Introduction
In recent years, phishing attacks have become one of the most common techniques used by threat actors to steal sensitive information such as user credentials and personal data. Attackers frequently impersonate trusted services and organizations to deceive victims into interacting with malicious infrastructure.
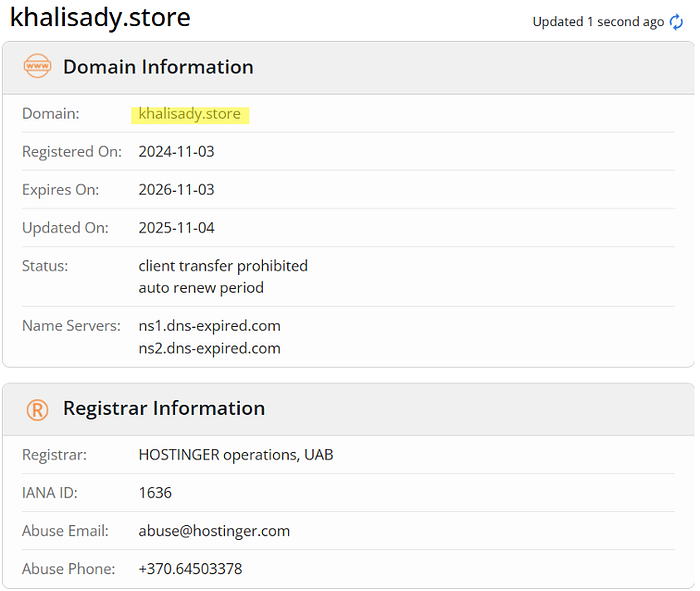
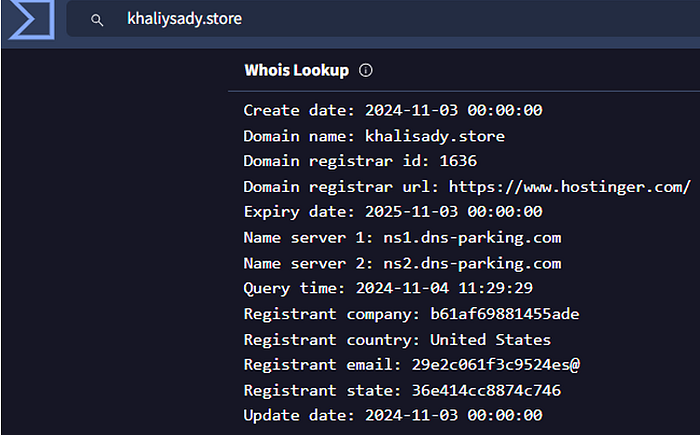
This investigation focuses on the analysis of the suspicious domain khalisady.store, which was reportedly involved in a phishing campaign impersonating Dropbox. The objective of this report is to examine the domain's intelligence characteristics, including its infrastructure, DNS records, IP associations, and any related indicators that may suggest malicious activity.
Using various open-source intelligence (OSINT) tools and threat intelligence platforms, the investigation aims to identify abnormal behavior linked to the domain, such as suspicious email infrastructure, potentially malicious subdomains, or indicators of command-and-control activity. Additionally, the analysis attempts to correlate the domain's creation timeline with reported Dropbox phishing campaigns to determine whether it may have been part of a broader malicious operation.
The findings of this report include technical evidence, screenshots, and supporting indicators that demonstrate the domain's potential association with phishing activity.
Objective
The primary objective of this investigation is to analyze the domain khalisady.store and determine whether it is associated with malicious activity, particularly phishing campaigns targeting Dropbox users.
This report aims to:
- Identify the domain's infrastructure and DNS characteristics
- Investigate associated IP addresses and hosting details
- Discover related subdomains and indicators of phishing behavior
- Analyze the domain's email infrastructure for suspicious activity
- Correlate the domain creation date with known Dropbox phishing campaigns
Methodology
To perform this investigation, several Open-Source Intelligence (OSINT) tools and threat intelligence platforms were used to gather information about the domain and its infrastructure.
The analysis included:
- Domain and WHOIS investigation
- DNS and infrastructure analysis
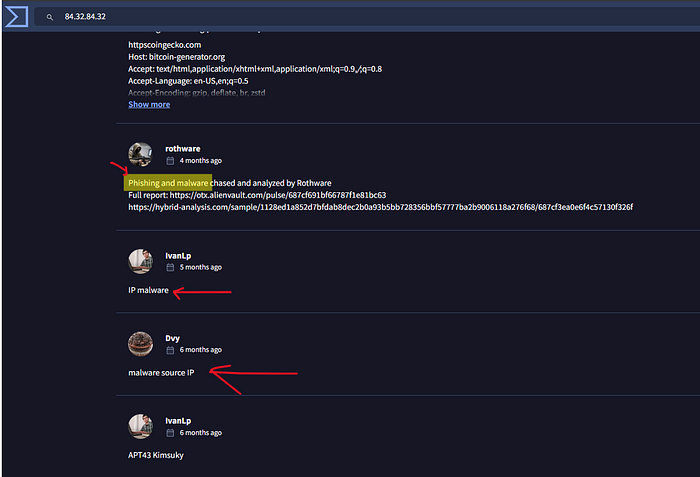
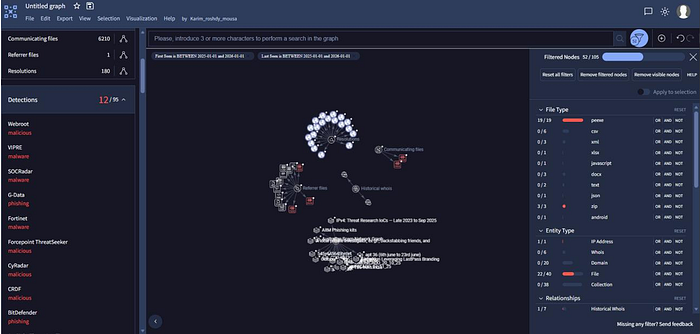
- IP reputation and threat intelligence checks
- Subdomain enumeration
- Correlation with known phishing campaigns
These techniques help identify suspicious patterns and indicators commonly associated with phishing infrastructure.
Let's Get started!
First Step:
Check Authentication Domain
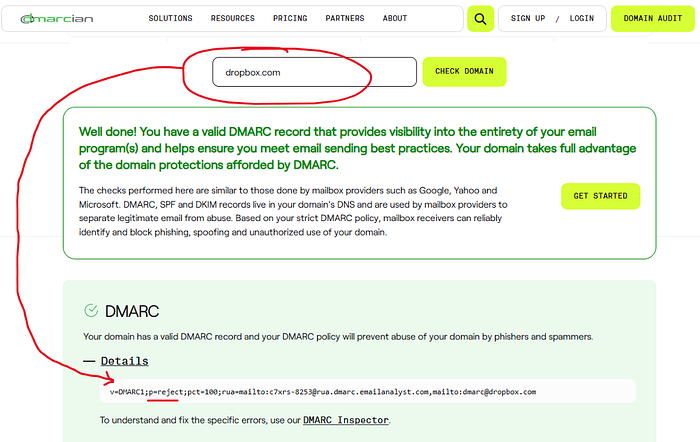
DMARC analysis of dropbox.com showing a valid DMARC policy configured with p=reject, which helps prevent email spoofing and phishing attempts using the Dropbox domain.
Second Step :
Search by use Google Dorking

Collect Information A bout Domain

The analysis indicates that the domain khalisady.store is classified as a Disposable Email Domain, a type of domain often used to create temporary email addresses and may be associated with activities such as spam or phishing campaigns.
Third Steps : search by Virus total to collect more information

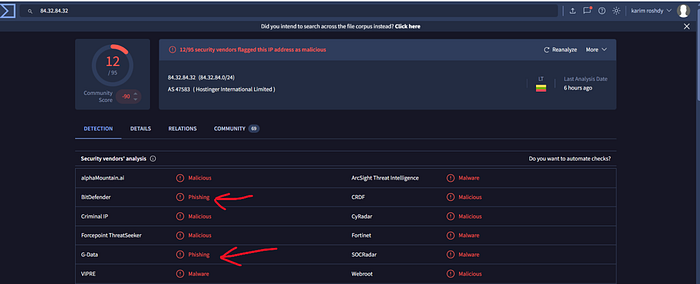
In conclusion, the investigation of khalisady.store demonstrates strong indicators of phishing activity targeting Dropbox users. The domain's infrastructure, DNS records, and subdomains confirm its malicious intent, highlighting the importance of monitoring and blocking suspicious domains to prevent credential theft.