In most SOC environments, we track a lot of numbers. Dashboards look impressive. Reports go out weekly or monthly. But if we're honest, not every metric truly reflects SOC maturity or analyst performance. Over time, I've realized that the metrics that matter are the ones that help you answer three simple questions:
- Are we detecting threats fast enough?
- Are we responding efficiently?
- Are we actually improving over time?

Here are the metrics that genuinely make a difference.
1. Mean Time to Detect (MTTD)
This measures how long it takes to identify suspicious activity after it occurs.
The shorter this time, the less opportunity an attacker has to move laterally or escalate privileges.
MTTD usually improves when:
- Detection rules are well-tuned
- Noise is reduced
- Analysts are not overloaded
It's not just a number — it reflects the quality of your detection engineering.
2. Mean Time to Respond (MTTR)
This measures the time from detection to containment or resolution.
From a business perspective, this is one of the most critical metrics. Leadership doesn't just want to know that something was detected — they want to know how quickly it was handled.
Clear runbooks, defined escalation paths, and automation through SOAR can significantly reduce MTTR.
3. Alert Volume vs. Closure Rate
If alert volume keeps increasing but closure rate stays flat, it's a warning sign.
It could mean:
- Too many noisy use cases
- Analysts stretched thin
- Poor prioritization
A healthy SOC doesn't just generate alerts — it closes them efficiently within SLA.

4. False Positive Rate
A consistently high false positive rate drains analyst energy and increases the risk of missing real threats.
This metric tells you how mature your use cases really are.
Improving it often requires:
- Better correlation logic
- Behavioral baselining
- Context enrichment
Reducing false positives doesn't mean reducing visibility. It means improving precision.
5. Detection Coverage (MITRE Mapping)
Tracking how many MITRE ATT&CK techniques your use cases cover gives a clearer picture of detection maturity.
It shifts the focus from "How many alerts do we have?" to "What attack techniques can we actually detect?"
This is especially useful when demonstrating SOC capability to leadership or clients.

6. SLA Adherence
This measures how consistently analysts meet triage and response timelines.
It reflects operational discipline and service reliability.
High SLA adherence usually indicates:
- Clear workflows
- Defined ownership
- Strong shift coordination
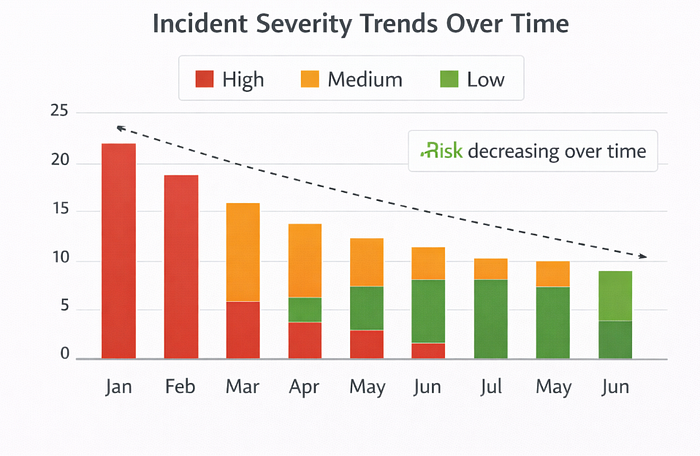
7. Incident Severity Trends
Looking at how High, Medium, and Low incidents trend over time gives context.
If high-severity incidents reduce over months, it suggests proactive detection and improved prevention.
If they increase, it's a signal to reassess controls and coverage.
8. Automation Rate
Automation isn't about replacing analysts — it's about removing repetitive tasks.
Tracking how many enrichment or response steps are automated shows how optimized your SOC is.
Higher automation usually results in:
- Faster triage
- Lower MTTR
- Reduced burnout
9. Detection Engineering Velocity
How often are new use cases being introduced or old ones updated?
Threat actors evolve constantly. A static detection environment eventually becomes outdated.
Tracking this ensures your SOC evolves alongside the threat landscape.
10. Repeat Incident Rate
If the same incident type keeps recurring, something is wrong at the remediation level.
This metric highlights gaps in:
- Root cause analysis
- Patch management
- Control enforcement
A mature SOC doesn't just close incidents — it prevents recurrence.
What Should You Actually Report?
For executive-level reporting, focus on:
- MTTD and MTTR
- SLA adherence
- Alert vs. closure trends
- False positive rate
- Incident severity trends
- Detection coverage
- Repeat incident rate
These metrics together provide a balanced view of performance, maturity, and business value.
Final Thought
SOC metrics shouldn't exist just to fill dashboards. They should guide decisions, improve processes, and help analysts work smarter not harder.
When chosen correctly, the right KPIs tell a story: not just about threats, but about progress.
