Hi! Today we will talk about domains, subdomains and subdomain enumaration. If want to understand what the subdmains are we have to get to the root of subdomain.
What Is A Domain?
Let's think everyone's name is a combination of random numbers. Could you remember name of your best friends or your famile members? It would be hard right? All the world use nicknames instead of our names in this situation. Because they would be more remembered and original.So what does this have to do with domain?
Domains are serves a similar purpose to nicknames. IP addreses are combination of 32 bit. So if you try to remember all the IP addresses you use your brain would be soup of 1's and 0's. Because of that we use domains. Domains are the URL strings that we use in real life. like google.com, youtube.com, nist.gov.
So What Is A Subdomain?
Let's assume we have all publicly available IP addresses and enough domain names to match those IP addresses and we want another domain name for our corporations mail server what should we do in this situation? We must match an IP address with another domain. So we use subdomains. Subdomains are the domains that intact with root domain and matched with the same IP address like apple.apple.com, aws.amazon.com, eu.wikipedia.org.
So we know domain and subdomain concepts. Let's learn Subdomain Enumaration.
What is Subdomain Enumaration And How To Make It?
Subdomain enumeration is the process of identifying all subdomains for a given domain. This can be useful for a variety of purposes, such as identifying potential targets for an attack, or simply for organizational purposes. It also helps to broader the attack surface(I'll write about an artical about attack surfaces), find hidden applications, and forgotten subdomains.
To identify potential targets for an attack: By enumerating all subdomains, you may be able to find subdomains that are less well protected than the root domain or the target organization, making them more vulnerable to attack.
To gain insights into the organization: Subdomain enumeration can give you insights into how an organization is structured, what services they offer, and so on. This information can be valuable when performing reconnaissance for a penetration test or security assessment.
To find misconfigured DNS entries: In some cases, organizations may have misconfigured DNS entries that reveal sensitive information, such as internal IP addresses.
There are lots of tools that you can subdomain enumaration. We'll delve deep into one of them and discuss a few others superficially.
SUBFINDER
Subfinder is an open source tool to detect valid subdomains for the given websites using passive online resources. It has a simple architecture and with this feature it is highly optimized for speed. Because it's passive, I'd recommend it for pentesters to use for stealth purposes.
So how do we use?
It has lots of flags to use but we will focus the most import ones.
- -d → domains to find subdomains for
- -rl → maximum number of http requests to send per second
- -f → subdomain or list of subdomain to filter (file or comma separated)
- -o → file to write output to
- -silent → show only subdomains in output
- -v → show verbose output
Let's take example scenario. We have website for hack its vulnweb.com. It has lots of vulnerabilities for hackers that they want to improve themselves. Let's see what subdomains it has.
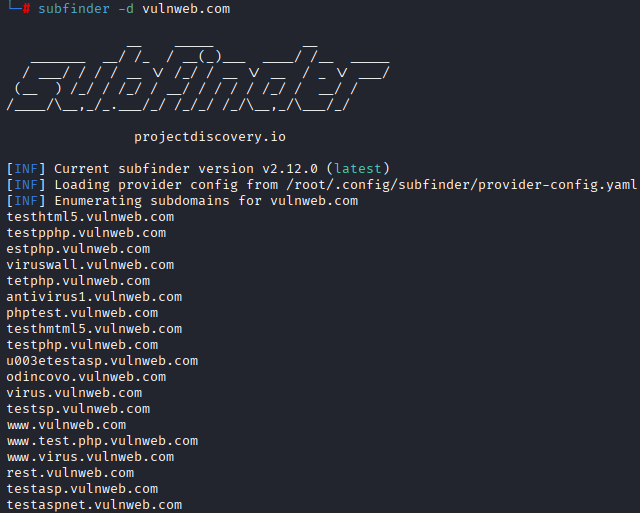
We are looking for websites that is alive to take informations. As you can see there is a API website link. If we look inside, we will come across a scene like this.
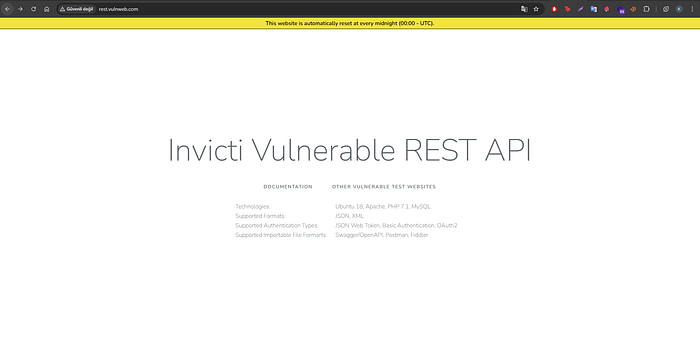
There is text that it says documentation. If we click on it we will reach to API's documentation.
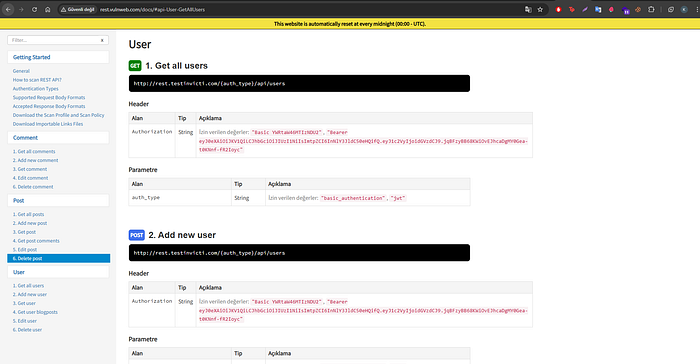
So if we use something like Postman to make calls on API. We can dump all user informations; create, edit or delete users and post etc. If we came across something like that in real life that would be dangerous for website owner. The owner may face legal proceedings and penalties for legal reasons.
Here is the Subfinder's GitHub URL for those who want to learn more
And if someone wants to look for more tools they can search for theHarvester, Sublist3r, and Knockpy.
See you in other documents. Thanks for reading and don't forget to stay silent!

