First and foremost, I am Thankful to GOD! 🙏R✨ 'm excited to share that I have successfully solved the Single-endpoint race conditions lab on PortSwigger.
What is this Lab about?
This lab focuses on a specific type of Race Condition where a single "endpoint" (a specific URL or function on a website) can be exploited if it doesn't handle multiple requests properly.
In this scenario, the website has an email change feature. Normally, you change your email, and the system updates your account. However, there is a "race window" between the time the server checks your request and the time it actually writes the data to the database.
The Core Vulnerability: The application allows you to associate any arbitrary email address with your account. There is a user named carlos@ginandjuice.shop who has a pending invite to be an administrator. If you can "race" the system to claim that email address as yours, you inherit his admin privileges automatically.
The correct path to follow🎯
The goal was to associate the email carlos@ginandjuice.shop with my account to inherit his pending admin invite.
Step-by-Step Exploitation 🛠️
1. Reconnaissance 🔍
- I logged in as
wiener:peterand navigated to the "My Account" section. - i use the default detail wiener:peter

then navigate to my account section and send the email provided also you can change the first name from that email

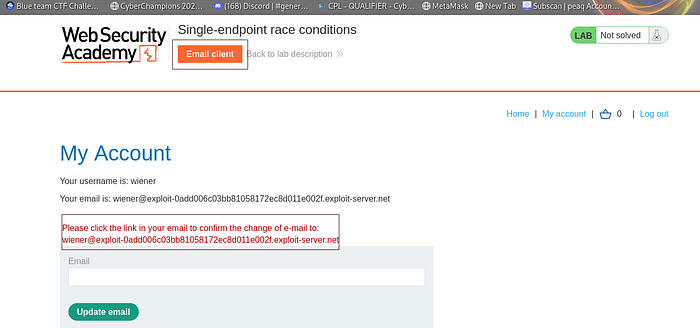
- through the browser you can change the name and then check confirmation
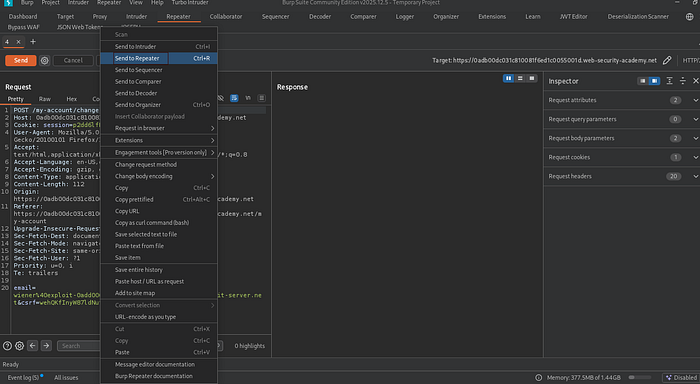
- I intercepted the
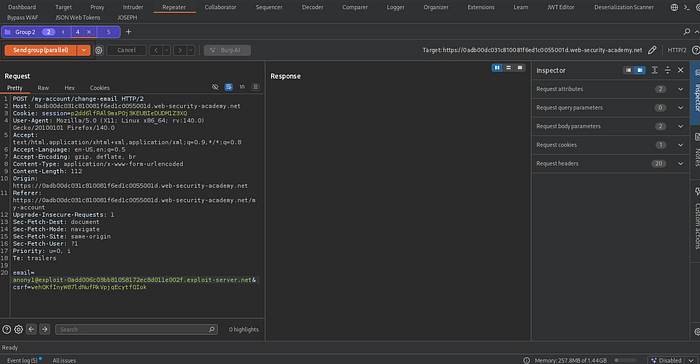
POST /my-account/change-emailrequest using Burp Suite to understand how the server handles email updates.
2. Preparing the Race ⚡
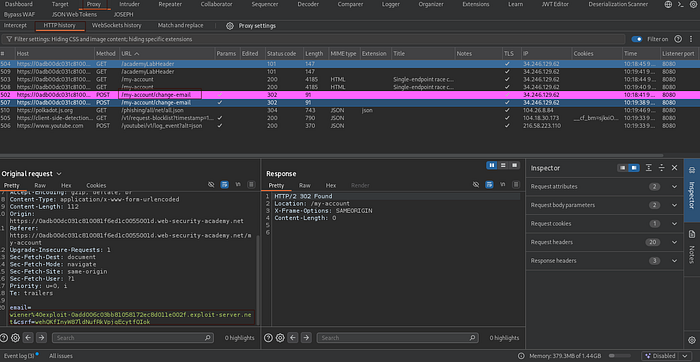
- I sent the change-email request to Burp Repeater.
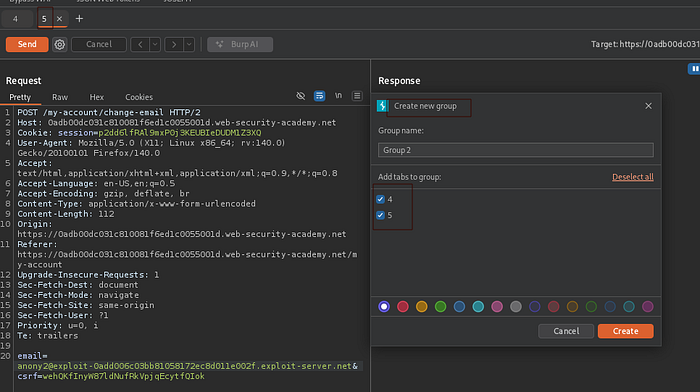
- I created a Tab Group containing two specific requests:
- before add another request into repeater
Also before you can try to change through browser and check the email link and then confirm as you see
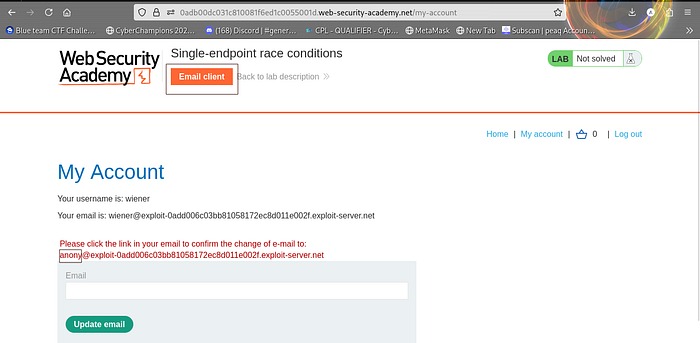
confirm and return into menu and refresh

as you see

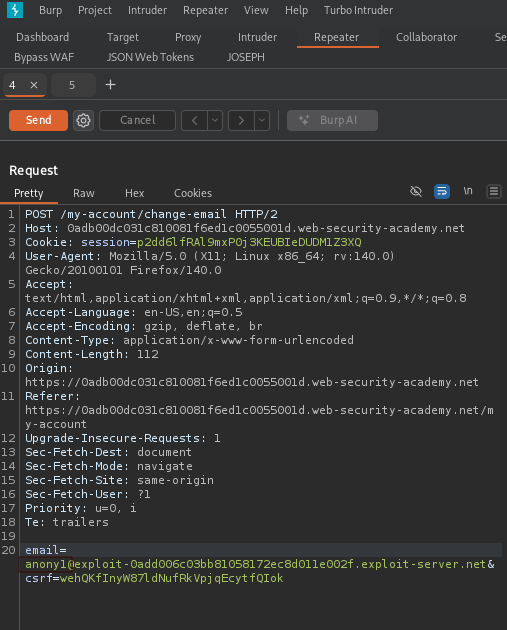
4.into repeater duplicate request into 2 request
and then change the name
Then rename as
- anony1: Changing the email to
carlos@ginandjuice.shop. - anony2: Changing the email to my legitimate exploit-server address.
again into another tab the same

then add group
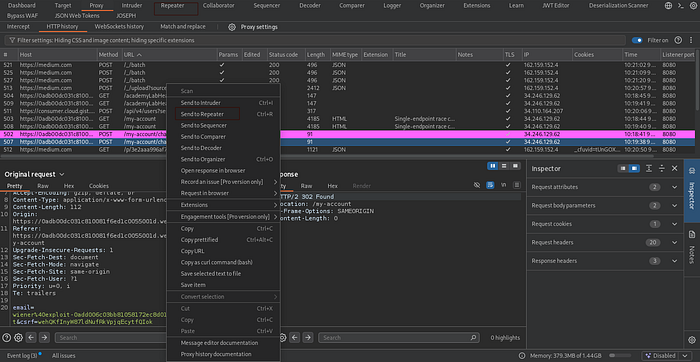
3. Executing the exploit🏎️💨
- Using the "Send group (parallel)" feature in Burp Suite (version 2023.9+), I fired both requests simultaneously.
- This created a "collision" on the server side where the database saved the admin email, but the confirmation was sent to my inbox
try to send to see if there is any changes
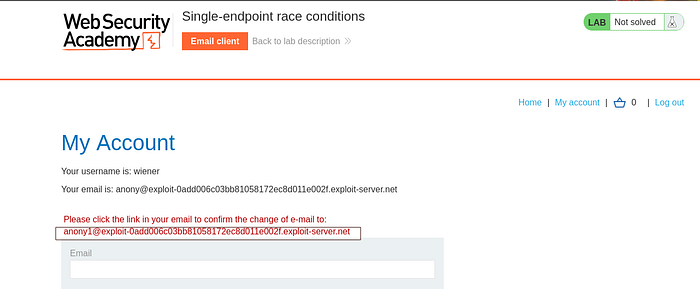
yes there is a changes you can confirm into a link and then return to the burp and now change the email and replace with
carlos@ginandjuice.shop
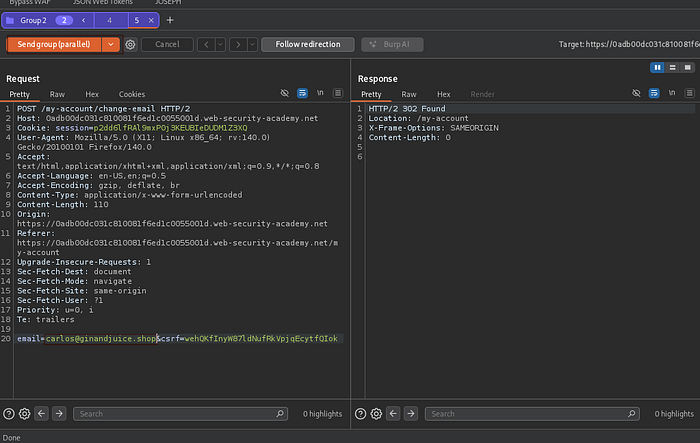
send and remember to refresh the browser page untill you see the email changed into browser
yes bingo like that

then go to the email link and confirm


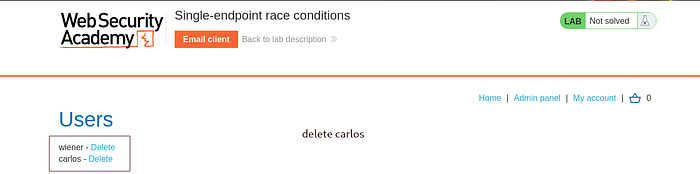
now return to the page and refresh the page and the exploit admin panel

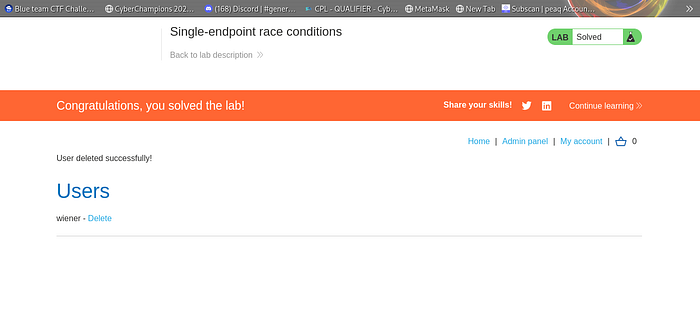
5. Final Objective 💀
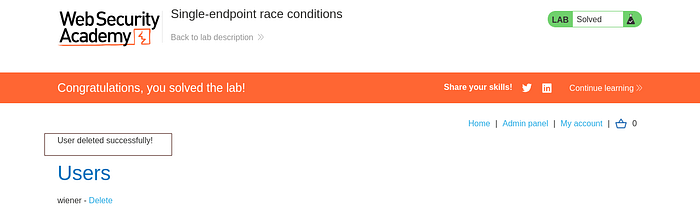
- I accessed the Admin Panel and successfully deleted the user "carlos" to solve the lab.
Conclusion & Remediation 🛡️
This lab proves that input validation isn't enough. Developers must use session locking or atomic database operations to ensure that one process finishes completely before another one starts on the same data.
#CyberSecurity #BugBounty #PortSwigger #EthicalHacking #RaceCondition 🔥🚀
ALL THE BEST