Introduction
A security researcher spent eleven months learning every reconnaissance technique available. He could enumerate subdomains with precision, fingerprint technology stacks accurately, map attack surfaces comprehensively, and chain together vulnerability discovery workflows that would impress anyone watching. His technical foundation was genuinely impressive by any reasonable measure.
His bug bounty earnings over those eleven months were almost nothing.
Meanwhile, someone in the same online community — someone who openly described their technical knowledge as intermediate at best — was submitting valid reports consistently and earning meaningful payouts across multiple programs every single month.
The difference was not technical depth. Both people understood ethical hacking fundamentals well enough to find real vulnerabilities. The difference was something that most bug bounty content, most courses, and most community discussions almost never address directly.
Here is the myth that keeps technically skilled people from earning what their knowledge should produce: that bug bounty success is primarily a function of how many vulnerabilities you can find across how much attack surface you can cover.
The real issue is not reconnaissance breadth. It is program selection intelligence — knowing which programs to work, why, and in what sequence. And most hunters never develop this skill because nobody told them it was the skill that mattered most.
Why Program Selection Is the Skill Nobody Teaches
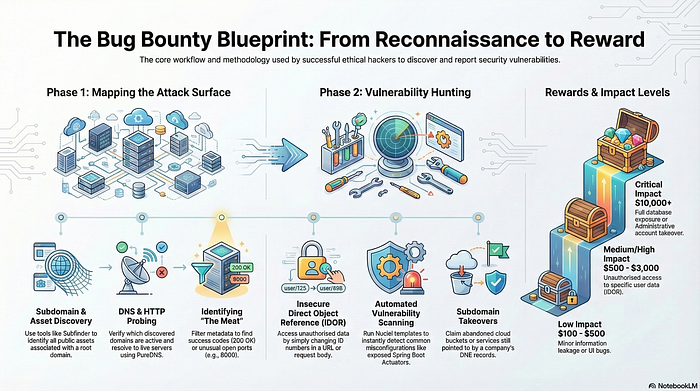
Walk into any bug bounty learning community and the conversation is dominated by technical content. Which reconnaissance tools to use. Which vulnerability classes to learn. Which automated workflows to build. How to chain findings into higher-severity reports. All of this is genuinely useful knowledge.
What is almost never discussed with the seriousness it deserves is the upstream decision that determines whether all that technical skill produces financial results: which programs are actually worth working.
Bug bounty programs are not equal. They differ enormously in the density of remaining undiscovered vulnerabilities, the quality of their triage processes, the specificity and fairness of their scope definitions, the responsiveness of their security teams, the reasonableness of their duplicate rate, and the alignment between their reward structure and the vulnerability classes most likely to exist in their applications.
A hunter with moderate technical skill working a well-selected program will consistently outperform a hunter with exceptional technical skill working a poorly selected one. Not because skill does not matter — it does, significantly. But because skill applied in the wrong environment produces far less than skill applied in the right one.
The intellectual insight here is uncomfortable for people who have invested heavily in technical skill development: program selection is a form of strategic intelligence that operates upstream of technical skill and multiplies or diminishes its value. Excellent reconnaissance techniques applied to a program that has been heavily tested by large numbers of experienced hunters for years will produce mostly duplicates and out-of-scope findings regardless of how technically sophisticated the approach is.
A concrete example that makes this visible: a hunter chooses between two programs. The first is a large, well-known technology company that has been running a public bug bounty program for several years and has a large, active hunter community working it continuously. The second is a mid-sized company that recently launched a private program, operates in a domain with historically poor security practices, and has a smaller community of hunters with access to it. The technical challenge of finding vulnerabilities in the first program is significant — the easily discoverable issues have been found and reported many times over. The second program likely has similar or greater density of vulnerabilities, a smaller hunter population competing to find them, and a triage team that is seeing fewer reports. Same technical approach. Dramatically different likely outcomes.
The Reconnaissance Depth Trap That Kills Momentum
Once a program has been selected thoughtfully, the next place where most hunters lose significant value is in the quality of reconnaissance — specifically, in the common mistake of confusing breadth of reconnaissance with depth of understanding.
Most bug bounty reconnaissance guidance emphasizes comprehensive surface coverage. Find all the subdomains. Map all the endpoints. Identify all the technologies. Build the most complete picture of the attack surface possible before beginning active testing. This guidance is not wrong — comprehensive surface awareness is genuinely valuable — but it creates a specific trap when it becomes the primary goal rather than the means to an end.
The trap is this: comprehensive surface mapping tells you what exists. It does not tell you where the interesting vulnerabilities are most likely to live. And the time required to achieve truly comprehensive surface coverage of any significant program is enormous — time that, spent on deep investigation of the most promising areas, would produce significantly better results.
The hunters who consistently find high-value vulnerabilities in competitive programs are not the ones with the most comprehensive attack surface maps. They are the ones who use reconnaissance to answer a specific strategic question: given what this application does, who its users are, what data it handles, and how it was likely built, where are the most interesting places to invest deep manual investigation?
That question requires understanding the application from a business and architectural perspective, not just cataloguing its technical surface area. It requires reading the application's documentation, understanding its core user flows, identifying the operations that handle the most sensitive data or the highest-privilege actions, and making informed judgments about where implementation complexity creates the conditions for security assumptions to be wrong.
This strategic reconnaissance — reconnaissance that is in service of a specific analytical question rather than in service of comprehensive coverage — produces a prioritized investigation agenda that shallow, broad reconnaissance never generates. And that agenda is what directs the subsequent testing toward the areas where high-value findings actually live.
The Severity Gap Between What Hunters Find and What Programs Pay For
One of the most consistent sources of frustration in bug bounty programs — and one that technical skill development alone cannot address — is the gap between the vulnerabilities hunters find and the vulnerability classes that programs actually reward at meaningful levels.
Most hunters, particularly early in their development, find vulnerabilities that are technically real but practically low-impact. Missing security headers. Informational disclosures that require significant chaining to produce actual risk. Self-XSS vulnerabilities that require interaction from the victim that makes them essentially non-exploitable in realistic conditions. Clickjacking on pages that do not handle sensitive operations. These findings are valid in a technical sense and many programs will accept them, but they are rewarded at the bottom of the bounty scale for the same reason — their real-world risk is minimal.
The highest bug bounty payouts are concentrated in a relatively small set of high-impact vulnerability classes: authentication and authorization bypass, significant data exposure, server-side vulnerabilities that allow meaningful access or control, and vulnerability chains that combine individually low-severity findings into genuinely high-impact attack scenarios. These vulnerability classes are harder to find not primarily because they require more technical skill to exploit once identified, but because finding them requires the specific kind of deep application understanding described in the previous section.
The intellectual insight is this: the difficulty in finding high-value vulnerabilities is less technical than strategic. It is less about knowing how to exploit the vulnerability once you find it and more about knowing where to look, what questions to ask about application behavior, and how to recognize the conditions that indicate a high-value vulnerability might be present.
A practical illustration: a hunter is testing an application that allows users to generate and download reports containing their own data. A surface-level approach might test the report generation endpoint for injection vulnerabilities — a technically reasonable approach. A deeper approach asks: is the report generation tied to the requesting user's identity server-side, or does it use a report identifier that any authenticated user could supply? If the latter, the vulnerability is an insecure direct object reference that allows any user to download any other user's report — a potentially significant data exposure that the surface-level technical approach would miss entirely. Finding it requires understanding what the endpoint does from a business logic perspective, not additional technical sophistication.
Why Report Quality Determines Payout More Than Finding Quality Does
There is a final dimension of bug bounty success that almost no technical training addresses, and its neglect is responsible for a meaningful proportion of the difference between hunters who consistently earn well and hunters who find valid vulnerabilities and receive smaller payouts than their findings merit.
Report quality is not a soft skill or a secondary consideration. It is a direct financial variable that influences the payout assigned to any given finding by the program's triage team. Programs that have the authority to reward at the higher end of their bounty range for a given severity level — and most do, because severity ranges have floors and ceilings — make that judgment partly based on the quality of the report accompanying the finding.
A high-quality report does several specific things that a low-quality report does not. It demonstrates the real-world impact of the vulnerability clearly and specifically, framing it in terms of what an actual attacker could accomplish rather than the technical mechanics of the vulnerability in isolation. It provides a complete, reproducible proof of concept that allows the triage team to verify the finding without ambiguity or additional investigation. It suggests a specific remediation approach that demonstrates genuine understanding of why the vulnerability exists and what architectural change would prevent it. And it accurately assesses the severity of the finding — neither overclaiming severity in ways that will be downgraded on review nor underclaiming it in ways that leave legitimate reward on the table.
Hunters who write reports that make the triage team's job easier — that arrive with clear impact framing, complete reproduction steps, and thoughtful remediation guidance — build a different kind of relationship with programs than hunters who submit technically valid but poorly documented findings. That relationship has compounding value over time. Programs with private invite structures preferentially invite hunters whose reports have demonstrated this quality. Triage teams for whom a specific hunter's submissions are reliably high quality resolve those submissions faster and with less back-and-forth. The financial and professional returns accumulate in ways that go far beyond any individual finding's payout.
The skill of writing excellent security reports is learnable and specific. It is also almost entirely absent from most bug bounty technical training — which focuses on finding vulnerabilities and almost not at all on the communication of what was found in ways that maximize its recognized value.
Engagement Loop
In 48 hours, I will reveal a simple program selection checklist that most bug bounty hunters skip entirely before they start reconnaissance — and skipping it is the single most consistent reason technically capable hunters spend months finding vulnerabilities that produce almost no financial return.
CTA
If this reframed how you are thinking about where bug bounty success actually comes from and what skills deserve more of your development time, follow for more honest analysis of the gaps between what the community talks about and what the highest-earning hunters are actually doing differently. Share this with someone who is putting in serious technical work without seeing the financial results they expected — this might be the conversation that redirects everything.