A structured reference covering the categories, capabilities, and strategic value of tools used to defend Operational Technology and Industrial Control System environments.
⬡ Classification: Practitioner Reference
⬡ Domain: OT / ICS / SCADA Security
⬡ Audience: Security Engineers & Architects
As industrial environments converge with enterprise IT and cloud platforms, the tooling required to defend them has grown significantly in sophistication.
Unlike IT security tools, OT/ICS tools must operate within strict constraints; they must be non-intrusive, operationally aware, and capable of understanding industrial protocols. This guide catalogs the primary tool categories, their purposes, key examples, and deployment considerations.
Why OT Security Tools Are Different
The tools designed for enterprise IT environments, endpoint detection, vulnerability scanners, and patch managers, cannot be applied directly to OT environments without risk. An active network scan that is routine in IT can crash a Programmable Logic Controller (PLC) or disrupt a SCADA server. A software agent deployed on an engineering workstation may interfere with real-time process control.
OT security tools are purpose-built to respect these realities. Their design priorities differ fundamentally from their IT counterparts:
Priority 1 Non-Disruption
Passive over active wherever possible. The environment must keep running during monitoring and assessment.
Priority 2 Protocol Awareness
Deep understanding of industrial protocols: Modbus, DNP3, EtherNet/IP, PROFINET, IEC 61850, OPC-UA, and others.
Priority 3 Safety Integration
Tools must be aware of Safety Instrumented Systems (SIS) and avoid actions that could interfere with safety logic.
Tool Category Overview
OT/ICS cybersecurity tools fall into six primary categories. Each serves a distinct function within a layered defense strategy, and mature programs deploy tools across all categories in a coordinated architecture.

Category 1 — Asset Discovery & Inventory Tools
You cannot protect what you cannot see. Asset discovery tools provide the foundational visibility required for every other security function. In OT environments, they operate passively, listening to network traffic to identify and fingerprint devices without sending probes that could disrupt operations.
Key Capabilities
- Passive device identification via traffic analysis (MAC, IP, device type, firmware version)
- Industrial protocol fingerprinting — identifying PLCs, RTUs, HMIs, and engineering workstations.
- Automatic asset inventory population and change detection
- Integration with CMDB and vulnerability management systems
- Detection of new or unauthorized devices connecting to the network
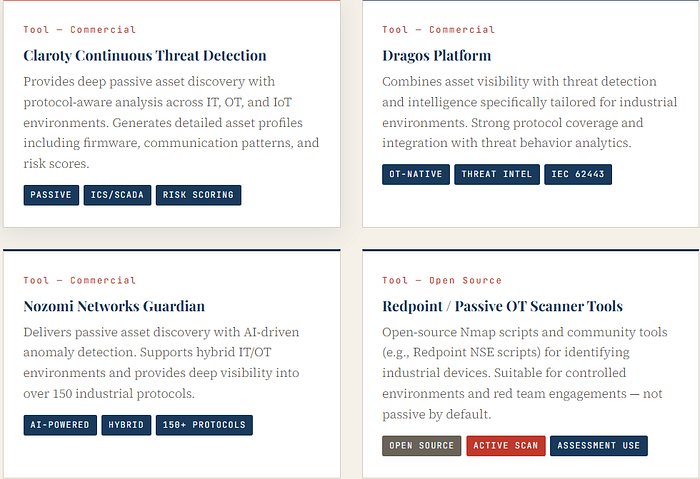
Category 2 — Network Monitoring & Anomaly Detection
Once assets are known, continuous monitoring of communications between them becomes essential. OT network monitoring tools analyze industrial traffic in real-time, baselining normal behavior and alerting when deviations occur, whether due to attack, misconfiguration, or equipment failure.
Key Capabilities
- Deep Packet Inspection (DPI) for industrial protocols
- Behavioral baselining — learning normal communication patterns per device
- Alerting on unauthorized commands, unusual polling rates, or new connections
- Detection of known attack signatures (e.g., TRITON/TRISIS, Industroyer tactics)
- Integration with SOC and SIEM platforms for centralized alerting
In OT environments, the most dangerous attacks are often the quietest — subtle command modifications, slow data exfiltration, and pre-positioned access that generates no obvious alert. Behavioral anomaly detection is the primary countermeasure. (Core Principle — OT Network Defense)
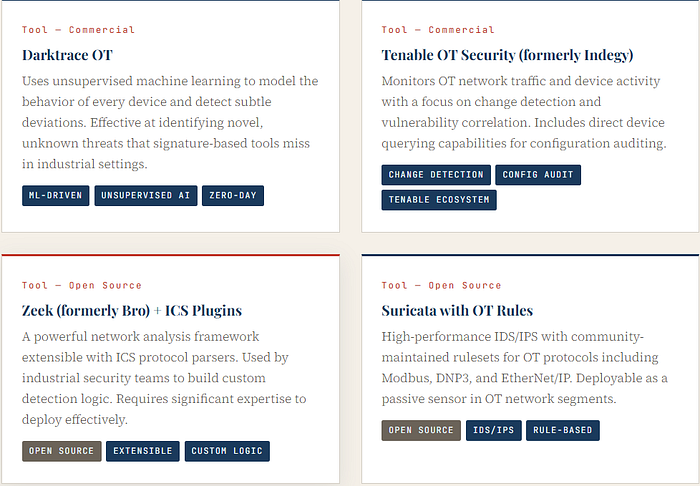
Category 3 — Vulnerability Management for OT
Vulnerability management in OT is considerably more constrained than in IT. Many OT assets cannot be patched on a regular schedule — a PLC managing a live production line may run for months or years without a maintenance window. Tooling in this category must prioritize passive assessment, risk-based prioritization, and compensating controls over remediation velocity.
Key Capabilities
- Passive vulnerability identification via network traffic and asset fingerprinting
- CVE correlation against identified OT asset firmware and software versions
- Risk scoring adapted to OT context (consequence of exploitation, not just CVSS score)
- Vendor advisory tracking for ICS-specific vulnerabilities (ICS-CERT, PSIRT feeds)
- Virtual patching recommendations via firewall rules and network controls
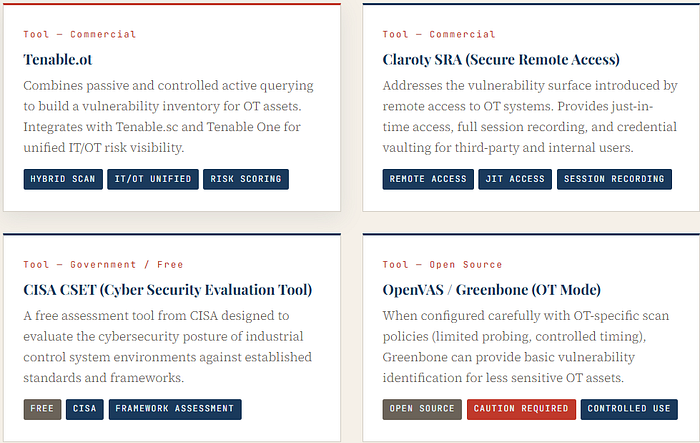
Category 4 — Identity & Access Management (IAM) for OT
Remote access to OT environments has expanded dramatically, driven by vendor maintenance requirements, centralized operations, and digital transformation initiatives. This access surface is one of the most exploited attack vectors in industrial breaches. OT-aware IAM tools provide the controls necessary to manage, monitor, and restrict who can interact with critical systems.

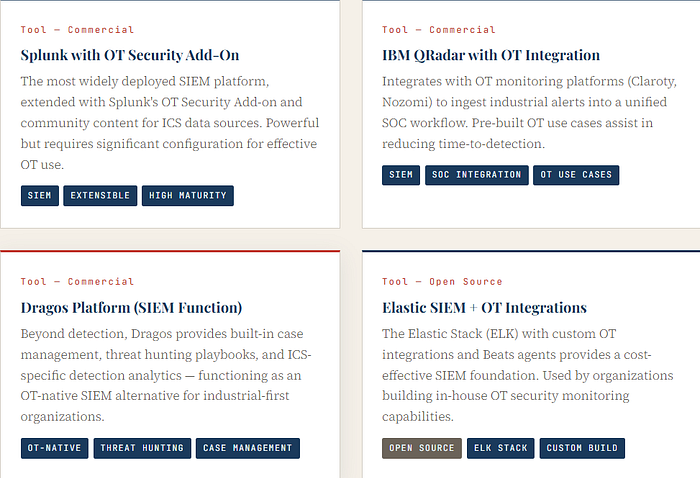
Category 5 — SIEM & Log Management for OT
Centralizing and correlating security events from OT environments requires SIEM solutions adapted to understand industrial data sources, including historian logs, DCS events, and protocol-level alerts from OT monitoring tools. Standard SIEM platforms require significant customization; OT-native solutions provide pre-built integrations and correlation rules tailored to industrial attack patterns.
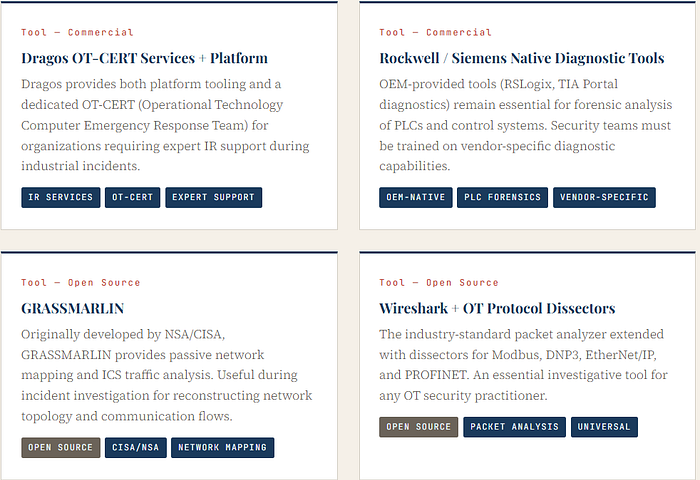
Category 6 — Incident Response & Forensics
OT incident response is categorically different from IT incident response. Isolating a compromised system may be impossible when that system is controlling an active physical process. Forensic tools must be able to capture and analyze industrial artifacts — PLC ladder logic, historian data, HMI logs — while the organization manages the difficult tradeoffs between safety, operations, and containment.
Critical Considerations for OT IR Tooling
- Forensic capture must be non-disruptive — live acquisition preferred over shutdown-and-image
- PLC logic backup and integrity verification tools are essential pre-incident investments
- Evidence must preserve the chain of custody while maintaining operational context.
- IR tools must be pre-positioned — deploying them during an active incident is too late.
- Tabletop exercises using OT-specific scenarios are required to validate IR procedures.
Supporting Tools & Specialized Capabilities
Beyond the six primary categories, several specialized tool types address specific OT security challenges that fall outside conventional IT security frameworks.
Data Diodes & Unidirectional Gateways
Hardware-enforced unidirectional data transfer solutions (e.g., Waterfall Security UG, Owl Cyber Defense) ensure that data can flow from OT to IT networks, but never in reverse. These provide an absolute, hardware-level enforcement mechanism that no software vulnerability can bypass. Widely deployed in nuclear, defense, and critical infrastructure environments.
OT Threat Intelligence Platforms
Industrial-specific threat intelligence feeds (e.g., Dragos WorldView, Claroty Team82 Research, Recorded Future ICS) provide adversary tracking, ICS vulnerability intelligence, and sector-specific threat reporting. Unlike generic CTI feeds, OT threat intelligence covers ICS-targeted malware families, PLC exploitation techniques, and nation-state TTPs targeting specific industrial sectors.
OT Security Assessment & Penetration Testing Tools
Controlled OT penetration testing requires specialized toolsets, including SCADA Defense, AttackIQ for OT, and purpose-built ICS attack simulation frameworks. These must only be used in test environments or with extreme operational caution, as active exploitation attempts against live OT systems can cause physical damage.
Network Segmentation & Firewall Enforcement
Industrial-grade firewalls with OT protocol awareness, such as Palo Alto Networks Industrial OT Security, Fortinet FortiGate with OT profiles, and Tofino Xenon (now part of Belden) enforce zone and conduit boundaries at the network level. These tools understand industrial protocols deeply enough to allow or deny specific commands, for example, permitting read commands on Modbus while blocking write operations.
Choosing the Right Tools: A Decision Framework
Tool selection in OT security should be driven by operational context, not vendor marketing. The following factors are critical determinants of which tools are appropriate for a given environment:
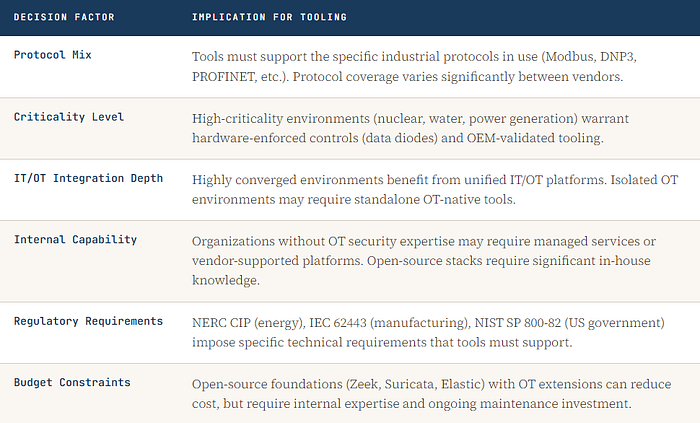
The most common mistake in OT security tool deployment is purchasing a platform without first establishing the visibility, segmentation, and process foundations that make the tool meaningful. Tools amplify capability; they do not replace it.
Strategic Deployment Principle
From Tools to Resilience
No single tool provides OT security. Resilience in industrial environments is the product of layered defenses, integrated tools, trained teams, and well-practiced response procedures. The tooling landscape covered in this guide represents the current state of the field, a rapidly evolving ecosystem driven by the growing recognition that industrial infrastructure is a primary target in modern conflict and cybercrime.
Organizations that invest seriously in OT security tooling and the expertise to operate it will be positioned not merely to detect attacks but to maintain safe and predictable operations even when those attacks succeed.
That is the definition of resilience. And in operational technology environments, resilience is not optional.
This document is intended as a professional practitioner reference. Tool capabilities, vendor offerings, and market landscape evolve continuously. Practitioners should validate tool capabilities directly with vendors and evaluate against their specific operational environment before deployment.
