Introduction
In cybersecurity, reconnaissance is the foundation of every security assessment. The ability to efficiently collect, analyze, and structure target information is critical for identifying potential vulnerabilities.
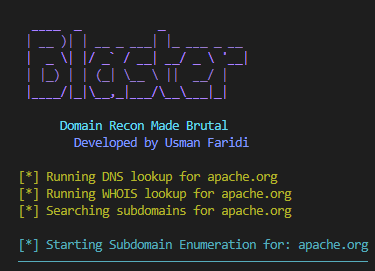
To improve and automate this process, I developed Blaster, a Python-based reconnaissance tool designed for multi-layered security analysis.
This article introduces Blaster v2.0, a major architectural upgrade that transforms the tool from a basic scanner into a modular reconnaissance framework.
What is Blaster?
Blaster is an open-source Python reconnaissance tool designed to automate common information-gathering tasks used in security analysis.
It supports:
- DNS enumeration
- Subdomain discovery
- WHOIS lookups
- Network scanning
- Technology Fingerprinting
- Threat Intel
- Infrastructure analysis with deep scanning
- Structured and Professional report in 3 different formats (.html, json and txt)
Its goal is to simplify and structure reconnaissance workflows for security researchers, students, and penetration testers.
🚀 How to Use Blaster
Blaster is designed to be simple to execute while providing modular control over different reconnaissance components.
You can run modules in any sequence that you like, the reporting works with every module, not just the full scan.
To download go to:
https://github.com/Faridi-m/Blaster-v2.0
🔧 Basic Usage
Install all the requirements before running the tool
git clone https://github.com/Faridi-m/blaster.git
cd blaster
python3 -m venv <your enviornment name> # python virtual environment
source venv/bin/activate # Linux/Mac
venv\Scripts\activate # Windows
pip install -r requirements.txtRun the main tool:
python blaster.py
or
python blaster.py -h, --help🌐 DNS Enumeration
python blaster.py --dns example.com
or
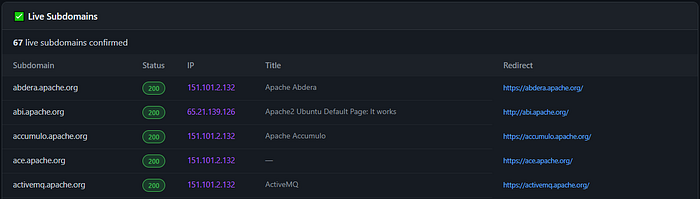
python blaster.py --dns example.com --output report.html, json and txt🕵️ Subdomain Discovery with (live active domains)
python blaster.py --subdomains example.com
or
python blaster.py --subdomains --live example.com --output report.html, json and txt📡 Nmap Network Scan
python blaster.py --ports example.com👤 WHOIS Lookup
python blaster.py --whois example.com🌍 SSL/TLS Analysis
python blaster.py --ssl example.com🌐 HTTP Headers Audit
python blaster.py --headers example.com🧠 Technology Fingerprinting
python blaster.py --tech example.com🔥 Threat Intelligence Check
python blaster.py --threat example.com🧪 Full Scan Mode (Recommended)
python blaster.py --full example.com
or
python blaster.py --full example.com --ouput report.html, json and txt💡 Note
Each module is designed to run independently or as part of a full reconnaissance pipeline, allowing flexible usage depending on the target and analysis depth
🧠 Blaster v2.0 — What Changed?
Blaster v2.0 is not just an update — it is a complete modular redesign.
The focus of this release is:
- Better architecture
- Expanded intelligence capabilities
- Improved output structure
- More extensibility for future modules
🔍 New Intelligence Modules
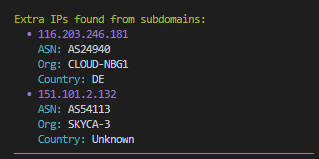
ASN Analysis Module
Provides insights into Autonomous System Numbers (ASN), helping map network ownership and infrastructure distribution.
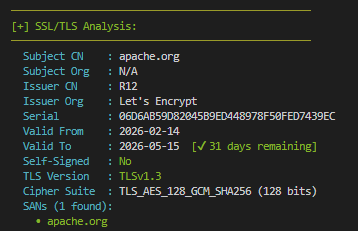
SSL/TLS Security Module
Analyzes certificate details and encryption configurations to identify weak or misconfigured security setups.
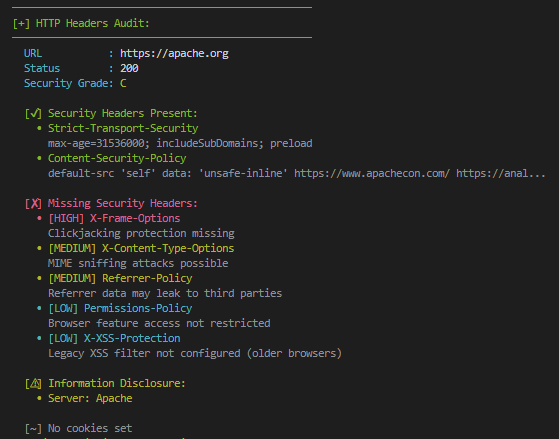
HTTP Headers Audit Module
The HTTP Headers Audit Module is designed to analyze security-related headers returned by a target web server. This module evaluates whether important security headers are properly configured or missing.
It checks for headers such as:
- Content-Security-Policy (CSP)
- Strict-Transport-Security (HSTS)
- X-Frame-Options
- X-Content-Type-Options
- Referrer-Policy
- Permissions-Policy
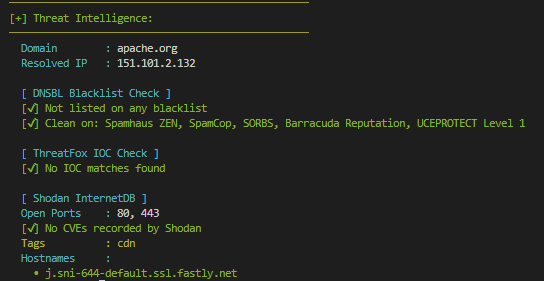
Threat Intelligence Module
Adds contextual security intelligence to help identify suspicious infrastructure patterns and potential risks. It checks the domain on various channels and tells whether the domain is blacklisted or has any CVE's recorded under their name.
Technology Detection Engine
Detects underlying technologies used by target systems, including frameworks, servers, and hosting environments.

⚙️ Improvements in Core Modules
Existing modules were significantly enhanced in v2.0:
- DNS Module → Improved resolution accuracy and structured output
- Nmap Integration → Better scan logic and cleaner results
- Subdomain Enumeration → Expanded discovery coverage with live subdomains
- WHOIS Module → More reliable parsing and formatting
These upgrades improve both accuracy and usability in real-world reconnaissance scenarios.
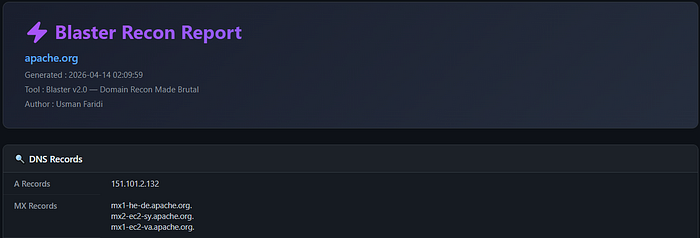
📊 Reporting System Upgrade
A major focus of v2.0 is structured reporting.
The new reporting system provides:
- Clean and readable scan results
- Organized output formatting
- Better data interpretation for analysts
- Easier integration into workflows
🧹 Architecture Improvements
Blaster v2.0 introduces a more maintainable and scalable architecture:
- Fully modular design for each reconnaissance component
- Clear separation of functionality
- Improved maintainability for future development
- Introduction of
.gitignorefor repository hygiene
This makes the tool easier to extend and improve over time.
🔄 v1.0 vs v2.0 Comparison
| Feature | v1.0 | v2.0 |
| --------------------- | --------------- | ---------------------- |
| Architecture | Basic structure | Modular framework |
| Scanning capability | Limited | Enhanced |
| Intelligence features | None/minimal | ASN, SSL, HTTP Headers Audit, Threat Intel |
| Reporting | Basic output | Structured reports |
| Extensibility | Low | High |Conclusion
Blaster v2.0 represents a significant evolution from a simple reconnaissance script to a structured and extensible security framework.
The focus moving forward is scalability, modular intelligence, and real-world applicability in security workflows.
Final Note
This release lays the foundation for future expansion into a full-fledged reconnaissance ecosystem.