Exploring how TrinetLayer helps security researchers analyze attack surfaces, uncover hidden vulnerabilities, and experiment with real-world cybersecurity techniques.
What if an application's most significant vulnerability isn't concealed deep within the backend?… but sitting in plain sight in a JavaScript file that no one thought to look at? People don't realize how frequently this occurs.
People don't realize how frequently this occurs. An online application opens. Everything looks safe and secure. The dashboard loads properly, the login is functional, and the APIs respond as expected.
However, there is a minor oversight somewhere in the system, such as a misconfigured route, an exposed endpoint, or a vulnerability that is just waiting for the right payload.
This is how many actual security discoveries start. Not using tools for dramatic hacking. But with Interest.
Cybersecurity isn't just about running tools — it's about seeing what everyone else overlooks.
The Reality of Modern Cybersecurity Research
Many beginners think that all it takes to conduct cybersecurity research is to run scanners and watch for vulnerabilities to show up. The process is actually much more complex. To complete various tasks, security researchers usually use a variety of tools:
· Subdomain Discovery tools
· Vulnerability Database
· Repositories of payloads
· Tools for analyzing JavaScript
· Testing settings for Vulnerabilities
It can easily become overwhelming to manage these tools independently. While attempting to keep track of their discoveries, researchers frequently switch between various terminals, scripts, and scanning tools. Research is slowed down and sometimes significant vulnerabilities are overlooked as a result of this disjointed workflow.
That's exactly the problem TrinetLayer aims to solve.
What is TrinetLayer?
A platform designed for practical cybersecurity research is called TrinetLayer.

It offers a setting where security researchers can investigate vulnerabilities, examine attack surfaces, and test real-world security scenarios rather than merely concentrating on theoretical ideas. The platform brings multiple aspects of security research into a single ecosystem.
Researchers can carry out reconnaissance, vulnerability analysis, and payload testing in an organized workflow instead of juggling various tools and resources.
The objective is straightforward: Make cybersecurity research more accessible, structured, and useful.
Recognizing the Attack Surface
An attack surface exists in every digital system. This refers to every point at which an attacker could attempt to engage with or take advantage of an application. Examples consist of:
· Subdomains and domains
· Backend services and APIs
· exposed endpoints
· client-side scripts
· Integrations with third parties
Due to improper analysis of these entry points, there are numerous vulnerabilities. TrinetLayer facilitates more efficient exploration and monitoring of an application's attack surface by researchers.
Researchers can see potential vulnerabilities more clearly by mapping assets and locating possible entry points.
Discovering Vulnerabilities Faster
Another key component of security research is vulnerability intelligence. TrinetLayer includes tools that help researchers connect discovered assets with known security vulnerabilities. This includes analyzing potential issues related to common security flaws such as:
- Cross-Site Scripting (XSS)
- SQL Injection
- IDOR vulnerabilities
- CRLF injection
- dependency confusion
Having this information available within the research environment allows security professionals to investigate potential risks more efficiently.
Why JavaScript Analysis Matters
Modern web applications rely heavily on client-side JavaScript. These scripts often contain valuable information that can reveal hidden parts of an application. For example, JavaScript files sometimes expose:
- internal API endpoints
- application routes
- configuration details
- authentication logic
TrinetLayer includes tools that help researchers inspect JavaScript files and analyze them for potential security insights. This capability is particularly useful when investigating complex web applications and single-page frameworks.
Experimenting with Payloads Safely
Learning cybersecurity requires experimentation. However, testing exploit payloads directly against production systems can be risky. To address this challenge, TrinetLayer provides a controlled environment where researchers can test payloads and observe how vulnerabilities behave.
Researchers can experiment with different attack techniques while gaining a deeper understanding of how specific vulnerabilities work. This approach encourages hands-on learning rather than purely theoretical study.
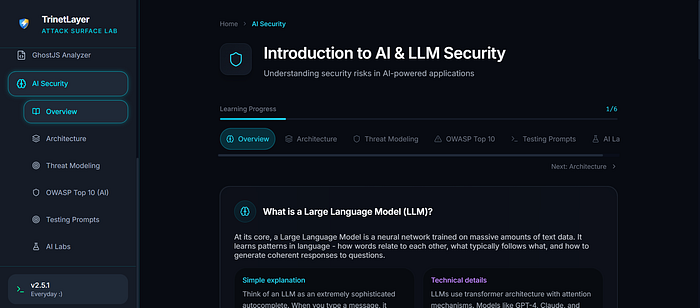
The Emerging Importance of AI Security
Artificial intelligence is becoming a major part of modern software systems. From chatbots to recommendation engines, AI models are now embedded into many applications. However, AI systems introduce entirely new security challenges.
These include issues such as:
- prompt injection attacks
- model manipulation
- unintended data exposure
Understanding these risks is becoming increasingly important for cybersecurity professionals. TrinetLayer includes resources focused on AI security research, helping researchers explore how these new types of vulnerabilities can appear in real systems.
Learning Cybersecurity Through Exploration
Cybersecurity is not a field that can be mastered through theory alone. Real understanding comes from experimentation. Researchers learn the most when they:
- investigate systems
- test hypotheses
- analyze application behavior
- experiment with vulnerabilities
Platforms like TrinetLayer encourage this exploratory approach. By providing tools, research environments, and security learning resources in one place, the platform helps researchers develop practical security skills.
The Future of Cybersecurity Research
As technology evolves, cybersecurity challenges continue to grow.
Applications are becoming more complex. Attack surfaces are expanding. AI systems are introducing new categories of risk.
To keep up with these changes, security researchers need environments that allow them to experiment, analyze systems deeply, and continuously learn.
Platforms like TrinetLayer represent a step toward this future.
They provide researchers with the tools and environments needed to explore vulnerabilities in a structured and practical way.
Final Thoughts
The internet is expanding all the time. Every new AI system, API, and application creates new chances for innovation, but it also creates new risks.
In the end, curiosity is what drives cybersecurity research. It starts with basic inquiries.
What would happen if this input was altered?
What is the purpose of this endpoint?
What is the real purpose of this script?
The biggest discovery can occasionally come from the smallest question. Frequently, the weakness existed from the beginning. All someone had to do was look closely enough to spot it.
Frequently Asked Questions
- What is TrinetLayer and who is it designed for?
TrinetLayer is a cybersecurity research platform designed for security researchers, bug bounty hunters, and students who want to explore vulnerabilities in a practical way. The platform provides tools and environments that help researchers analyze attack surfaces, investigate vulnerabilities, and experiment with real-world cybersecurity scenarios.
2. How does TrinetLayer help in discovering vulnerabilities?
TrinetLayer helps researchers identify vulnerabilities by providing features such as attack surface exploration, JavaScript analysis, and vulnerability intelligence. These tools help security professionals discover hidden endpoints, analyze application behavior, and test systems for potential weaknesses.
3. Why is attack surface analysis important in cybersecurity?
Attack surface analysis helps researchers understand all the possible entry points into an application. These entry points can include APIs, subdomains, exposed endpoints, or client-side scripts. By analyzing the attack surface, security professionals can identify areas where vulnerabilities are more likely to exist.
4. Can beginners use TrinetLayer to learn cybersecurity?
Yes. TrinetLayer supports hands-on learning by allowing users to experiment with vulnerabilities and understand how different attacks work in practice. This makes it useful not only for experienced researchers but also for beginners who want to develop practical cybersecurity skills.
5. Why is AI security becoming important in modern cybersecurity?
As artificial intelligence systems become part of modern applications, they introduce new types of security risks such as prompt injection attacks, model manipulation, and unintended data exposure. Understanding these risks is important for researchers who want to secure AI-powered systems and prevent misuse
