In web application security testing, the initial, often overlooked, stage is actually the foundation of the entire testing process: Information Gathering. According to the OWASP Web Security Testing Guide, Information Gathering is a systematic process for gathering as much information as possible about a target before conducting further testing, such as exploitation or vulnerability analysis.
Conduct Search Engine Discovery Reconnaissance for Information Leakage
Organizations often believe their systems are secure because they don't have direct access to sensitive files. However, they forget that search engines like Google can index files or directories that shouldn't be exposed. This technique is known as Search Engine Reconnaissance or Google Dorking. Example website: ubl.ac.id
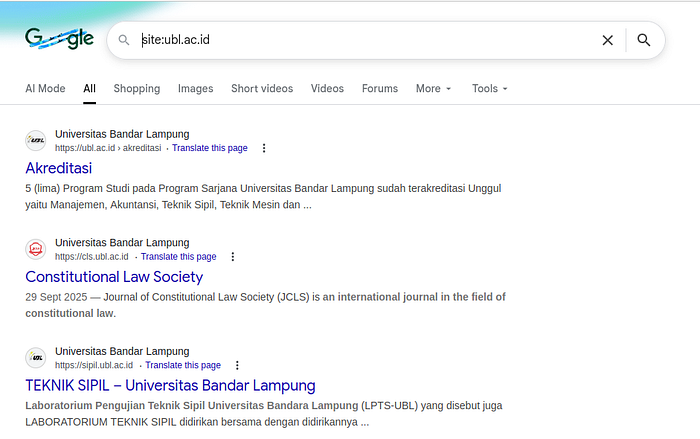
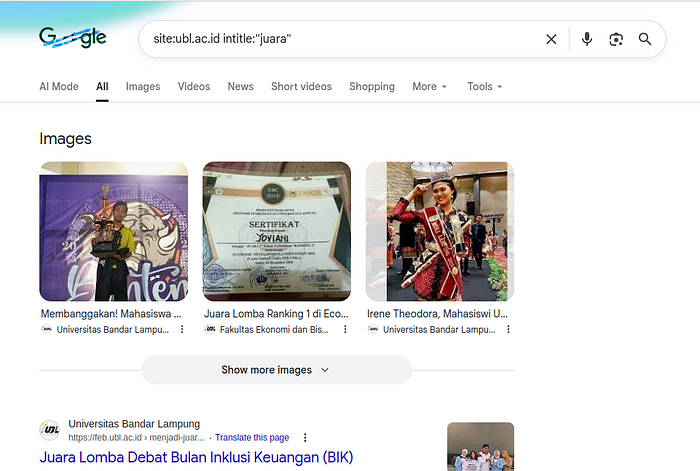
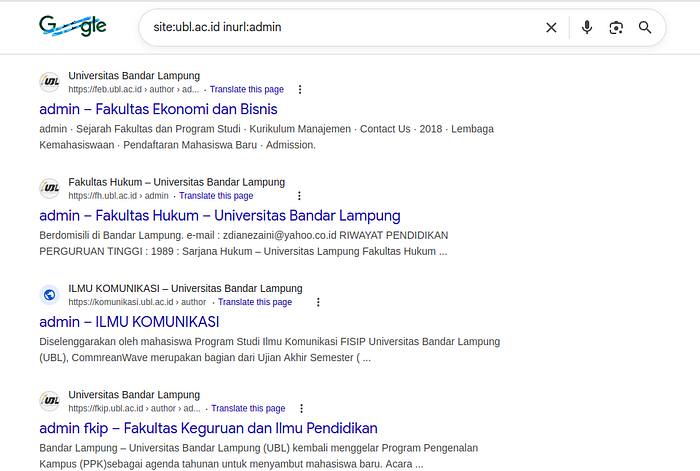
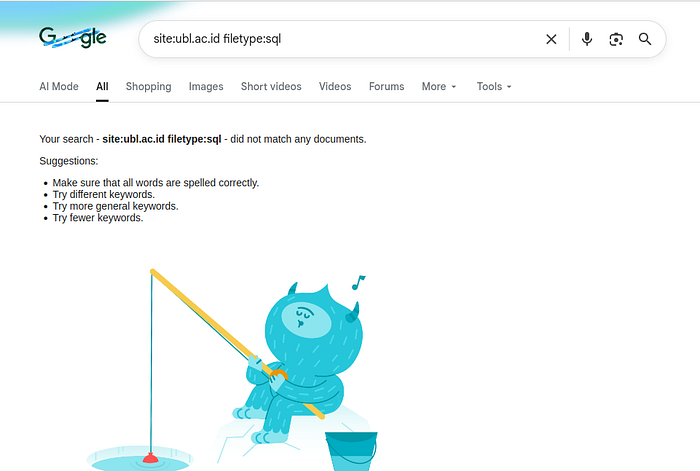
In a security context, findings like indexed .env or .sql files are a serious indication of information leakage. From this, we learn that data leaks are often not caused by sophisticated attacks, but rather by poorly thought-out configuration.
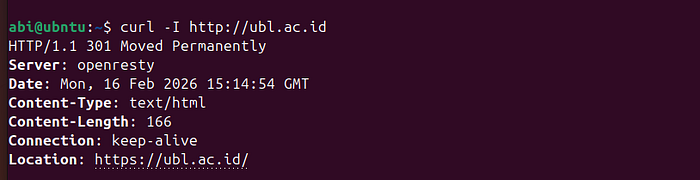
Web Server Fingerprinting: Recognizing System Identity
This is called fingerprinting. Why is this important? Because every technology has:
- Certain versions
- A history of vulnerabilities
- Exploitable default configurations
This information is important because each version has different potential vulnerabilities. If an older version (for example, a vulnerable version of Apache) is found, it can be checked against a vulnerability database such as CVE.
Examples
Review Web Server Metafiles: Small Files, Big Impact
Often, files like robots.txt or sitemap.xml are considered harmless. However, they can provide important clues about an application's structure. Example
Through this process, we can find:
- Staging folders
- Backup files
- Endpoint development
- Leftover configuration files
This stage indicates that security breaches are common through small details that are overlooked.
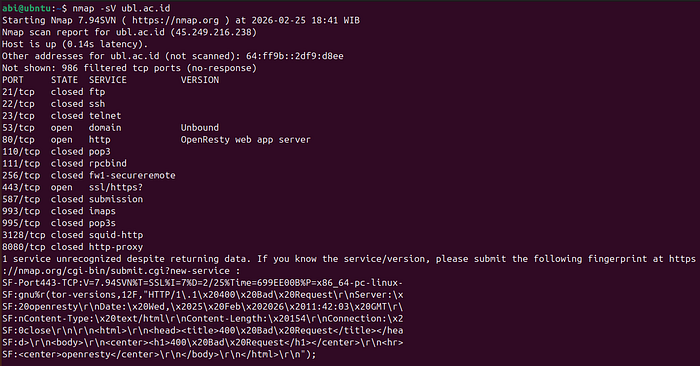
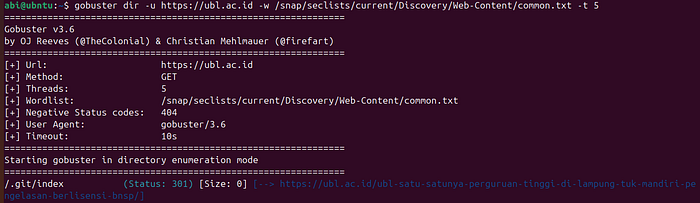
Application and Subdomain Enumeration
In many cases, a primary domain doesn't just run one application. It may contain:
- Development subdomains
- Staging servers
- Separate APIs
- Internal panels
To identify subdomains, you can use
subfinder -d ubl.ac.idThen proceed with port scanning
nmap -p- ubl.ac.idif a port is found
- 3306
- 8080
- 3000
so it is possible that there are additional services running.
Review Web Page Content: The Information Behind the Display
Not all hidden information resides on the server. Sometimes leaks occur on the client side.
By opening:
<<<> Code
Ctrl + U (View Bource)We may encounter comments such as:
<> HTML
<<
TODO: remove before production
<API KEY=123456Additionally, JavaScript files also often store:
- Endpoint API internal
- Token
- Baking structure
- Validation logic
Through DevTools (Network tab), we can also observe requests and responses running behind the scenes. This stage teaches that security is not only about the backend, but also how the frontend manages information.
Reflection: Information Gathering as a Foundation for Security
From this entire process, I learned that Information Gathering is more than just collecting technical data. It's the process of building a holistic picture of the system.
Without this level:
- Testing becomes undirected
- The risk of being late becomes greater
- Analysis efficiency decreases
In contrast, with systematic Information Gathering:
- The attack surface can be mapped
- Potential leaks can be identified early on
- Testing becomes more structured
In the context of learning, this stage also forms a critical mindset — that security is not about attacking, but about understanding how systems can be exposed so we can build them more securely.
Conclusion
information gathering is an often underestimated initial step, but it is the determining factor in the success of web application security testing. As an Informatics student, understanding this stage helps me see systems not just as running applications, but as entities with digital footprints, configurations, and potential risks. Because in the end, security isn't just about finding vulnerabilities. But it is about understanding the system as a whole before the gaps are exploited by irresponsible parties.
Reference https://owasp.org/www-project-web-security-testing-guide/latest/4-Web_Application_Security_Testing/01-Information_Gathering/README https://haxoris.com/testing-methodologies/wstg