Imagine this: a security researcher sits in a car park outside a corporate office. With a laptop and a $30 software-defined radio, she sends a signal to the building's smart access control panel. The door clicks open. No badge. No credentials. No alarm.
This isn't fiction. It's exactly the class of attack that CISA warned about in March 2024 — when it published an advisory detailing a dozen critical vulnerabilities in Linear eMerge E3 door access control systems that had been sitting unpatched since 2019. One of those flaws had already been exploited in the wild.
The breach didn't start with a phishing email. It started with a door.
The Convergence Nobody Planned For
For decades, physical security and cybersecurity lived in separate departments, separate budgets, and separate conversations. Physical security meant locks, guards, and badge readers. Cyber security meant firewalls, antivirus, and SOC teams. The two barely spoke.
Then we connected everything to the internet — and the wall between those worlds collapsed.
Today's office buildings run on networks. Smart cameras stream to cloud dashboards. Access control panels communicate via IP. HVAC systems, elevators, and lighting are managed through IoT sensors. Every one of those devices is a potential entry point. And as operational technology converges with IT infrastructure, a compromise in the physical layer is no longer just a broken lock — it's an open door into the corporate network.
Three Scenarios That Should Keep You Up at Night
⚠ Scenario 01 — Access Control as a Network Gateway
In May 2019, researchers at Applied Risk identified ten critical vulnerabilities in Nortek Linear eMerge E3 building access systems — the exact hardware used in thousands of corporate offices and data centers. Six of those flaws scored a perfect 9.8 or 10 on the CVSS severity scale. Attackers could remotely hijack credentials, unlock or lock physical doors, install malware, and pivot directly into the connected corporate network. Tens of thousands of probing attempts were recorded daily across 100 countries before patches were eventually issued — years later. The door wasn't just a door. It was a network interface disguised as physical security.
⚠ Scenario 02 — Smart Cameras Turned Into Weapons
In August 2024, security researchers discovered that AVTECH IP cameras — deployed across finance, healthcare, transportation, and public health infrastructure — were being actively exploited to spread Mirai malware. The vulnerability had been known since 2019 and still had no patch available five years later. These cameras, meant to watch for threats, had become the threat itself. Attackers used them as launch pads for DDoS attacks, credential harvesting, and network infiltration. The physical surveillance layer had been weaponized against the organizations it was meant to protect.
⚠ Scenario 03 — Smart City Infrastructure Taken Offline
In May 2024, a distributed denial-of-service attack struck a major smart city in Asia. Traffic lights, surveillance cameras, waste management systems, and public utilities were simultaneously knocked offline. The attack exploited weak authentication and outdated IoT protocols — standard vulnerabilities in municipal infrastructure that moves slowly on patching cycles. The result wasn't a data breach. It was a physical city brought to its knees by a digital attack. Traffic congestion. Public safety failures. Hours of real-world disruption caused by code.
"The door to your building and the door to your data center are now the same door. Most organizations haven't accepted that yet."
Why This Problem Is Structurally Worse Than It Looks
The root cause isn't laziness. It's architecture. IoT and physical security devices were designed for longevity, not agility. A badge reader or IP camera is expected to sit on a wall for a decade. It doesn't have the compute resources for robust encryption. It wasn't built with an automated update mechanism. And because it "just works," nobody touches it.
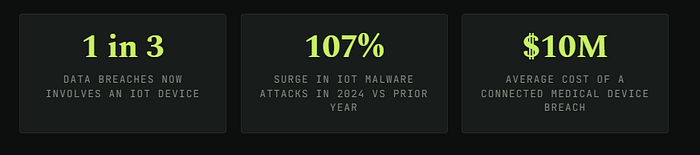
That's precisely what attackers count on. 60% of IoT breaches are caused by unpatched firmware and outdated software. And one in five IoT devices still ships with factory-default login credentials. In 2024, attackers continued exploiting a known command-injection flaw in TP-Link routers — affecting over 21% of small and medium businesses — years after the CVE was published.
The attack surface is also growing faster than most teams can track. The average enterprise now operates thousands of connected devices across its facilities. Each one represents a potential pivot point for an adversary who's already inside the network perimeter — or looking for a way in through the physical layer.
What "Cyber-Physical" Actually Means for Risk Teams
The consequences of cyber-physical breaches aren't just financial. They're operational, reputational, and in some industries — life-threatening.
In February 2024, ransomware actors compromised IoT-connected medical devices across several U.S. hospitals — seizing control of patient monitoring systems, infusion pumps, and MRI machines. Hospitals reverted to manual procedures. Patient care was directly impacted. This wasn't a data exfiltration event. It was a clinical emergency triggered by a software exploit.
In industrial settings, the risk is equally stark. Cyber-physical attacks on European manufacturing plants in June 2024 exploited weak IIoT communication protocols, manipulating machinery and halting production lines entirely. The average cost of a manufacturing sector data breach reached $4.97 million in 2024 — and that figure doesn't include production downtime, supply chain disruption, or long-term reputational damage.
This is no longer a niche concern for critical infrastructure teams. It's a board-level risk for any organization that operates physical facilities connected to digital systems — which, in 2025, is nearly every organization.
Five Things Your Security Team Should Do This Quarter
Priority Action List — Cyber-Physical Security
01
Audit your physical device inventory. You can't protect what you can't see. Create a complete inventory of every IP-connected physical security device — cameras, access panels, sensors, intercoms — and map them to network zones. Treat unmanaged devices as active vulnerabilities.
02
Segment your physical security network. IoT and physical security devices should never share a flat network with corporate systems. Network segmentation limits lateral movement — organizations that implement it reduce breach costs by 35%. It's one of the highest-ROI controls available.
03
Eliminate default credentials immediately. The UK's PSTI Act, which came into effect in April 2024, legally bans default passwords on connected devices. Even if you're not UK-regulated, the principle is non-negotiable. One in five IoT devices still ships with factory defaults. That's an open invitation.
04
Establish a firmware patching cadence. Physical security devices need patching just like servers do. Assign ownership, track CVEs relevant to your hardware, and define an acceptable patch window. Legacy devices that can't be patched should be isolated or replaced — not ignored.
05
Run cross-functional tabletop exercises. Most incident response plans treat physical and digital threats separately. Run scenarios where a compromised badge reader leads to a network breach, or where a camera exploit enables physical intrusion. The convergence is real. Your playbooks should reflect it.
The Bottom Line
The hacked door in the opening scenario isn't a hypothetical. Variants of it have happened in corporate campuses, hospitals, government buildings, and smart city infrastructure — often going undetected for months, because the security team was watching the firewall logs, not the door controller event logs.
Cyber-physical security isn't a specialty vertical anymore. It's a fundamental dimension of organizational risk. The companies that understand this are already running unified security programs that treat a compromised IP camera the same way they'd treat a compromised endpoint — with the same urgency, the same visibility, and the same response protocols.
The ones that don't? They're leaving a door open. Literally.
