Weakness:Sensitive Information Disclosure / Improper Access Control Severity: High Status: Resolved Program: Responsible Disclosure (Direct to ETH Zurich CSIRT)
What Happened:
While reviewing a subdomain on ETH Zurich's infrastructure, I found Directory Listing enabled on a MediaWiki installation. Among the exposed files was a 3.6 GB PostgreSQL database dump — freely downloadable with no authentication required.
The Core Issue:
Directory Listing gives any visitor a full index of files in a directory. Combined with a database dump left in a publicly accessible path, this creates a straightforward path to downloading the entire database contents in one request.
The file wasn't hidden or protected — it was sitting in plain sight, indexed and accessible to anyone who visited the URL.
Why This Keeps Happening:
Database dumps are often created for migration or backup purposes and temporarily placed in web-accessible directories. The problem is "temporary" rarely gets enforced. Without automated checks on what's exposed in public directories, these files linger indefinitely.
Impact:
A 3.6 GB database dump likely contains the full dataset of the application — user records, configurations, and any other stored data. Even for a student project or test installation, this can include real user data or credentials reused elsewhere.
The exposure requires zero technical skill to exploit — just a browser and a download.
Timeline:
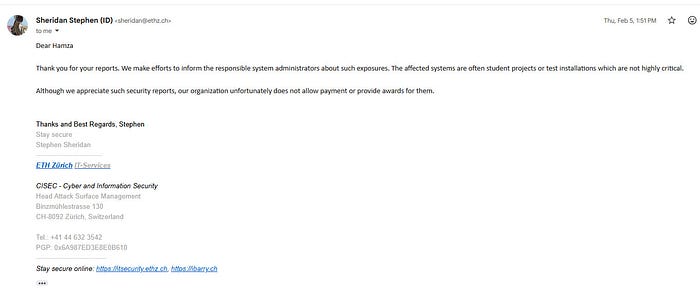
- Feb 5, 2026 — Reported to ETH Zurich CSIRT - Feb 5, 2026 — ETH Zurich acknowledged the report and notified the responsible system administrator
Remediation:
- Disable Directory Listing globally across all hosted subdomains - Never place database dumps in web-accessible directories - Implement automated scanning to detect publicly exposed sensitive files - Set up periodic audits on student and test installations — they carry the same exposure risk as production systems
Reported: February 2026 — Resolved by ETH Zurich IT Security.