OpenClaw has rapidly gained popularity since its release, surpassing even the Linux kernel in GitHub stars. Many people use it as their co-worker or personal assistant, giving users full access to their digital life and social media accounts like WhatsApp, Telegram, MS Teams, and many other tools, which is exactly what makes an exposed OpenClaw gateway a serious security concern.
OpenClaw's Growing Vulnerability Problem
Over the past month, OpenClaw has been hit with multiple high severity vulnerabilities. Some allow Remote Code Execution (RCE) on hosted machines, including CVE-2026–25253 and CVE-2026–24763. Beyond known CVEs, there is also the possibility of undisclosed zero-days not yet available to the public. Since OpenClaw can access the browser, it may also be vulnerable to command injection through malicious websites, a flaw already demonstrated by the recently disclosed ClawJacked vulnerability, and the SDKs or third-party libraries OpenClaw depends on may carry their own unpatched vulnerabilities.
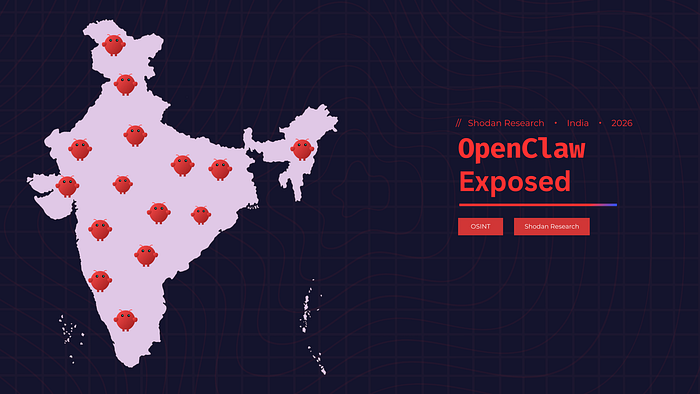
How Many Are Still Exposed?
Some of these vulnerabilities were patched in OpenClaw version 2026.1.29 and later. After learning that so many flaws are now publicly known, I got curious, how many OpenClaw instances are still exposed to the internet in India, and are they running patched versions?
Finding OpenClaw in the Wild
When I started researching on Shodan, what surprised me wasn't how many instances were open, but the vulnerability details visible right in the banners. That information makes an attacker's job significantly easier, sitting there publicly indexed for anyone to find.
I started with a simple Shodan search, port 18789 filtered to India. The results showed 1,300+ instances, with Mumbai having the most, followed by Bengaluru. But something felt off. Digging into the banners I realized port 18789 isn't exclusive to OpenClaw, other services were running on it too, which was inflating my numbers significantly. I needed a more accurate approach.
Switching to the product:"OpenClaw" filter on Shodan gave me much more accurate results. Since it directly fingerprints the product itself, I trusted this data more. The results showed 400+ instances across India, surprisingly low for such a large country, but concerning enough to dig deeper. To be clear, I wasn't touching any of these systems, everything I could see was already publicly indexed by Shodan. By seeing the HTTP 200 OK status codes in the banners, I assumed these instances were accessible to anyone on the internet, that's what told me they were exposed, not any active probing or testing on my part. I was just reading what was already out there. Looking at the city breakdown, one result stood out immediately. Doddaballapura, a city in the Bengaluru district, had more instances than anywhere else in India.
I dug deeper to understand who was actually running these instances, were they self-hosted on personal machines or cloud servers? The answer was surprising. The top organizations were DigitalOcean, Vultr Holdings, and The Constant Company, all cloud VPS providers, not local Bengaluru businesses. This changed everything. It turns out Shodan's geolocation isn't always reliable. These IPs were physically hosted elsewhere in the world, yet Shodan's data placed them in Doddaballapura because that's where those cloud providers' IP ranges happen to be registered. A good reminder that location data on Shodan should always be verified against the actual hosting organization.
Interactive charts available in the original post at russeldsouza.dev
When looking at the top organizations across all of India, even major cloud providers like Amazon, Google and Microsoft appear, suggesting OpenClaw is being deployed across all types of cloud infrastructure, not just budget VPS providers.
What This Means for OpenClaw Users
As we saw, exposed OpenClaw instances are actively indexed on Shodan, and with multiple high severity CVEs now public, leaving them unpatched is a real risk. Here's what you should do:
- Update OpenClaw to the latest version. Yes it might break things, yes there may be issues, but running a vulnerable version connected to your entire messaging life is a worse problem.
- Use Tailscale. It creates a private encrypted network so only your authorized devices can reach your OpenClaw instance, completely invisible to Shodan and the public internet.
- Run OpenClaw in a containerized environment. Isolating it limits the damage if something goes wrong.
- Give it only the permissions it actually needs. Don't connect every chat, every email, every account by default. OpenClaw is an AI, it can hallucinate, it can get prompt injected, and a compromised instance with full access to your digital life is a nightmare scenario.
AI is a powerful tool, but it can't always be trusted blindly, and that applies to the security of the systems running it too. AI doesn't take accountability, if your data gets deleted, it's deleted; if it gets leaked, it's leaked. You are responsible for what you connect to it and what you give it access to. Limit permissions, stay updated, and stay skeptical.