Disclaimer: This write-up is shared for educational purposes only. All testing was conducted on authorized targets under a responsible disclosure or bug bounty program. The intent is to help improve security awareness and highlight common implementation mistakes.
Introduction
This is Rahima, a Bug Bounty Hunter and Jr. Penetration Tester.
In this write-up, I will explain how I discovered a subdomain takeover vulnerability caused by an expired third-party service with a dangling CNAME record. This simple misconfiguration allowed me to claim control over a subdomain.
For privacy reasons, I will not disclose the organization's name and will refer to it as example.com throughout this article.
Recently, I participated in a bug bounty program where I discovered this vulnerability. let's walk through the process step by step.
Subdomain Enumeration
I started by enumerating subdomains of the target domain. Since there were many subdomains, I used a Chrome extension called Open Multiple URLs to quickly open all discovered subdomains in my browser.
This allowed me to review each subdomain manually and check whether the associated service was still active.
Identifying a Vulnerable Subdomain
While reviewing, I noticed that one subdomain returned a "Secure connection failed" error and wasn't loading properly.
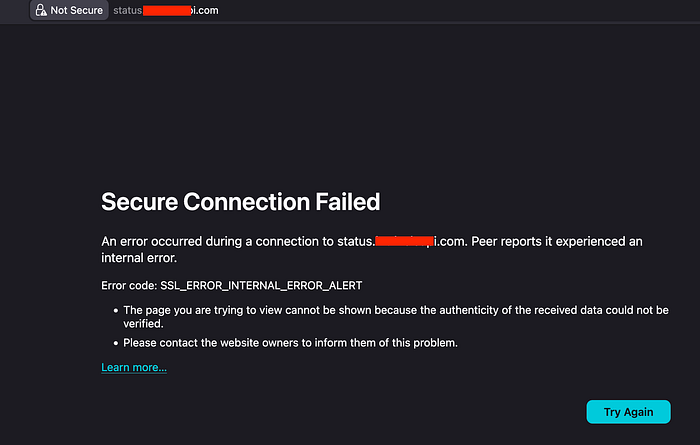
To investigate further, I checked its DNS configuration:
dig status.example.comThe result showed a CNAME record pointing to:
statuspage.betteruptime.comThis indicated that the subdomain was previously using the Better Uptime status page service. However, the service was no longer active, while the CNAME record was still pointing to Better Uptime.
Congratulations! its a subdomain takeover. xD
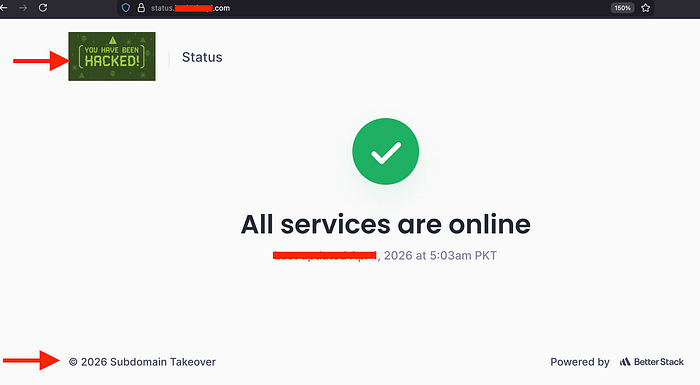
Taking Over the Subdomain
I quickly created an account on Better Uptime (Better Stack).
Then:
- Navigated to the Status Pages feature
- Added a custom domain:
status.example.com
The platform verified the CNAME and displayed:
The CNAME is configured correctly.

At this point, I had successfully claimed the subdomain.
Reporting the Bug
After confirming the takeover, I prepared a report with all necessary details and submitted it to the bug bounty program.
Outcome
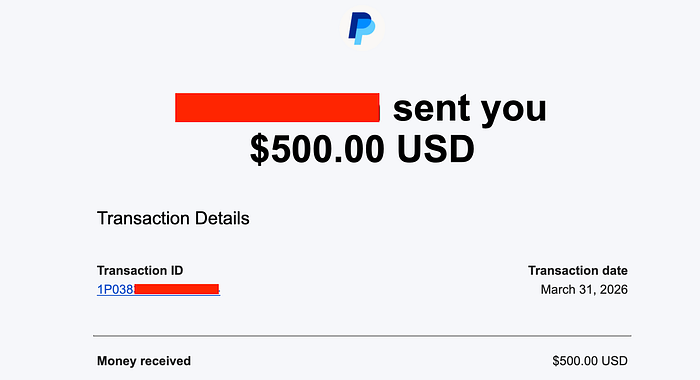
The security team responded quickly:
- The issue was fixed within 30 minutes
- Along with two additional reports, I was awarded a $500 bounty
Lets Connect? If you'd like to discuss projects, collaborations, or anything related to this article, feel free to connect with me on Instagram or LinkedIn.
