Advanced Persistent Threats (APTs) are among the most sophisticated forms of cyber adversaries. They are typically state-sponsored or wellresourced groups conducting long-term campaigns targeting specific sectors or organizations for espionage, sabotage, or influence operations. Unlike financially motivated cybercriminals, APTs focus on stealth, persistence, and intelligence collection over extended periods.
The MITRE ATT&CK framework provides a globally recognized taxonomy for analyzing and comparing adversarial tactics, techniques, and procedures (TTPs). It enables defenders to understand attacker behavior, detect commonalities, and prioritize mitigation strategies.
This writeup compares APT3 (Gothic Panda / BuckEye) — attributed to China — and APT29 (Cozy Bear / Nobelium) — attributed to Russia — highlighting their distinct and overlapping operational behaviors, motivations, and implications for global cybersecurity defense.
Unlike traditional cybercriminals, APT groups focus on:
- Stealth - Persistence - Intelligence collection

🐼 APT3 (Gothic Panda / BuckEye)
APT3 is a Chinese state-sponsored threat group active since at least 2010. It is believed to operate under the umbrella of China's Ministry of State Security (MSS), particularly through its regional security bureaus. The group has targeted industries vital to China's economic and military development.
Primary Objectives:
- Intellectual property theft - Military intelligence collection - Industrial espionage
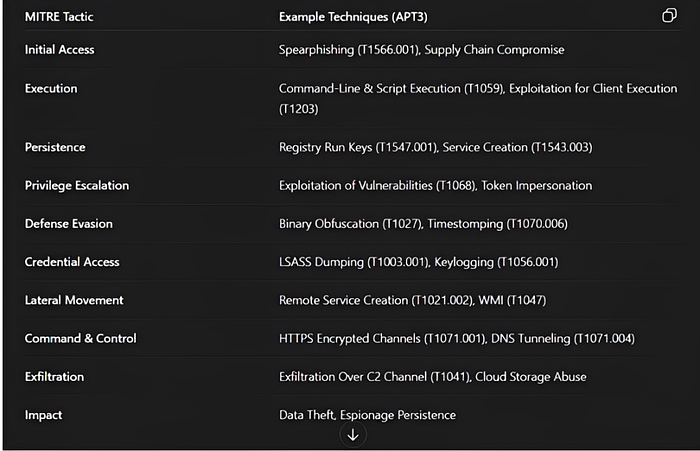
Technical Capabilities & TTPs: APT3's attack chain aligns closely with the MITRE ATT&CK Enterprise matrix.
APT3 heavily relies on:
- Spear-phishing for initial access - Credential dumping for privilege escalation - PowerShell execution for automation - Encrypted command and control communication - Data exfiltration for intelligence theft
Notable Operations :
Operation Double Tap (2013–2015): Targeted Western aerospace firms using zero-day vulnerabilities in Adobe Flash and Internet Explorer.
NSA Exploit Reuse (2016): After the Shadow Brokers leak, APT3 integrated portions of NSA's "EpMe" and "DoublePulsar" tools into its own malware suite, demonstrating rapid capability adaptation.
🐻 APT29 (Cozy Bear / Nobelium)
APT29 is attributed to Russia's Foreign Intelligence Service (SVR) and has been active since at least 2008. The group is known for highly covert cyber espionage operations targeting Western governments, diplomatic missions, and IT infrastructure.
Primary Objectives:
- Government espionage - Political intelligence - Supply chain attacks
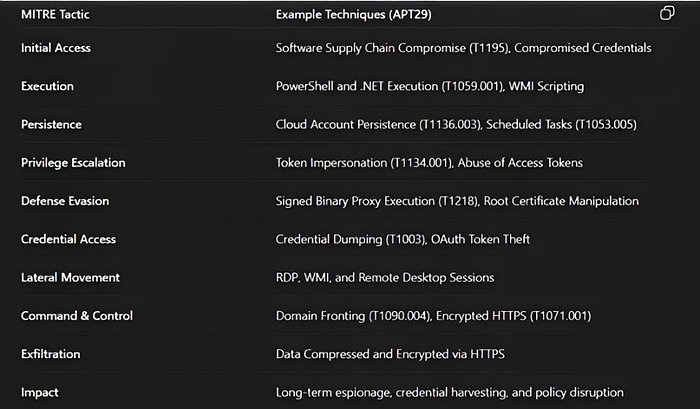
Technical Capabilities & TTPs: APT29's attack chain aligns closely with the MITRE ATT&CK Enterprise matrix.
APT29 heavily relies on:
- Supply chain compromise - Token theft - Cloud persistence - Encrypted command and control
Notable Operations :
SolarWinds Supply Chain Compromise (2020): Infiltrated software updates of SolarWinds Orion, impacting over 18,000 organizations including U.S. federal agencies.
COVID-19 Vaccine Espionage (2020): Targeted vaccine research facilities in the U.S., U.K., and Canada during the pandemic.
⚔️ Common Techniques
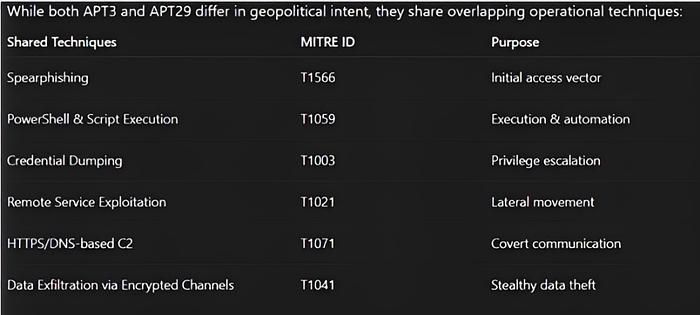
These overlaps demonstrate a convergence of tradecraft, likely driven by shared global trends in cyber operations, tool sharing across underground communities, and mutual observation of successful adversary TTPs.
In your embedded SVG diagram, the comparative visualization illustrates:
- APT3 shows dominance in Exploitation, Persistence, and Privilege Escalation tactics - APT29 shows dominance in Defense Evasion, Lateral Movement, and Cloud-based Command and Control (C2) - Both APT3 and APT29 share common overlap in Initial Access and Exfiltration phases
🎯 Conclusion
APT3 and APT29 represent two of the most capable and enduring state-backed APT actors.
- APT3 demonstrates China's focus on industrial and strategic espionage, leveraging custom malware and rapid exploitation of vulnerabilities - APT29 exemplifies Russia's mastery of stealth, deception, and supply-chain infiltration to conduct long-term intelligence operations
Defenders must therefore evolve from reactive measures to intelligence-driven security, leveraging frameworks like MITRE ATT&CK for continuous adaptation and proactive defense.
👨💻 About the Author
"Defenders must therefore evolve from reactive measures to intelligence-driven security, leveraging frameworks like MITRE ATT&CK."
Pranav More Cybersecurity Researcher | Bug Bounty Hunter | VAPT Enthusiast LinkedIn

