When the Attack Lives Inside the Device
In Part 1, we explored printers as entry points.
In Part 2, we weaponized rogue printers for MITM attacks.
In Part 3, we hijacked DNS and launched internal phishing.
Now we go to the layer most defenders never check.
Firmware.
Because the most dangerous compromise isn't loud.
It's persistent.
🧠 What Is Firmware — Really?
Firmware is low-level software embedded directly into hardware devices.
It runs:
- Before your operating system
- Below your monitoring tools
- Outside your antivirus visibility
Devices like:
- Printers
- Routers
- Switches
- NAS appliances
- IP cameras
All run firmware.
And firmware is rarely audited.
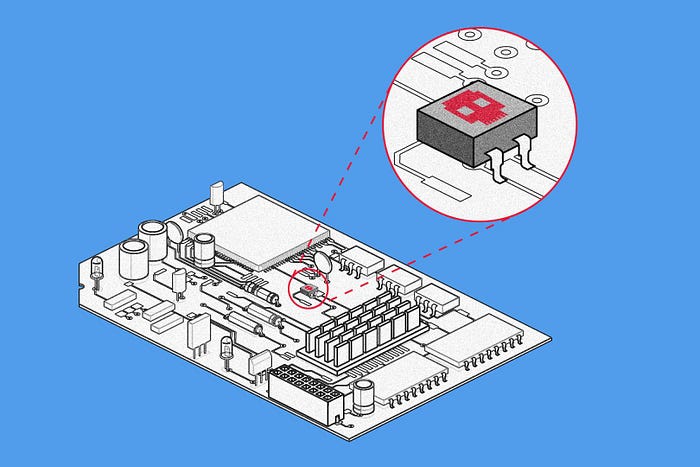
🧨 What Is a Firmware Implant?
A firmware implant is malicious code embedded directly into a device's firmware.
Once installed, it can:
- Survive reboots
- Survive factory resets (in some cases)
- Evade endpoint detection
- Maintain long-term persistence
Unlike malware on a laptop…
This lives inside infrastructure.
🖨️📡 How Network Devices Become Persistent Footholds

Here's a realistic attack chain:
1️⃣ Attacker gains admin access to printer/router 2️⃣ Uploads modified firmware (or exploits firmware update process) 3️⃣ Device reboots 4️⃣ Malicious implant loads silently 5️⃣ Device resumes normal behavior
Users see nothing unusual.
But the attacker now has:
- Remote access hooks
- Covert command-and-control channels
- Traffic monitoring capabilities
- DNS manipulation capabilities
- Credential harvesting opportunities
And because security teams rarely verify firmware integrity…
It persists.
🔍 Why Firmware Persistence Is So Dangerous
Because most incident response focuses on:
- Endpoints
- Servers
- Cloud logs
Very few teams:
- Reflash printers during incident response
- Verify router firmware hashes
- Check switch firmware integrity
If the implant remains…
The attacker can simply re-enter later.
Clean laptop.
Clean server.
Same compromised infrastructure.
🧰 Realistic Capabilities of a Firmware Implant
A compromised network device could:
- Open hidden management ports
- Create encrypted outbound tunnels
- Modify DNS responses
- Perform packet inspection
- Inject malicious responses into traffic
- Reinstall userland malware after cleanup
In advanced threat models, firmware persistence is the endgame.
Because hardware is trusted by default.
🔐 "But Don't Devices Verify Firmware?"
Some do.
Many don't.
Older devices often:
- Lack secure boot
- Lack firmware signature verification
- Allow unsigned firmware flashing
Even modern devices may have:
- Vulnerabilities in update mechanisms
- Downgrade attacks
- Bypassable verification checks
And small office / home office environments rarely validate firmware authenticity.
🛡️ How To Defend Against Firmware Persistence
✔ Change default credentials immediately ✔ Disable remote firmware updates ✔ Restrict admin interfaces to management VLANs ✔ Regularly update firmware from official sources ✔ Verify firmware hashes when possible ✔ Use hardware that supports secure boot ✔ Replace end-of-life network devices ✔ Include network hardware in incident response plans
Advanced environments should:
- Monitor outbound traffic from infrastructure devices
- Log firmware update events
- Maintain firmware baselines
- Segment infrastructure from user networks
🧠 The Strategic Lesson for Security Researchers
If you're doing red team research or bug bounty:
Look beyond web apps.
Ask:
- Can firmware be downgraded?
- Is update validation enforced?
- Is secure boot enabled?
- Can firmware be extracted and analyzed?
Infrastructure-level vulnerabilities often have massive impact.
Because persistence equals leverage.
🚨 Reality Check
True firmware implants are:
- More complex
- Higher effort
- Higher sophistication
They're not common in casual hacking.
But in:
- Targeted attacks
- Advanced persistent threats
- Corporate espionage
- Nation-state operations
Firmware persistence is absolutely part of the playbook.
🎯 The Bigger Pattern Across This Series
Part 1 — Entry Part 2 — Interception Part 3 — Manipulation Part 4 — Persistence
This is the lifecycle of infrastructure compromise.
Attackers don't just break in.
They:
- Gain trust
- Control traffic
- Manipulate perception
- And then make themselves permanent
Final Thoughts
Security isn't just about protecting applications.
It's about protecting the devices that shape the network itself.
Because when infrastructure is compromised…
Every layer above it becomes fragile.
Printers were just the beginning.
If you've followed this entire series:
👏 Respect. 💬 Drop your thoughts. ☕ Support the research: https://buymeacoffee.com/ghostyjoe