🎯 The Target (Redacted 👀)
So I found this "secure" portal handling:
- KYC 📄
- Passports 🛂
- Compliance data 📊
And of course, it had:
👉 Email login 👉 MFA
So naturally I said:
"Yeah… I'm not getting in."
5 minutes later: "I'm definitely getting in." 😭
🧠 Phase 1: OSINT — LinkedIn is the Real Hacker Tool
I needed a valid user.
So I did elite-level reconnaissance:
👉 Open LinkedIn 👉 Find employee 👉 Guess email
That's it.
OSINT tools? Yes. Brain? Optional.
🔍 Phase 2: View Source — Because Curiosity Kills… Security
Opened login page → View Source
Nothing interesting.
But then I remembered:
👉 "This is Next.js… there HAS to be chunk files."
So I grabbed a JS file and ran:
grep -oEi '"/[a-z0-9/_-]{3,}"'And suddenly…
💥 Main character moment
/api/setup-mfa
/api/complete-mfa-setupMe: "Why are these public…?" Also me: "Don't ask questions. Exploit." 😌
🚨 Phase 3: The "No Way This Works" Request
I sent:
POST /api/setup-mfa
{
"email": "target@company.com"
}Response:
- Secret ✅
- QR Code ✅
- Happiness ❌ (because this should NOT happen)
At this point I knew… This wasn't a bug. This was a lifestyle choice by the backend.
🧪 Phase 4: QR Code = Unauthorized Life Access
Converted base64 → QR → scanned it.
Now my phone was generating OTPs for someone else's account.
Microsoft Authenticator: "Welcome 👋R" Me: quot;I don't even belong here…" 💀
😭 Phase 5: Reality Check (It Didn't Work)
Tried logging in.
❌ Failed.
And I was like:
"Okay… security team did SOMETHING at least."
Almost gave up.
Closed terminal.
Opened Instagram,Started scolling.
Then…
⚡ Phase 6: Hacker Instinct Kicks In
Brain:
"You found TWO endpoints… don't be lazy."
Right.
/api/complete-mfa-setupEndpoint name: complete-mfa-setup Me: "Oh so you WANT me to finish it?" 😏
🧠 Phase 7: Final Boss Fight
From JS clues:
secretverificationCode
So I sent:
POST /api/complete-mfa-setup
{
"email": "target@company.com",
"secret": "<secret>",
"verificationCode": "<OTP from my phone>"
}💥 BOOM.
"MFA setup completed successfully"Me staring at screen: "This is why we can't have nice things." 😭
🏁 Phase 8: The "Wait… I'm Actually In" Scene
Login again:
- Email ✅
- OTP (mine 😎) ✅
And…
🚪 ACCESS GRANTED
💀 What I Found Inside
- Passports 🛂
- KYC docs 📄
- Compliance data 📊
Basically:
👉 "Congratulations, you've unlocked GDPR violation DLC." 🎮
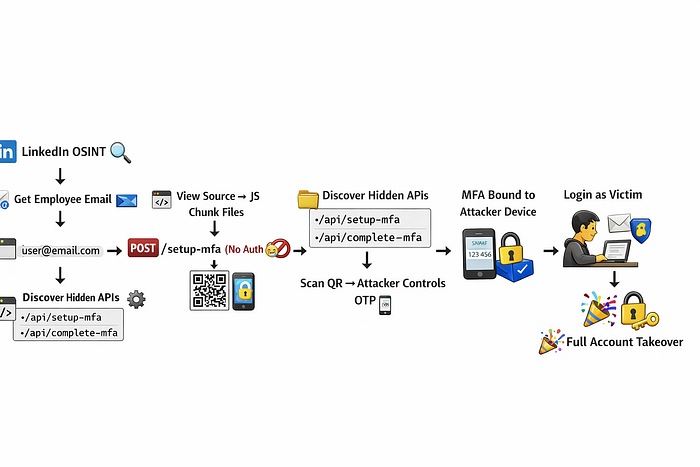
📊 Attack Flow (Visual)
⚠️ Why This Is INSANE
This is basically:
- ❌ MFA without authentication
- ❌ Identity not verified
- ❌ Backend trusting anyone
- ❌ Complete auth bypass
All you need:
👉 Email address
That's it.
🧯 Responsible Disclosure
Before anyone panics:
- No data touched ❌
- No data downloaded ❌
- Reported responsibly ✅
Ethical hacker mode: ON Chaos mode: OFF
🧠 Developer Takeaways
If you're building auth systems:
- 🔒 NEVER allow MFA setup without login
- 🔒 Always bind actions to session
- 🔒 Validate user identity server-side
- 🔒 Stop trusting frontend like it's your best friend
🎬 Final Thoughts
Time taken:
⏱️ ~10 minutes 🧠 1 brain cell 📧 1 email
Impact:
💀 Total account takeover
MFA is supposed to STOP attackers… not onboard them.
"At this point, the only factor in Multi-Factor Authentication… was me."

