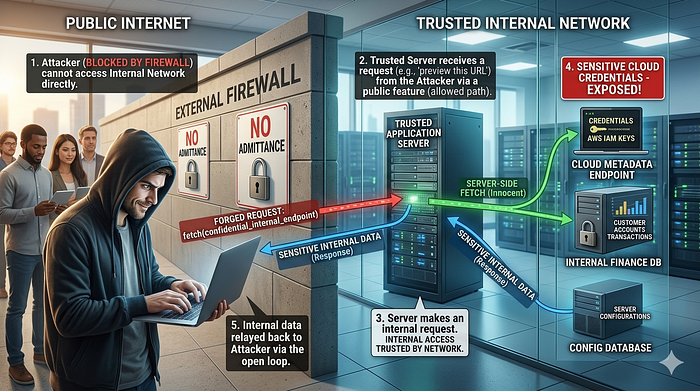
The most dangerous position an attacker can reach is not outside your system throwing attacks at it. It is inside your network, making requests that look completely legitimate because they are coming from a machine you trust. Server-Side Request Forgery (SSRF) gets them there without ever needing to touch your internal infrastructure directly.
Here is the everyday version. Imagine you work at a company with a strict visitor policy. No outsiders are allowed past the reception desk. But there is one trusted internal employee whose job involves fetching documents from any department on request. An attacker cannot get past reception themselves, so instead they hand that employee a forged request note and ask them to fetch a confidential document from the executive floor. The employee, following instructions as designed, walks right past every internal checkpoint and brings back exactly what was asked for. No alarm fires. The employee did nothing wrong by their own understanding of the job.
That trusted employee is your server. SSRF is the forged note.
When an application fetches a remote resource based on a URL or address supplied by the user, and does not validate what destinations are permitted, an attacker can redirect that server-side request anywhere they choose. Including places that are completely unreachable from the outside internet but fully accessible from inside the server's own network.
This vulnerability appears across many types of platforms. 1. Document processing tools that fetch files from URLs. 2. Social platforms that generate link previews by visiting submitted URLs. 3. Analytics dashboards that pull data from user-specified sources. 4. Webhook systems that send requests to URLs provided by integrating partners. Any feature where your server visits a URL on behalf of a user is a potential SSRF surface.
In fintech, the attack surface expands significantly because of how modern financial infrastructure is built. Cloud-hosted payment platforms, banking APIs, and digital wallet backends all run on infrastructure where internal services, configuration endpoints, and administrative interfaces sit on the same internal network as the application. An SSRF vulnerability in any outward-facing feature of that platform becomes a bridge into that internal world.
The most frequently targeted destination in cloud environments is the instance metadata endpoint. On AWS, that endpoint lives at a fixed internal IP address that is only accessible from within the cloud instance itself. It returns sensitive configuration data, including IAM credentials, which grant permissions to cloud resources. An attacker who can force the server to make a request to that address and return the response has just collected credentials that may allow them to access storage buckets, databases, internal APIs, and other cloud services far beyond the original application.
Technically, the attack is clean. An application offers a feature that fetches and previews content from a URL the user provides. The developer validates that the URL begins with http or https, which feels like sufficient protection. The attacker submits the internal metadata endpoint address. The server makes the request, receives a response containing cloud credentials, and depending on how the application handles the fetched content, returns it to the attacker directly or stores it somewhere they can access. The URL validation passed. The feature worked as designed. The application had no instruction not to visit that address.
A realistic scenario: a fintech platform offers a KYC document upload feature where users can optionally submit a URL pointing to their hosted document instead of uploading directly. The backend fetches the document from the provided URL and stores it internally. An attacker submits the AWS metadata endpoint address instead of a document URL. The server fetches it, the response contains temporary IAM credentials, and the application stores the response as a document file. The attacker retrieves their stored document and now holds valid cloud access credentials. From there, they move laterally through the cloud environment, reaching databases, internal APIs, and storage containing customer financial data.
Preventing SSRF requires validating not just the format of a URL but its destination. 1. Maintain an explicit allowlist of permitted domains and IP ranges for any server-side fetch operation and deny everything outside it. 2. Block requests to private IP ranges, loopback addresses, and cloud metadata endpoints at the network level as a defense in depth measure. 3. Disable unnecessary URL-fetching features entirely if the use case does not genuinely require them. 4. Use a dedicated outbound proxy for all server-side HTTP requests so you can enforce destination policies consistently. 5. Never return raw fetched content directly to the user without stripping sensitive response data. 6. Log all outbound requests made by the server and alert on requests to unexpected destinations.
Your server has access to parts of your infrastructure that the internet never should. SSRF is how attackers borrow that access without asking.
A messenger who delivers any note to any destination is not a trusted employee. It is a liability waiting to be exploited.
#CyberSecurity #SSRF #ServerSideRequestForgery #APISecurity #WebSecurity #ApplicationSecurity #FintechSecurity #CloudSecurity #SecureByDesign #OWASP #DevSecOps #SoftwareEngineering #SecurityEngineering #30DaysOfSecurity #CTOInsights