0xAbhiSec · Bug Bounty · Web Security Testing
Most people enter cybersecurity with a backpack full of tools and zero understanding of the target. They fire up Burp Suite, run a scanner, wait for red flags, and call it a day. When nothing shows up, they assume the application is secure.
It isn't. The scanner just couldn't see what a thinking person could.
If you find value in my cybersecurity writing, you can support my work here:
The Common Mistake Everyone Makes
Automated tools are seductive. They're fast, they look impressive, and they give you something to point at. Run a scan, get a report, submit the findings. Easy, right?
Not quite. Scanners are pattern matchers. They look for known signatures — outdated headers, common misconfigurations, CVEs they've been taught to recognize. They are incredibly useful for that narrow task.
But here's what they miss entirely:
What scanners can't catchBusiness logic flaws, broken access control in context, insecure direct object references (IDORs), chained vulnerabilities, and anything that requires understanding "what the application is supposed to do".
A scanner doesn't know that a user shouldn't be able to access another user's invoice by changing an ID in the URL. It doesn't know that a discount code can be applied twice if you intercept the right request. That's not a signature — that's a thought.
The Mindset Shift That Changes Everything
Real vulnerability discovery isn't about running more tools. It's about thinking differently about what you're looking at. This is what people mean when they say "think like a hacker" — and it's not a cliché, it's a discipline.
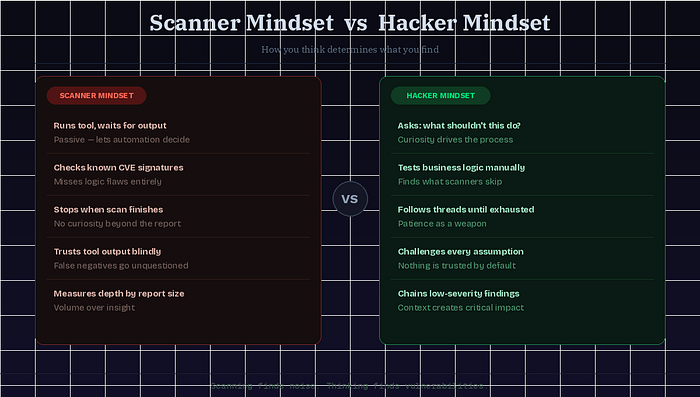
Scanner Mindset
- Waits for a tool to flag something
- Trusts automated output completely
- Looks for known patterns
- Stops when the scan finishes
- Measures success by report length
Hacker Mindset
- Asks "what should this NOT do?"
- Questions every assumption
- Looks for logical inconsistencies
- Follows curiosity, not checklists
- Measures success by impact found
The hacker mindset is rooted in curiosity. It asks: what happens if I do something unexpected? What if I send a negative quantity? What if I access this endpoint without authentication? What if two legitimate features combine in a way the developer didn't anticipate?
"Hackers don't look for what's broken. They look for what was assumed to be impossible."
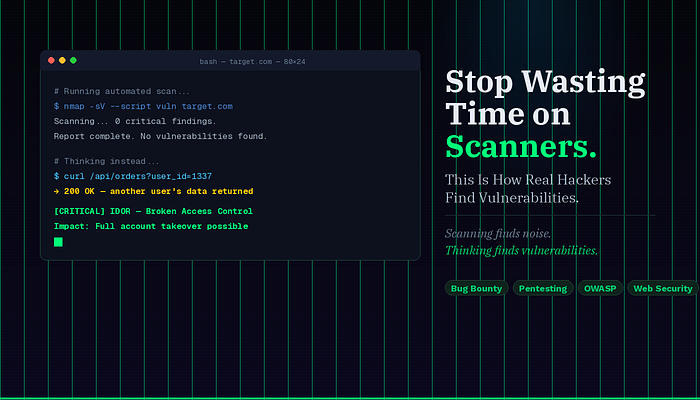
A Real-World Example: The IDOR a Scanner Never Found
Here's a scenario that plays out constantly on platforms like HackerOne. A researcher is testing an e-commerce application. They log in, place an order, and notice the URL: /api/orders?order_id=10482.
The scanner saw nothing unusual here. It's a valid authenticated endpoint, no injection vectors, no exposed headers. Clean bill of health.
But the researcher thought: what if I change that number?
They changed order_id=10482 to order_id=10481. They got back a different user's full order — name, address, purchase history, everything.
This is a classic Insecure Direct Object Reference (IDOR) — listed prominently in the OWASP Top 10 under Broken Access Control, and consistently one of the most common vulnerabilities found in bug bounty programs. It requires no special tooling. It requires only the thought: "Is my identity actually being verified here, or is the server just trusting the number I sent?"
A Practical Framework for Thinking Like an Attacker
Developing a pentesting mindset isn't abstract. Here's how to make it actionable on every target you assess:
1.Map the application flow first
Before touching a single tool, walk through the app as a real user. Understand every feature. Note every place data is submitted, retrieved, or displayed.
2.Find every parameter and ask "who owns this?"
IDs, tokens, filenames, user references — these are your targets. Ask: is ownership actually enforced server-side, or just assumed?
3.Break the expected sequence
What happens when you skip step 2 in a 4-step checkout? What if you replay an old token? Developers test the happy path — test the unhappy ones.
4.Test your assumptions, not just the app's
When you think "this is probably secure," that's exactly when to probe. Assumptions are where bugs live.
5.Chain low-severity findings
An info-disclosure and a CSRF alone might be boring. Together, they might be critical. Think in combinations, not individual findings.
Tools Are a Support Act, Not the Main Stage
This isn't anti-tool advice. Burp Suite is genuinely excellent — its Proxy, Repeater, and Intruder modules are irreplaceable when you're doing web security testing. But the key word is when. You reach for Burp Suite to test a hypothesis you already formed by thinking.
The workflow should be:
Observe → Hypothesize → Test → Confirm.
Tools help with the "Test" phase.
The first two steps require a human brain.
Running a scanner at the start of an engagement is like sending a metal detector through a library. You might find something. But you'll miss the most interesting things entirely.
Why Most People Stay Stuck
Here's the uncomfortable truth about why so many aspiring security researchers plateau quickly:
Over-reliance on automation means you find what everyone else already found. If you're running the same scanners as every other tester, you're competing in a race to the bottom on known issues.
Lack of patience is the other killer. Real vulnerability discovery requires sitting with an application for hours, reading source code, testing edge cases that feel unlikely. The bugs that earn the best payouts on platforms like HackerOne are almost always the ones nobody else was patient enough to find.
Avoiding fundamentals — too many people learn tools before they understand HTTP, authentication patterns, or how access control is supposed to work. Without that foundation, you're operating blind even when a scanner flags something real.
The shortcut that isn't oneEvery hour spent truly understanding how a web application works is worth more than ten hours of automated scanning. The depth compounds.
The Closing Thought
Bug bounty tips and hacking techniques flood the internet. But the rarest and most valuable skill in vulnerability discovery isn't knowing more tools it's knowing how to think about a target long after the tools have finished their reports.
Security researchers who consistently find impactful bugs share one trait: they never accept the application at face value. They pull at threads. They ask inconvenient questions. They assume there's something to find, and they look with their brain before they look with Burp.
Scanners find noise. Thinking finds vulnerabilities.
Found this useful? Follow me for more real-world web app security write-ups, pentest tips, and vulnerability breakdowns.
Your support helps me continue creating honest, no-hype security content.
— 0xAbhiSec
Happy hunting.
Tags: #Cybersecurity #Bug Bounty #Ethical Hacking #Penetration #TestingWeb Security
Have questions or want to share your own findings? Drop a comment below.