Description : Vulnerability allow a authenticated user whith low privilages upload a malicious WAV file that could lead to remote arbitrary file disclosure and server-side request forgery (SSRF).
Difficulty : Easy
Note : All of the content and screenshot it's from https://tryhackme.com/
Room : https://tryhackme.com/room/wordpresscve202129447
Task 1 Introduction
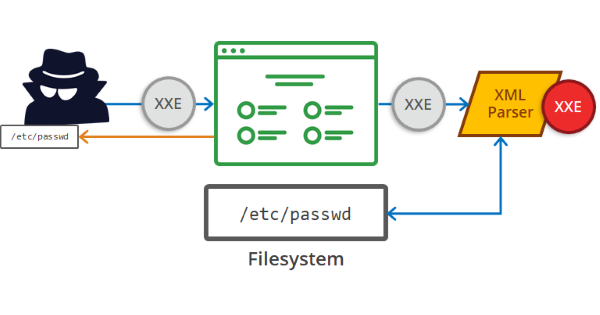
An XXE vulnerability consists of an injection that takes advantage of the poor configuration of the XML interpreter. This allows us to include external entities, enabling us attack to applications that interpret XML language in their parameters. We'll explore a recent XXE vulnerability, albeit one that comes with some situational caveats.
Researchers at security firm SonarSource discovered an XML external entity injection (XXE) security flaw in the WordPress Media Library. The vulnerability can be exploited only when this CMS runs in PHP 8 and the attacking user has permissions to upload media files. Take note of the latter condition as we walk through an example of exploiting this vulnerability below.
Impact
- Arbitrary File Disclosure: The contents of any file on the host's file system could be retrieved, e.g. wp-config.php which contains sensitive data such as database credentials.
- Server-Side Request Forgery (SSRF): HTTP requests could be made on behalf of the WordPress installation. Depending on the environment, this can have a serious impact.
Exploiting the vulnerability
A WordPress site affected by this vulnerability has been identified via the WPScan tool. We can see the output of this tool below from our enumeration.

In this example, we have identified that the author user uses weak credentials.
user: test-corp
password: test
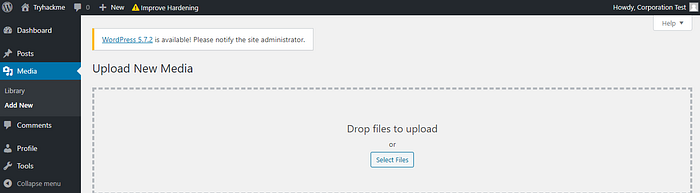
In this case, we can see that this user has permission to upload media files. We can leverage this to upload a reverse shell!
Now launch an http server in the same directory as the dtd file.
php -S 0.0.0.0:PORT
Now upload the malicious .wav to the WordPress application!
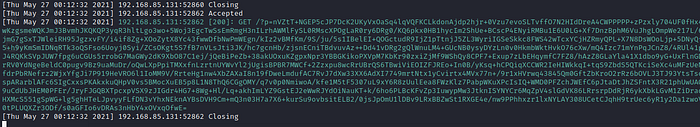
Once you've uploaded the .wav file, you should see the following request in your HTTP server logs. Note, in order to exfiltrate data effectively we've used Zlib for encoding.
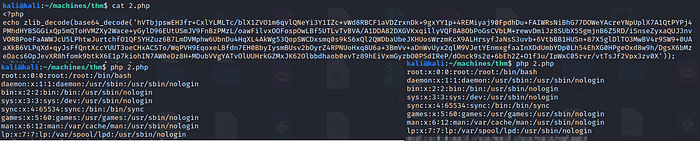
For practice (and the sake of this example), let's use PHP to decode this blurb! Create a .php with the following code, just be sure to copy and paste the base64 returned from the WordPress server where we have 'base64here' in the example code.
<?php echo zlib_decode(base64_decode('base64here')); ?>
Run the php file with the following command: php FILENAME.php
Answer the questions below
- ) Read the above.
Answer : No Answer needed
Task 2 Ready Set Go
Please, help us to compromise the system using the information provided in the introduction task.
Are you able to complete the challenge?
Answer the questions below
1.) Use the vulnerability CVE-2021–29447 to read the wordpress configuration file.
Answer : No answer needed
2.) Based on the results of #1, what is the name of the database for WordPress?
Answer : wordpressdb2
3.) Based on the results of #1, what are the credentials you found?
example: user:password
Answer : thedarktangent:sUp3rS3cret132
4.) Enumerate and identify what is the dbms installed on the server?
Answer : mysql
5.) Based on the results of #4, what is the dbms version installed on the server?
Answer : 5.7.33
6.) Based on the results of #4, what port is the dbms running on?
Answer : 3306
7.) Compromise the dbms, What is the encrypted password located in the wordpress users table with id 1??
Answer : $P$B4fu6XVPkSU5KcKUsP1sD3Ul7G3oae1
8.) Based on the results of #7, What is the password in plaint text?
Answer : teddybear
9.) Compromise the machine and locate flag.txt
Answer : thm{28bd2a5b7e0586a6e94ea3e0adbd5f2f16085c72}


Thanks for read my blog sir ;)
Lawvye