
Step 5: Suppress Server Version Info apache# /etc/apache2/apache2.conf ServerTokens Prod ServerSignature Off
Step 6: Verify the Fix bash# Test config syntax apache2ctl configtest
# Reload Apache systemctl reload apache2
# Test from command line curl -I https://your-server.com/uploads/ # Expected: HTTP/1.1 403 Forbidden
# Re-run the same checks that found the issue grep -rn "Options Indexes" /etc/apache2/ grep -rn "AllowOverride" /etc/apache2/ grep -rn "ExecCGI" /etc/apache2/
# Confirm with nuclei nuclei -u https://your-server.com -t exposures/configs/directory-listing.yaml
Chapter 8: Prevention Checklist Run through this every time you deploy or modify a web server config.
a) Global Apache config does NOT contain Options Indexes anywhere b) All VirtualHost configs explicitly set Options -Indexes c) AllowOverride is set intentionally not left at default d) If .htaccess files are used, AllowOverride is configured to actually process them e) Log directories are either outside web root or explicitly denied f) Sensitive file extensions (.env, .bak, .sql, .key, .pem) are blocked via FilesMatch g) ExecCGI is not enabled unless explicitly needed and documented h) Server version disclosure suppressed: ServerTokens Prod and ServerSignature Off i) Config tested with apache2ctl configtest before reloading j) Manual verification done by requesting known directories via browser and curl k) Automated scan run post-deployment with nuclei or custom script l) Findings documented and change logged in ticketing system
Pro Tip: Integrate a post-deployment check into your CI/CD pipeline. A simple curl that verifies known directories return 403 can catch regressions before they hit production.
Closing Thoughts Directory listing is one of those findings that looks simple on paper but reveals something much deeper the gap between security intent and security reality.
Someone on this team knew Options -Indexes was the right move. They put it in the .htaccess. They did the right thing. But AllowOverride None silently nullified it. The protection existed only in the file, not on the server. That's a systemic configuration management failure, and it's more common than any of us want to admit.
The lesson isn't "learn more directives." The lesson is: verify your controls actually work, not just that they're configured. Test from the outside. Run the scan after the fix. Assume nothing.
The fix is five minutes of config editing. The cost of not fixing it can be measured in breach notifications and regulator phone calls.
Disclaimer: All findings described are based on real assessment patterns. Test only on systems you own or have explicit permission to test. Responsible disclosure matters.
