A zero‑touch RCE attack refers to a remote code execution vulnerability that can be exploited without any user interaction — no clicking links, opening files, or approving prompts. If a vulnerable service is exposed (often network‑facing), an attacker can trigger code execution simply by sending specially crafted network traffic.
This class of attack is considered critical because it completely breaks traditional "user awareness" or "phishing resistance" defenses.
What "Zero‑Touch" Means
Zero‑touch = zero user action required.
The victim:
- Does not open a file
- Does not click a link
- Does not authenticate or approve anything
The attack succeeds purely due to:
- A design or implementation flaw
- In protocol parsing, deserialization, message handling, or pre‑auth logic.
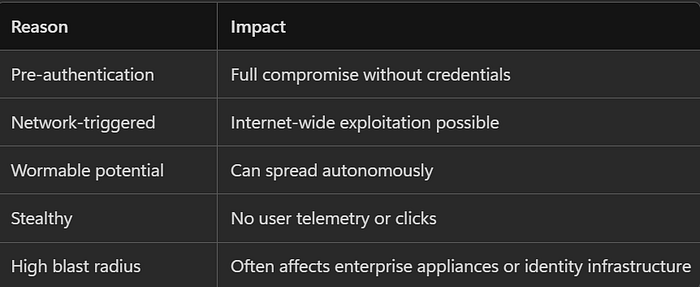
Why Zero‑Touch RCE Is So Dangerous
Typical Zero‑Touch RCE Attack Surfaces
Zero‑touch RCEs usually live in systems that must automatically trust and parse inbound data:
1. Network & Security Appliances
- Firewalls
- VPN concentrators
- ADCs / Load balancers
Why vulnerable: They parse complex traffic formats at high privilege levels.
2. Identity & Authentication Protocols
- Kerberos
- SSO components
- Federation services
Why vulnerable: Pre‑auth cryptographic parsing, ticket handling, and legacy compatibility layers.
Windows Kerberos RCE vulnerabilities (e.g., CVE‑class issues) allow arbitrary code execution without authentication if message validation fails
3. Management & Collaboration Platforms
- CI/CD controllers
- Knowledge bases
- Issue tracking systems
Why vulnerable: Template engines, YAML/JSON deserializers, macro execution paths.
Atlassian RCE issues tied to unsafe deserialization and template injection were highlighted in security briefings
4. Core Network Services
- SSH daemons
- RPC services
- Message brokers
Why vulnerable: Memory handling in long‑lived privileged processes.
The OpenSSH "regreSSHion" vulnerability shows how pre‑auth memory flaws can enable zero‑interaction RCE on Linux systems
How Zero‑Touch RCEs Are Typically Detected
Defensive Signals
- Crashes or restarts of critical services
- Unusual outbound connections from appliances
- Memory corruption alerts (EDR/XDR)
- Protocol anomalies (IDS/IPS)
Defensive Gaps
- No phishing telemetry
- No user logs
- Often no authentication logs
Mitigation & Defense Strategy (Enterprise‑Safe)
1. Exposure Reduction (Most Critical)
- Do not expose management interfaces to the internet
- Enforce network segmentation
- Zero‑trust front‑ending
2. Patch Velocity
- Zero‑touch RCEs are usually zero‑day or n‑day abused
- Appliances and identity systems must be patched as fast as endpoints
3. Compensating Controls
- IDS/IPS signatures for malformed protocol traffic
- WAF (limited effectiveness for protocol‑level flaws)
- Runtime memory protection where supported
4. Detection Engineering
- Behavioral baselines for "normally quiet" infrastructure
- East‑west traffic monitoring
- Appliance EDR where available
How This Maps to Security Frameworks
OWASP Top 10
- A03: Injection
- A08: Software and Data Integrity Failures
MITRE ATT&CK
- T1190 — Exploit Public‑Facing Application
- T1210 — Exploitation of Remote Services
NIST
- SI‑2 (Flaw Remediation)
- SC‑7 (Boundary Protection)