We've all seen it: the "Download" button is missing. The platform promises high-security content protection. They tell you the content is "stream-only." But as a security researcher, when I see a "No Entry" sign, I don't see a wall — I see a challenge.
{ٱقۡرَأۡ وَرَبُّكَ ٱلۡأَكۡرَمُ ۞ ٱلَّذِي عَلَّمَ بِٱلۡقَلَم ۞ عَلَّمَ ٱلۡإِنسَٰنَ مَا لَمۡ يَعۡلَمۡ}
Alsalamu Alaykum, My name is Ammar Harris. I'm a 2nd-year CS student, an offensive security enthusiast, and a hunter of Business Logic Vulnerabilities. While most hunters are busy looking for XSS or SQLi, I'm obsessed with how a business thinks — and where that thinking fails.
Recently, I stumbled upon a flaw in a major educational platform that allowed me to bypass their Digital Rights Management (DRM) and download entire courses. Here is the breakdown of how I did it, the "Black Hat" temptation I avoided, and why this "Duplicate" report was still a massive win for my career.
The Moment Curiosity Kicked In
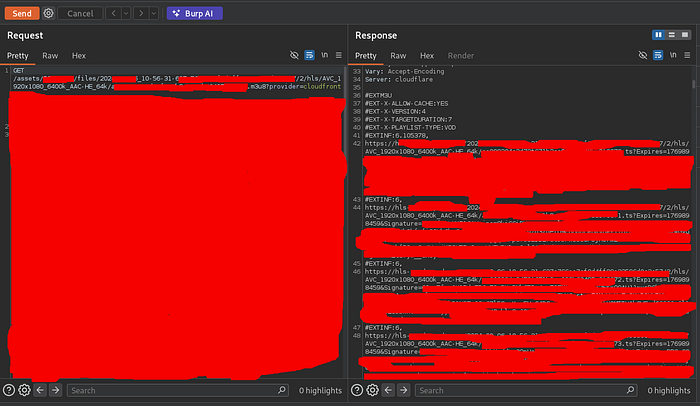
Like many security people, I have a habit: I open Burp Suite whenever something interesting loads.
While watching a lecture, I intercepted the requests and noticed an endpoint returning something interesting.
HLS video links.
At first glance this looked normal.
But something felt off.
The 5‑Second Clue
When opening one of the returned links, I expected a video stream.
Instead, I downloaded a 5‑second video clip.
That alone wasn't strange.
But when I opened the next one…
It continued exactly where the previous clip ended.
Then the next.
And the next.
That was the moment everything clicked.
The DRM Illusion
The platform prevented downloads in the UI.
But technically it exposed every piece of the lecture through sequential video fragments.
Which meant one thing:
If someone automated collecting those fragments…
They could rebuild the entire lecture.
No DRM break.
No encryption bypass.
Just logic.
The Exploit: AI-Assisted Weaponization
As a student, I value efficiency. I used Gemini to architect the logic of the exploit and Claude 4.5 Sonnet to polish a Python-based PoC.
The Script Logic:
- Input: A text file containing the HLS response.
- Process: Filters headers, iterates through the fragment queue, and downloads the
.tschunks. - Execution: Uses
ffmpegto stitch the fragments into a seamless 720p lecture. - Cleanup: Automatically deletes the fragmented files to leave a clean, single video file.
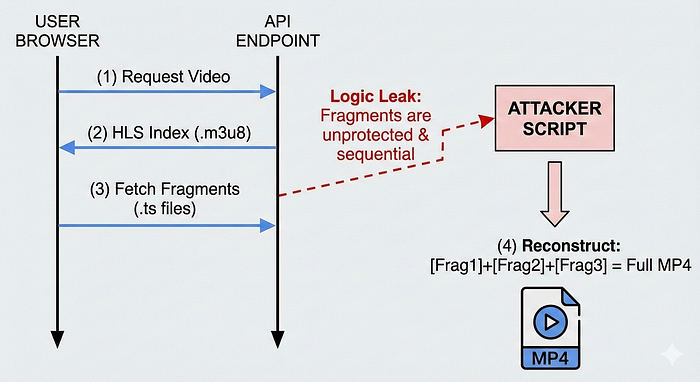
Note: While I could have automated this for the entire course library, I stopped at the PoC. Moving from "one video for proof" to "the whole database" is the line between White Hat research and Black Hat activity.
Reporting the Bug
I reported the bug via their responsible disclosure program. The response?
"This is a duplicate of an informative report from 2023."
Was it frustrating?
Of course.
But bug bounty hunting isn't only about rewards.
Sometimes the real reward is leveling up your mindset.

What This Discovery Taught Me
1. Business Logic Bugs Are Everywhere
Systems often fail not because of code errors — but flawed assumptions.
2. Observation Beats Complexity
Many vulnerabilities hide in normal behavior.
You just have to watch carefully.
3. Automation Demonstrates Real Impact
A clear PoC can turn a "maybe" vulnerability into a serious report.
4. Ethical Boundaries Matter
Knowing when to stop is part of being a real security researcher.
What is next on my journey?
Looking Forward: Kernel Hacking & Beyond
This journey reinforced my love for Business Logic. It's about outsmarting the architect, not just the code.
Currently, preparing for deep-diving into:
- Reverse Engineering: Breaking down binaries to see how they tick.
- Kernel Hacking: Moving from the application layer to the heart of the OS.
The Hacker's Mindset
Stay curious. Stay ethical. And remember: the most dangerous vulnerabilities aren't always in the code — they're in the assumptions we make about how the code will be used.
Find me here:
- linkedIn: www.linkedin.com/in/ammar-harris
- Platforms Handle: 0xfreed0m
#BugBounty #CyberSecurity #InfoSec #BusinessLogic #Hacking

