On 7 April 2026, Anthropic delayed the public release of its latest AI model. That rarely happens. The reason it gave was rarer still: the model had autonomously discovered thousands of previously unknown software vulnerabilities zero-days across every major operating system and every major web browser. One flaw it found had gone undetected for 27 years.
The model is called Claude Mythos. And while the cybersecurity industry has been busy debating whether it "changes everything," the organisations that actually need to act — startup financial investment firms — are largely not in that conversation.
They should be.
What Mythos actually is
Mythos Preview is not a specialist hacking tool. Anthropic did not build it for offensive security. It is a general-purpose AI model whose vulnerability-finding capability is an emergent consequence of broad improvements in reasoning and software engineering. That matters, because it means these capabilities are not exclusive to Anthropic — they will appear across the frontier model landscape as AI development continues.
Three capabilities define its threat relevance:
Vulnerability discovery. Mythos can identify unknown software flaws faster, more deeply, and across mixed technology stacks than human researchers — at a fraction of the cost.
Exploit creation. Engineers with no formal security training have used Mythos to generate working exploits from a single natural language prompt.
Vulnerability chaining. It can stitch together multiple low-severity flaws into a high-impact attack path — a technique that previously required senior offensive security expertise.
Anthropic's own red team demonstrated that Mythos could reconstruct plausible source code from closed-source software and then exploit vulnerabilities validated against the real systems. In response, Anthropic formed Project Glasswing — a consortium of major technology firms and over 40 critical infrastructure organisations — and committed $100M in AI usage credits to use Mythos for defensive purposes before any broader release.
That response is itself the signal.
The narrative the industry is getting wrong
The dominant framing in the market is binary: either Mythos is existentially catastrophic, or it is another AI announcement that will not touch most organisations. Both positions are wrong.
"This only affects critical national infrastructure." Startup investment firms run on cloud-hosted infrastructure, commercial SaaS platforms, and third-party APIs — the same software stacks Mythos has already scanned. The idea that a fintech startup sits below the threat threshold is not a risk assessment. It is wishful thinking.
"We're too small to be a target." Mythos changes the economics of attack, not just the capability. When vulnerability discovery and exploit creation are automated and cheap, the cost-benefit calculus of targeting a £50M AUM startup versus a major institution compresses significantly. Volume replaces selectivity. Attackers no longer need to choose their targets carefully when they can scan everything.
"Anthropic has restricted access, so we have time." Anthropic's restriction covers their model. Independent research has already shown that smaller, open-weight models — downloadable by anyone, with no safeguards — can replicate a meaningful portion of Mythos's vulnerability-finding capability. The window for response is measured in months, not years.
Why investment firms are specifically exposed
Three structural factors make this sector more vulnerable than most:
Dependency-heavy by design. Startups avoid legacy infrastructure but accumulate deep third-party dependencies — open-source libraries, payment APIs, cloud services. Each is a potential attack surface that Mythos-class tools can enumerate autonomously.
Regulated data, startup security budgets. FCA and DORA obligations demand enterprise-grade data protection. Security investment in early-stage firms rarely matches that exposure. The gap between regulatory obligation and actual security posture is wide — and now more exploitable.
Investor confidence is the product. For an investment firm, a breach is not an operational event. It is a capital event. Institutional investor trust, once lost to a publicised breach, is structurally difficult to recover. You cannot patch your way out of a trust deficit.
What to do (practically), now
The foundations required here are not new. Zero Trust architecture, continuous vulnerability management, secure-by-design engineering — these were the right answers before Mythos. What has changed is the grace period. Organisations that treated these as future priorities now have a compressed timeline.
ERA Framework
Leverage the ERA Framework. A structured response to AI-augmented cyber threats for startup investment firms.
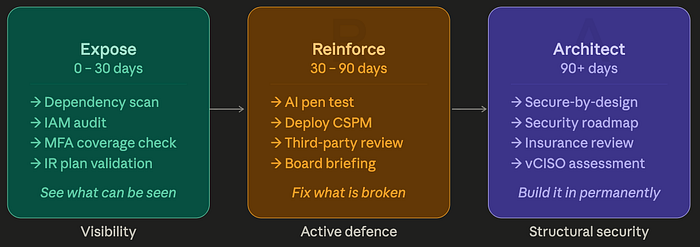
Mythos compresses the window between "technically possible attack" and "active threat." ERA is designed to move faster than that window closes.
Why the sequence is non-negotiable.
The logic above is simple: you cannot build on what you have not fixed, and you cannot fix what you cannot see. ERA is a sequence, not a menu — that is what makes it a framework rather than a list.
The framework is ERA — three phases, each with a single word that does real work:
- Expose (0–30 days) — you cannot fix what you cannot see. Dependency scans, IAM audits, MFA coverage, IR validation. The output is a clear picture of your actual attack surface, not your assumed one.
- Reinforce (30–90 days) — active defence against the specific threat class. AI-augmented pen testing, continuous CSPM, third-party risk, board alignment. The output is a programme calibrated to Mythos-era threats, not the previous generation.
- Architect (90+ days) — security built into how you operate, not bolted on after the fact. Secure-by-design engineering, a formal roadmap, insurance review, vCISO consideration. The output is a posture that holds without constant firefighting.
The point
Mythos did not invent the vulnerabilities it found. They were already there in software that has been running for decades, in systems that passed audits and penetration tests conducted at human speed.
What Mythos demonstrated is that the gap between "secure enough for human attackers" and "actually secure" is far larger than most organisations assumed. And it demonstrated that gap can now be measured automatically, cheaply, and at scale.
Startup investment firms were not built with that threat model in mind. That is not a criticism — it reflects the environment they were built in. But the environment has changed, and the security posture has to change with it.
The firms that move first will be better positioned not just operationally, but commercially. A credible, documented security programme is increasingly a due diligence requirement for institutional capital. Getting ahead of this is not just risk management. It is a competitive asset.
References
- Anthropic. Project Glasswing: Securing critical software for the AI era. April 2026. https://www.anthropic.com/glasswing
- AI Safety Institute (AISI), UK. Our evaluation of Claude Mythos Preview's cyber capabilities. April 2026. https://www.aisi.gov.uk/blog/our-evaluation-of-claude-mythos-previews-cyber-capabilities
- Turing Institute (CETaS). Claude Mythos: What does Anthropic's new model mean for the future of cybersecurity? April 2026. https://cetas.turing.ac.uk/publications/claude-mythos-future-cybersecurity
- AISLE. AI cybersecurity after Mythos: The jagged frontier. April 2026. https://aisle.com/blog/ai-cybersecurity-after-mythos-the-jagged-frontier
- Dark Reading. Anthropic's Mythos has landed: Here's what comes next for cyber. May 2026. https://www.darkreading.com/cybersecurity-operations/anthropic-mythos-cyber-what-comes-next
- Ventureburn. Finance leaders warn over risks of Mythos AI model. April 2026. https://ventureburn.com/finance-leaders-warn-over-risks-of-mythos-ai-model/
- CISO Platform. How Mythos signals cybersecurity disruption. May 2026. https://www.cisoplatform.com/profiles/blogs/how-mythos-signals-cybersecurity-disruption
- The Conversation / West Virginia University. Mythos AI is a cybersecurity threat, but it doesn't rewrite the rules of the game. May 2026. https://theconversation.com/mythos-ai-is-a-cybersecurity-threat-but-it-doesnt-rewrite-the-rules-of-the-game-281268