When starting web security testing or bug bounty hunting, the first and most important step is reconnaissance (Recon) which is the process of collecting information about a target system before testing it for vulnerabilities.
It helps researchers understand
- What infrastructure the target uses
- What subdomains exist
- What technologies power the application
- Where the potential attack surface may be
In this short case study, I'll walk through the basic reconnaissance steps I used while analyzing the domain: https://burgerprofiel.beta-vlaanderen.be
So this article focus on the RECON rather than EXPLOITATION
A: Target Overview
The target domain analyzed was:
burgerprofiel.beta-vlaanderen.be
From the domain structure, we can already notice:
burgerprofiel → the main service
beta → likely a testing or staging environment
vlaanderen.be → associated with Flemish government services
B: Recon Methodology
The recon process followed these basic steps:
1. Domain information lookup
2. DNS Enumeration
3. Subdomain discovery
4. SSL certificate inspection
5. Technology identification
Let's walk through each step.
1. Domain Information Lookup
The first step was checking domain registration information using a WHOIS lookup.
What WHOIS Does
WHOIS helps identify:
- Domain registrar
- Registration date
- Expiration date
- Contact information
Command Use : whois burgerprofiel.beta-vlaanderen.be
Information Found
Registrar: COMBELL-MNT
Registration Date: 2009–06–08
Expiration Date: May 30, 2026
Abuse Contact: abuse@combell.com
This indicates that the domain infrastructure is managed through Combell hosting services.
2. DNS Enumeration
Next I checked the DNS configuration of the domain.
DNS records tell us how a domain is connected to the internet.
Command Used : dig burgerprofiel.beta-vlaanderen.be
A / AAAA Records
These records reveal the server's IP addresses.
217.21.190.139 2a02:26f0:9d00::5f64:6270
This means the system supports both: IPv4 / IPv6
MX Records
mx.mailprotect.be
This suggests the domain uses MailProtect for email services.
Name Servers
ns1.combell.eu ns3.combell.net ns4.combell.net
Again, these point to Combell infrastructure
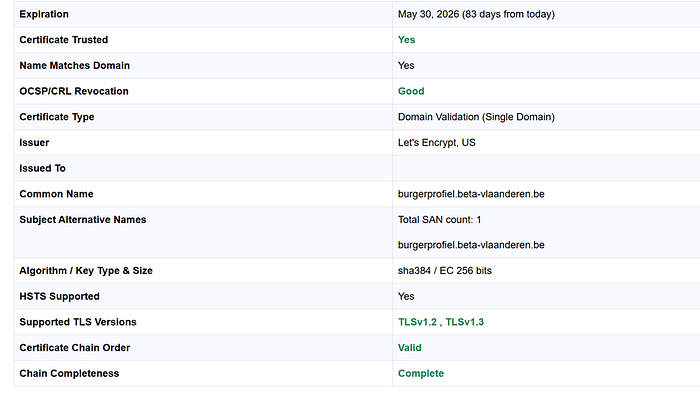
3. SSL Certificate Inspection
Another useful recon step I used is inspecting the SSL certificate used by the domain using the website https://www.sslshopper.com/ssl-checker.html
Certificates often reveal:
- Certificate authority
- Validity dates
- Additional domains linked to the certificate
This below is the Screenshot that i have discovered while doing the SSL Certificate Inspection.
4. Subdomain Discovery
Subdomain enumeration is a critical process in cybersecurity and penetration testing used to identify all subdomains associated with a target domain. These subdomains often reveal hidden, forgotten, or misconfigured systems that can serve as potential attack vectors.
During recon using subfinder , I found several related subdomains:
beta.gastwebsite-acm.burgerprofiel.ext-vlaanderen.be beta.gastwebsite.burgerprofiel.ext-vlaanderen.be beta.widgets.burgerprofiel.dev-vlaanderen.be burgerprofiel.beta-vlaanderen.be vo-gebruikersbeheer.vlaanderen.be
These domains indicate multiple environments such as:
- beta environment
- development environment
- external service integrations
This expands the overall attack surface of the platform.
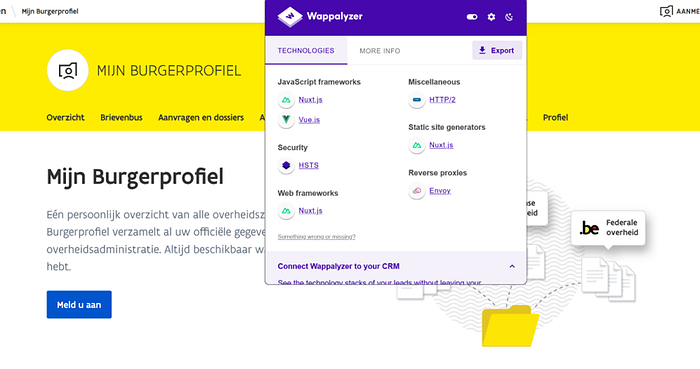
5. Technology Identification
Understanding the technology stack helps researchers know what frameworks and services power the application.
During this recon I used Wappalyzer which helps me to detect things like:
- web servers
- frameworks
- JavaScript libraries
- security headers
Knowing the technology stack helps guide further security testing. This is below Screenshot of the tech stacks that my targeted website is using..
C: Final Thoughts
As a beginner my goal during reconnaissance is not to rush into vulnerability hunting. Instead I focus on building a clear picture of the target environment.
By following a simple workflow like:
- Understanding the domain
- Checking WHOIS data
- Enumerating DNS records
- Discovering subdomains
- Inspecting SSL certificates
- Identifying technologies
I can gradually map out the system and understand how everything is connected.
Stay hacking stay curious .< 3.