When I first started learning about information security and made the decision to start writing, I knew I wanted to be consistent with it and truly document my journey.
So, coming to the end of this series?
It feels really good.
And I'm proud to say, this is the end of the OWASP series, but definitely not the end of documenting my learning journey.
So… let's wrap this up nicely.
OWASP #9: Security Logging & Monitoring Failures
Let's start here.
In simple terms, this vulnerability means:
Security events are not logged, monitored, or acted on.
Basically, something goes wrong… And no one notices.
A quick real-life parallel
I run a gift business that's very dear to my heart!
After busy seasons, I like to sit down and write things out — essentially log what happened:
- lessons learned
- What didn't go well
- What I could do better
Ideally, I do this during or right after the season ends.
But… life happens. Sometimes I delay it.
And the period between when the season ends and when I finally sit down to reflect? That gap is critical.
And believe it or not…
The same kind of "gap" exists in systems.
When events aren't logged properly, or no one is actively monitoring them, important incidents can slip through unnoticed, and that gap can create serious problems.
- Suspicious activity can go unnoticed
- attackers can move freely
- Problems are discovered way too late
In today's world, I genuinely believe every business should have some form of monitoring system in place to prevent situations like this.
So, what are the consequences?
- Breaches go unnoticed
- It becomes very difficult to investigate what happened (even figuring out where to start becomes a problem!)
- Response to incidents is slow or ineffective
By the time you realize something is wrong… It's already been going on for a while.
How do we prevent this?
One key solution is centralized logging using a SIEM.
Now let's break that down simply.
SIEM = Security Information and Event Management
It's basically a system that:
- collects logs (records of activity) from different parts of your system
- brings them into one place
- and helps monitor them in real time
Think of it like a control room.
Instead of checking different places one by one, everything is visible in one spot, and alerts can be raised when something unusual happens.
OWASP #10: Server-Side Request Forgery (SSRF)
And now… the final one.
Don't let the name scare you — it's simpler than it sounds.
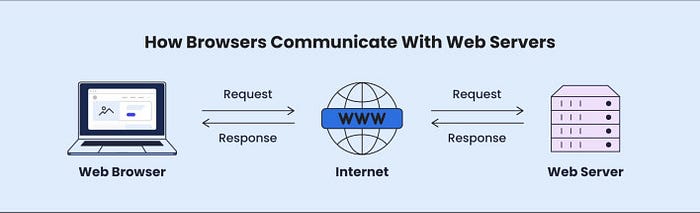
First, a quick foundation
Whenever you use a website, your browser is constantly making requests.
For example:
- loading an image
- fetching product details
- retrieving data from a database
Your browser asks, and the server responds.
Simple.
So what is SSRF?
SSRF happens when:
An attacker tricks the server into making a request it was not supposed to make.
Instead of the attacker directly accessing something, they use the server to do it for them.
Why is that a problem?
Servers often have access to things that regular users don't.
So if an attacker tricks the server, they can gain access to:
- internal systems
- private data
- restricted resources
Things that are meant to be hidden.
Simple way to think about it
It's like this:
You can't enter a restricted room… but you convince someone who has access to go in for you.
And they do it, thinking everything is normal.
How do we prevent SSRF?
The key defense is:
Validate and sanitize URL inputs.
Let's break that down simply.
- Validate → Only allow trusted, expected URLs
- Sanitize → Clean the input so nothing harmful is hidden inside
In other words:
Don't let users send just any link. Only allow what is safe and expected.
Wrapping Up
And just like that… we've come to the end of the OWASP Top Ten.
Thank you for following along this series — truly.
From the beginning till now, we've broken concepts down step by step, keeping it simple and making it make sense.
If you remember nothing else, remember this little mnemonic we've been building along the way:
B… CIIS… VISSS✨
There's still a lot more to learn, and I'll be sharing more from my journey — especially from these platforms: Hack The Box and PortSwigger.
The wins. The confusion. The "wait, what just happened?" moments.
All of it.
Stay tuned!