Hello, my name is Muhammed Elsayed, also known as Scander0X. I am a Bug Bounty Hunter with a strong passion for offensive security and real-world vulnerability discovery.
I actively engage in security research and knowledge sharing, and I participate in bug bounty programs on platforms such as HackerOne and YesWeHack.
My primary interests include Business Logic Vulnerabilities and Access Control flaws. I have hands-on experience testing web, mobile, and cloud environments, and my goal is to continue growing in the cybersecurity field while making a meaningful impact through responsible disclosure and research.
Before diving into the technical details, it is important to understand the concept of Price Manipulation:
Price Manipulation is a business logic vulnerability that occurs when an application allows users to alter the price of a product or service during a transaction. Instead of calculating and enforcing the correct amount on the server side, the system relies on client-supplied values that can be modified.
For example, if a product costs €100 and the request includes a parameter such as amount=100, an attacker can intercept the request and change it to amount=1. If the server does not properly validate the amount, the transaction may be processed with the manipulated value.
This issue results from improper server-side validation of sensitive financial data and can directly impact the organization's revenue
Understanding application:
When I test an application, I always start by understanding how it works and what features exist. This step is very important, but many beginner bug hunters ignore it. Skipping this usually leads to wasted time, missing real impact, or reporting duplicates.
In this case, the application is a secure communication platform that allows users to exchange messages and hold private conversations in a protected environment. The core business of the application is built around trust, confidentiality, and message visibility, so any flaw that affects message handling can have a real security and trust impact.

During my testing, I discovered several impact issues across the platform. However, my primary objective was to identify a vulnerability that could significantly impact the business. I shifted my focus to the subscription plans and billing workflow, particularly how payments were processed and validated.
I observed that the platform relies on external payment verification methods such as SEPA and iDEAL. While analyzing the payment flow through iDEAL, I noticed that the server did not properly validate the price parameter submitted during payment intent creation.
Specifically, the request included a client-controlled parameter.

{
"payment_intent": {
"status": "inited",
"amount": 10,
"currency_code": "EUR",
"payment_method_type": "ideal",
"gateway": "stripe"
}
}Steps to Reproduce:
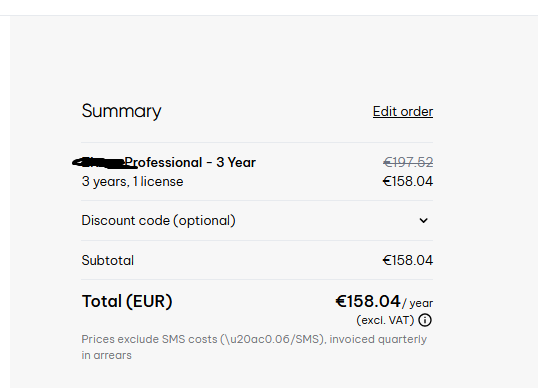
1. Select a paid subscription plan priced at €100.
2. Intercept the payment request during the checkout process.
POST /api/v2/payment_intents
{
"payment_intent": {
"status": "inited",
"amount": 100,
"currency_code": "EUR",
"payment_method_type": "ideal",
"gateway": "stripe"
}
}3. Modify the amount parameter before forwarding the request
Change:
amount=100
To:
amount=14. Proceed with the payment via iDEAL.
5. Observe the result:
Payment is successfully processed for 0.11 EUR.
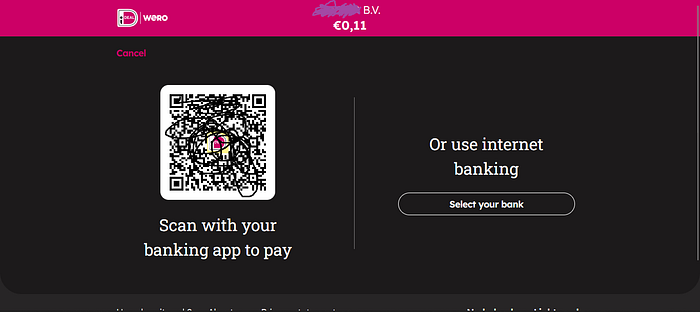
The service/subscription is activated as if the full amount was paid.
to fully validate the impact, I subscribed to the Ultimate plan and demonstrated that the vulnerability could be used to obtain a paid subscription at a manipulated price. I responsibly submitted my findings and supporting evidence to the company.
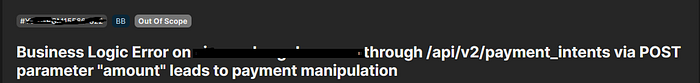
Although the payment flow was directly tied to the service, the checkout process was handled through an external billing domain, which led to a lengthy discussion with the triage team to demonstrate that the issue ultimately affected the main platform. Despite the technical impact, the report was classified as out of scope.
Security research often involves unexpected outcomes. Not every valid finding is accepted, and not every effort results in a reward. Still, each experience is part of the journey — an opportunity to learn, improve, and move forward.
Thank you for reading, and I wish you success in your security research .

