In this room, we will understand more about what a penetration tester's job responsibilities and what processes should be followed prior to performing pentests.
Learning Objectives:
- Define a penetration test and be able to explain its purpose
- Recognize the broad relevance of ethically-driven Pentest with Cyber Security
- Understand the need for proactive security measures
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
This room consists of 5 tasks: 1. What is Penetration Testing? 2. Penetration Testing Ethics 3. Penetration Testing Methodologies 4. Black box, White box, Grey box Penetration Testing 5. Practical: ACME Penetration Test
I will walkthrough each room with my own answer method
===============================================================
- Task 1: What is Penetration Testing?
Before we dive deeper into the technical hands-on aspects of ethical hacking, we need to priorly understand what a penetration tester's job responsibilities.
A penetration test or AKA pentest is an ethically-driven attempt to test and analyse the security defenses in a system or website. This activity often involves using the same tools, techniques that someone with malicious intent (attacker) would use. Basically speaking, a pentester will actually act like the real attacker.
Q1) Read me !
Answer: no answer needed
===============================================================
- Task 2: Penetration Testing Ethics
To recall, the penetration test is an authorised audit of a computer system's security and defences as agreed by the system's owners. Thus, before starting a pentesting activity, the pentester usually will have a prior discussion with the system owner about the agreed tools-to-used and other policies.
For instance, if the pentesters are successfully gaining access to a database, even able to see several sensitive data. Or, they are probably performing a phishing attack on an employee to test an organisation's human security. If these cases has been agreed upon during the initial discussion then this will be legal
Hackers are sorted into three hats category, with different ethics and motivations:
- White Hat: considered "good ppl", as they remain within the law and use their skills to benefit others
- Grey Hat: these people use their skills to benefit others often, but they don't respect the law or or ethical standards
- Black Hat: these people are criminals and often seek to damage organisations and gain financial benefits at the costs of others
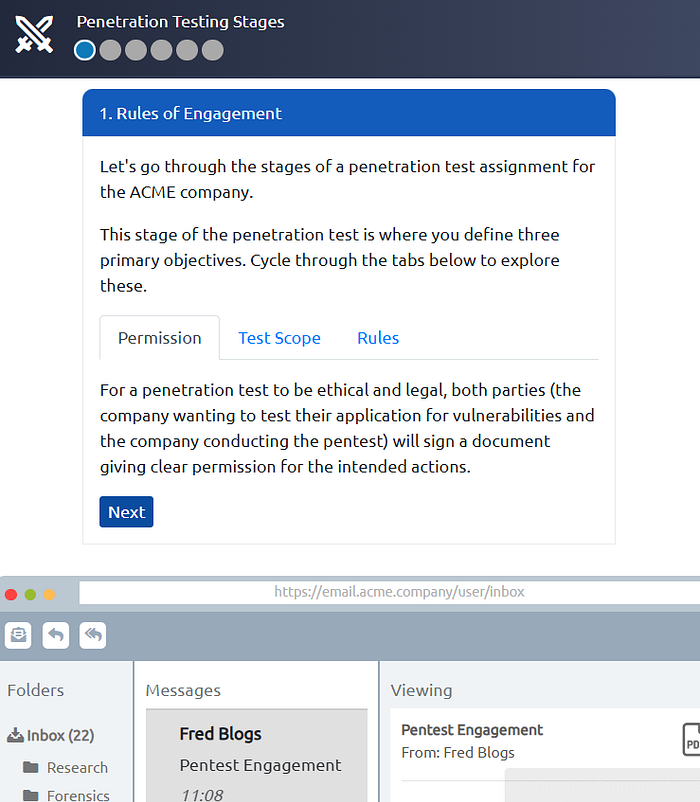
Rules of Engagement (ROE) is created at the initial stages of a penetration testing engagement, as this document contains 3 main sections:
- Permission: to protect individuals and organisations for the acitivities they carry out
- Test Scope: to annotate specific targets to which the engagement should apply
- Rules: to state the specific allowed techniques used for this activity
Q1) You are given permission to perform a security audit on an organisation; what type of hacker would you be?
Answer: White Hat
Q2) You attack an organisation and steal their data, what type of hacker would you be?
Answer: Black Hat
Q3) What document defines how a penetration testing engagement should be carried out?
Answer: Rules of Engagement
===============================================================
- Task 3: Penetration Testing Methodologies
Methodology is the steps a penetration tester takes during an engagement. This includes several different stages, such as:
- Information Gathering: to collect accessible information
- Enumeration/Scanning: to discover applications and services running on the system
- Exploitation: to leverage vulnerabilities discovered in a system or application
- Privilege Escalation: to expand our access to a system. Can escalate horizontally and vertically
- Post-Exploitation
— — — — — — — — — — — — — — — — — — — — — — — — — — — — — — — —
There are several frameworks to discuss here:
- OSSTMM (Open Source Security Testing Methodology Manual), where it provides a detailed framework of testing strategies for systems, software, applications, communications, and the human aspect of cybersecurity.
- OWASP (Open Web Application Security Project), which is a community-driven and frequently updated framework used solely to test the security of web applications and services.
- NIST Cybersecurity Framework 1.1, which improve an organisations cybersecurity standards and manage the risk of cyber threats
Q1) What stage of penetration testing involves using publicly available information?
Answer: Information Gathering
Q2) If you wanted to use a framework for pentesting telecommunications, what framework would you use? Note: We're looking for the acronym here and not the full name.
Answer: OSSTMM
Q3) What framework focuses on the testing of web applications?
Answer: OWASP
===============================================================
- Task 4: Black box, White box, Grey box Penetration Testing
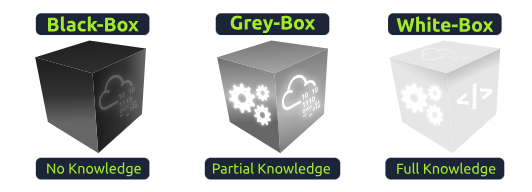
- Black-Box Testing: The tester has no knowledge of the internal workings and acts as a standard user interacting with the interface. This external perspective increases the time spent on information gathering to understand the attack surface.
- Grey-Box Testing: This hybrid approach combines elements of both black-box and white-box methods, which provides the tester with limited internal knowledge. This will save some time and make it a popular choice for penetration testing on well-hardened targets.
- White-Box Testing: The tester has full knowledge of the application's internal logic and code to validate specific functions.
Q1) You are asked to test an application but are not given access to its source code — what testing process is this?
Answer: Black Box
Q2) You are asked to test a website, and you are given access to the source code — what testing process is this?
Answer: White Box
===============================================================
- Task 5: Practical: ACME Penetration Test
In this task, we will be given the practical exercise to gain the real feelings of penetration testing
Q1) Complete the penetration test engagement against ACME's infrastructure.
Answer: THM{PENTEST_COMPLETE}
===============================================================