If you are passionate about Microsoft 365 governance, Purview, Entra, Azure, and secure digital transformation, let's collaborate and advance governance maturity together.
Read Complete Article |
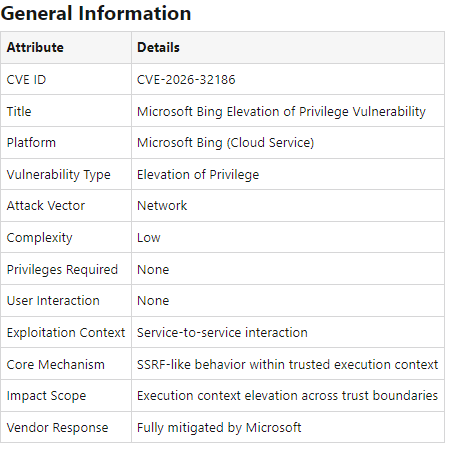
CVE-2026–32186 | Microsoft Bing Elevation of Privilege Vulnerability
Let's Connect |

Hire Aakash Rahsi | Expert in Intune, Automation, AI, and Cloud Solutions
CVE-2026–32186 | Microsoft Bing Elevation of Privilege Vulnerability
There are moments in cybersecurity that don't arrive loudly.
They don't announce disruption.
They reveal design.
CVE-2026–32186 is one of those moments.
But a quiet demonstration of how execution context, service trust boundaries and cloud-native design philosophy operate at scale inside Microsoft's ecosystem.
The Silent Signal
Within the vast surface of Microsoft Bing's cloud infrastructure, this vulnerability highlights something deeper:
- How distributed services interpret trusted inputs
- How execution contexts are inherited across boundaries
- How service-to-service communication behaves under designed conditions
This is not about breaking systems.
This is about understanding how systems are intended to operate under pressure.
Design Philosophy in Motion
Microsoft's architecture reflects a layered model where:
- Trust is granted, not assumed
- Execution flows are context-aware
- Cloud services operate within clearly defined boundaries
CVE-2026–32186 offers a lens into how:
- SSRF-like behaviors interact with internal service layers
- Privilege elevation emerges through contextual trust alignment
- Cloud orchestration respects identity, not just requests
Why This Matters
Because modern cybersecurity is no longer about endpoints.
It is about:
- Control planes
- Service identity
- Execution lineage
And most importantly:
How systems behave when everything is working as designed
Azure, Bing, and the Bigger Picture
This is not a story of disruption.
It is a study of scale, trust, and orchestration.
A reminder that:
- Cloud systems are living architectures
- Security is embedded in behavior, not just controls
- True understanding comes from observing how design manifests in reality
The most powerful signals in cybersecurity are rarely loud.
They are precise.
They are quiet.
They are deeply embedded in design.
And those who understand them…
don't react.
They interpret.