In this blog, I explain Lab 7 and Lab 8 from the PortSwigger Web Security Academy, both focused on Insecure Direct Object Reference (IDOR) vulnerabilities caused by user-controlled request parameters.
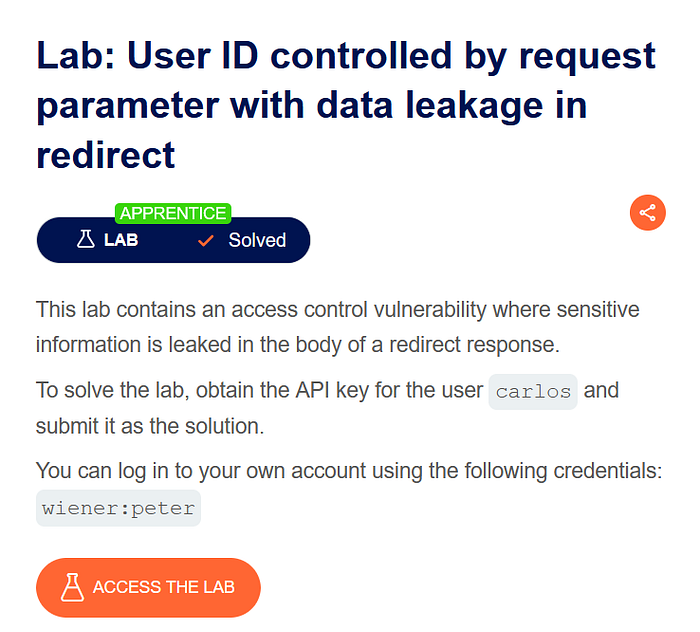
Lab 7: User ID Controlled by Request Parameter with Data Leakage in Redirect
Vulnerability Overview
This lab demonstrates how sensitive data can be leaked through redirect responses when a user ID is controlled via a request parameter.
Steps to Exploit
Log in using valid credentials:
- Username: wiener
- Password: peter
- Intercept the request in Burp Suite. The request appears as:
- GET /my-account?id=wiener
- Send the request to Repeater and change the parameter:
- GET /my-account?id=carlos
- Send the request. Even though access is restricted, the redirect response leaks Carlos's API key.
- Submit the API key to solve the lab.
Key Takeaway
Applications must ensure authorisation checks are enforced before redirects, not after.
Lab 8: User ID Controlled by Request Parameter with Password Disclosure

Vulnerability Overview
This lab exposes a critical password disclosure issue where sensitive credentials are returned in the response when user IDs are manipulated.
Steps to Exploit
Log in using:
- Username: wiener
- Password: peter
- Intercept the request:
- GET /my-account?id=wiener
- Change the parameter to:
- GET /my-account?id=carlos
- The response reveals Carlos's password in the HTML:
- <input required type="password" name="password" value="i01unxio46xc3shfvalo"/>
- Repeat the same step for the administrator account to obtain admin credentials.
- Log in as administrator and delete the user carlos.
- The lab is solved.
Why This Is Dangerous
- Passwords should never be sent back to the client.
- Storing passwords in plain text or exposing them in responses is a severe security flaw.
Conclusion
Both labs clearly demonstrate how IDOR vulnerabilities can lead to:
- Sensitive data leakage
- Password disclosure
- Full account takeover
Proper access control, server-side authorisation, and secure credential handling are essential to prevent such attacks.