💣 Top 10 Critical CVEs from March 2026 — With Learning Resources & Practical Analysis
Most people read CVEs like news.
Top bug bounty hunters use them like:
👉 training material for finding real bugs
🔥 1. CVE-2026-21992 — Oracle RCE
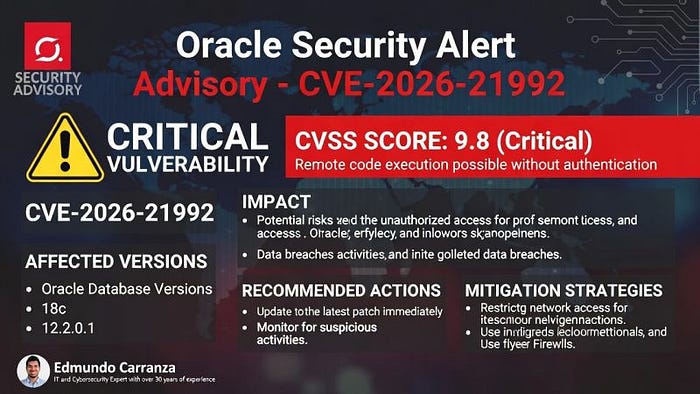
💥 Impact:
Remote Code Execution → Full system compromise
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-21992 👉 https://www.oracle.com/security-alerts/
🧠 What to Learn:
- Input validation failures - Backend service exposure
🧪 Practice:
- Try RCE labs on PortSwigger 👉 https://portswigger.net/web-security
---
⚡ 2. CVE-2026-26113 — Microsoft Office RCE
💥 Impact:
Malicious file execution
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-26113 👉 https://msrc.microsoft.com/update-guide/
🧠 What to Learn:
- File upload risks - Parser vulnerabilities
🧪 Practice:
- File upload labs 👉 https://portswigger.net/web-security/file-upload
---
💣 3. CVE-2026-26110 — Office Parsing Bug
💥 Impact:
Code execution via document
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-26110
🧠 What to Learn:
- Complex file parsing issues
---
🧠 4. CVE-2026-21536 — Microsoft RCE
💥 Impact:
Network-based exploitation
🔗 Learn More:
👉 https://msrc.microsoft.com/update-guide/
🧠 What to Learn:
- Exposed services - Network attack surfaces
---
🔐 5. CVE-2026-20079 — Cisco Auth Bypass
💥 Impact:
Unauthorized admin access
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-20079 👉 https://tools.cisco.com/security/center/
🧠 What to Learn:
- Broken authentication - API auth flaws
🧪 Practice:
- IDOR & auth labs 👉 https://portswigger.net/web-security/access-control
---
🌐 6. CVE-2026-20127 — Cisco Zero-Day
💥 Impact:
Full system compromise
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-20127
🧠 What to Learn:
- Authorization bypass - Token validation flaws
---
📱 7. CVE-2026-0038 — Android Privilege Escalation
💥 Impact:
Kernel-level access
🔗 Learn More:
👉 https://source.android.com/security/bulletin
🧠 What to Learn:
- Privilege boundaries - System-level security
---
🧬 8. CVE-2026-21385 — Android Memory Bug
💥 Impact:
Memory corruption
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-21385
🧠 What to Learn:
- Memory safety issues - Low-level exploitation concepts
---
💾 9. CVE-2026-21262 — SQL Server EoP
💥 Impact:
Database privilege escalation
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-21262
🧠 What to Learn:
- Backend misconfigurations - Privilege escalation
---
📊 10. CVE-2026-26144 — Excel Info Disclosure
💥 Impact:
Sensitive data exposure
🔗 Learn More:
👉 https://nvd.nist.gov/vuln/detail/CVE-2026-26144
🧠 What to Learn:
- Data leakage - Information disclosure
---
🧠 How to Use CVEs Like a Bug Hunter
Don't just read.
👉 Convert CVE → Testing Idea
---
💡 Example Mapping
- RCE → Test file upload, inputs - Auth bypass → Test IDOR, roles - Info leak → Check API responses
---
🧪 Best Practice Platforms
👉 Practice safely here:
- https://portswigger.net/web-security - https://tryhackme.com - https://hackthebox.com
---
⚠️ Important Note
👉 Only test in:
- Labs - Bug bounty scope
Never test real systems without permission.
---
🏁 Final Thought
👉 CVEs are not just vulnerabilities
👉 They are blueprints for real bugs
---
💬 Study them → Apply them → Find your own bugs
🚀 That's how top hunters grow.

