Lab Objective
This is an Apprentice-level lab from the Cross-Site Scripting (XSS) section in PortSwigger Web Security Academy.
The comment functionality contains a stored XSS vulnerability. The goal is to submit a comment that calls the alert() function when any user (including the simulated victim) views the blog post.
Steps to Exploit
- I opened the lab and navigated to a blog post that has a comment section.
Screenshot 1: Blog post page with comment form.
- I entered the following payload in the comment box:
<script>alert(1)</script>I also filled in a name, email, and website (any values work).
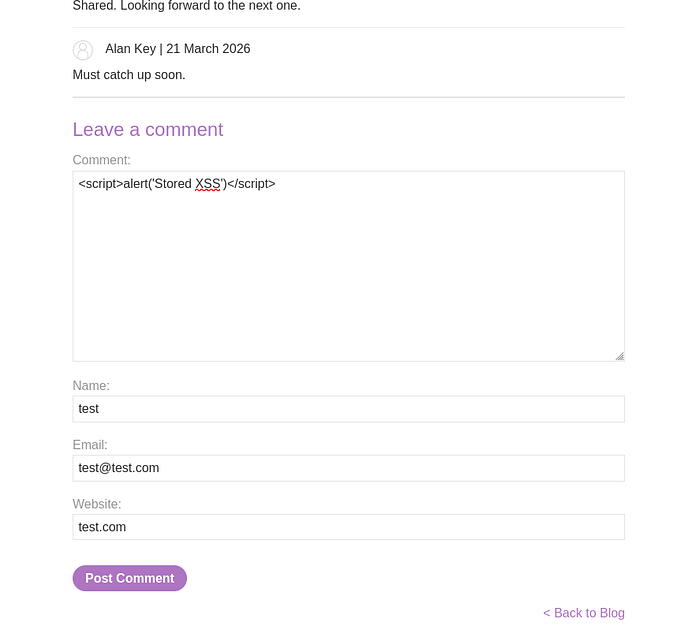
- Clicked Post comment.
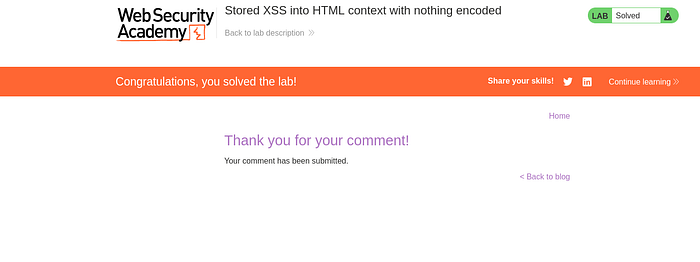
- I went back to the blog post. The comment was stored on the server and displayed to users without any encoding. The malicious script executed immediately, popping the alert box.

How the Vulnerability Works
In Stored XSS (also called Persistent XSS), the malicious payload is saved in the application's database and served to every user who views the affected page.
The application took the comment input and inserted it directly into the HTML page without escaping special characters:
Unsafe behavior:
HTML
<div class="comment">
<p>[user comment]</p>
</div>After submitting <script>alert(1)</script>, it became executable JavaScript for anyone viewing the blog post.
This makes Stored XSS more dangerous than Reflected XSS because the attack persists and affects multiple users automatically.
Exploitation Summary
- Vulnerability Type: Stored XSS (HTML context with nothing encoded)
- Payload Used: <script>alert(1)</script>
- Tool: None required (solved directly in the browser)
Mitigation
- HTML-encode all user-generated content before displaying it.
- Use proper escaping functions depending on the output context.
- Sanitize input on arrival and apply output encoding on every render.
- Implement a strong Content Security Policy (CSP) to limit script execution.
This lab clearly shows why comments, reviews, and user-generated content are high-risk areas if not properly sanitized.
Continuing my PortSwigger Web Security Academy series.
#XSS #StoredXSS #CrossSiteScripting #PortSwigger #WebSecurityAcademy #WebPenetrationTesting #BugBounty #LearningInPublic