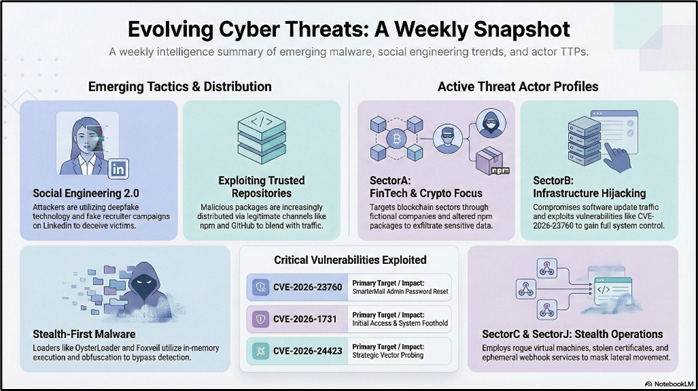
This week, the cybersecurity landscape is characterized by a diverse array of sophisticated cyber threat campaigns, each employing unique tactics, techniques, and procedures (TTPs) to achieve their objectives. The overarching trend among these campaigns is the exploitation of both human and technological vulnerabilities to gain unauthorized access, exfiltrate sensitive data, and deploy malicious payloads. Attackers are leveraging advanced social engineering techniques, such as deepfake technology, spear-phishing, and typosquatting, to deceive victims into executing malicious commands or providing sensitive information. These campaigns target a wide range of sectors, including cryptocurrency, financial services, government, and critical infrastructure, with a particular focus on exploiting emerging technologies like blockchain and cryptocurrency platforms. The malware used in these campaigns exhibits high levels of sophistication, with functionalities designed to evade detection and persist within compromised systems. Notable examples include multi-stage loaders like OysterLoader and Foxveil, which utilize obfuscation and in-memory execution to deliver payloads stealthily. Information stealers such as LummaStealer and Odyssey Stealer are employed to harvest credentials and cryptocurrency wallet data, while ransomware variants like LockBit 5.0 and Gunra RaaS demonstrate the continued evolution of ransomware-as-a-service models, emphasizing strong encryption and strategic targeting to maximize impact. Public platforms and repositories, such as GitHub and npm, are increasingly being exploited as distribution channels for malicious packages, highlighting the attackers' ability to blend malicious activity with legitimate traffic. Additionally, the use of legitimate tools and services, such as Velociraptor and Syncthing, for malicious purposes underscores the attackers' adaptability and resourcefulness in leveraging existing technologies to achieve their goals. Overall, the threat landscape this week is marked by a convergence of advanced malware capabilities, innovative social engineering tactics, and strategic targeting, reflecting the ongoing challenges faced by cybersecurity professionals in defending against increasingly sophisticated cyber threats.
The hacking activities associated with the SectorA Group demonstrate a high level of sophistication and strategic targeting, particularly within the realms of cryptocurrency and financial technology. The group's operations are characterized by their use of advanced social engineering tactics, such as fake recruiter campaigns and deceptive communications through platforms like LinkedIn, Reddit, and Facebook. These campaigns often involve the creation of fictional companies in the blockchain and cryptocurrency sectors to lure victims. A notable technique employed by the SectorA Group is the alteration of npm packages and GitHub repositories, embedding malicious code within seemingly legitimate software projects. This approach not only exploits public package repositories like npm and PyPI as distribution channels but also leverages the trust developers place in these platforms. The group's malware exhibits modularity and persistence, with multi-layered components such as remote-access trojans (RATs) that communicate with command-and-control servers using token-protected commands. Another tactic involves the use of disguised malicious shortcut files (.lnk) to execute PowerShell scripts, which are obfuscated to evade antivirus detection. These scripts facilitate the download and execution of additional payloads from controlled GitHub repositories, establishing persistence through disguised scheduled tasks. The SectorA Group's operations also include reconnaissance activities, collecting system and security data for potential targeted malware development. Their attacks on FinTech companies further illustrate their capability, employing complex methods like compromised communication platforms, deepfake AI videos, and a suite of malware tools designed for data capture and credential theft. The use of specific C&C servers for communication underscores their precise and targeted efforts aimed at financial theft and extended malicious campaigns. Overall, the SectorA Group's tactics, techniques, and procedures (TTPs) highlight their technical prowess and focus on exploiting the cryptocurrency and financial sectors through sophisticated and persistent cyber operations.
SectorB Group has demonstrated a sophisticated and strategic approach in its cyber attack campaigns, characterized by advanced Tactics, Techniques, and Procedures (TTPs) and a focus on intelligence gathering rather than overt disruption. The group's activities, as evidenced by the attacks on Notepad++ and SmarterMail servers, reveal a pattern of exploiting vulnerabilities in widely-used software to infiltrate targeted systems. In the Notepad++ incident, SectorB Group compromised the hosting infrastructure to hijack update traffic, specifically targeting users in Southeast Asia's government, telecommunications, and critical infrastructure sectors. They employed DLL sideloading and Lua script injection to deploy the Cobalt Strike Beacon malware and a backdoor named Chrysalis, utilizing Microsoft's Warbird code protection framework and custom API hashing to evade antivirus detection. Their adversary-in-the-middle approach allowed for dynamic fingerprinting and selective targeting, minimizing the risk of detection by the software vendor. In the SmarterMail attack, the group exploited a critical vulnerability (CVE-2026–23760) to reset administrator passwords and gain full system control, using the Volume Mount feature to inject malicious commands. They maintained persistence through Velociraptor, a legitimate forensic tool, to stage ransomware operations. The concurrent probing for another vulnerability (CVE-2026–24423) underscores their methodical testing of multiple attack vectors. SectorB Group's operations highlight their capability to leverage legitimate software features for malicious purposes, emphasizing the need for robust defenses against such sophisticated threats. Their focus on system administrators and developers in strategic regions further illustrates their intent to gather valuable intelligence, leveraging advanced evasion techniques to remain undetected.
The hacking activities associated with the SectorC Group, as evidenced by the "Operation MacroMaze" campaign, demonstrate a sophisticated and evolving approach to cyber threats, particularly targeting entities in Western and Central Europe. This campaign is characterized by its use of spear-phishing tactics, leveraging documents that mimic agendas from official sources to entice victims into opening them. The malicious documents contained macros that cleverly utilized the INCLUDEPICTURE field within their XML structure to initiate HTTP requests, effectively confirming when a document was accessed. These macros served as droppers, deploying multiple files into the victim's %USERPROFILE% directory, which were designed to exfiltrate data through HTML forms. Over the course of the campaign, four document variants were observed, each showcasing enhanced evasive techniques such as headless browser execution and keyboard simulation to bypass security measures. The SectorC Group demonstrated a preference for stealth, employing payload distribution and data exfiltration via webhook services to ensure operations remained ephemeral and less detectable. The use of batch files facilitated a multi-stage execution process, with Microsoft Edge being leveraged for both payload delivery and data exfiltration. This approach allowed the attackers to conceal their activities through off-screen execution and by leaving minimal artifacts on the disk, thereby reducing the likelihood of detection. Overall, the SectorC Group's TTPs reflect a high level of sophistication and adaptability, focusing on stealth and evasion to achieve their objectives.
The cyber attack attributed to the SectorJ Group showcases a highly sophisticated approach, emphasizing their adeptness in exploiting both technological and human vulnerabilities. The attackers initiated their operation by gaining unauthorized access to a VMware vSphere environment, a critical infrastructure component for many organizations. This access facilitated the creation of a rogue virtual machine, which served as a launchpad for further malicious activities. The attackers' tactics, techniques, and procedures (TTPs) included advanced reconnaissance and the strategic download of tools necessary for maintaining persistence and conducting lateral movement within the network. A key aspect of their methodology was the establishment of a command and control (C2) channel using stolen certificates, which underscores their capability to leverage legitimate credentials to mask their activities. The attackers' use of tools such as Chisel for SSH tunneling and ADRecon for Active Directory enumeration highlights their focus on gathering sensitive domain data, which is crucial for understanding the network architecture and identifying high-value targets. The extraction of critical files like the NTDS.dit and SYSTEM registry hive from the domain controller indicates a targeted effort to compromise user credentials, facilitating further infiltration and data exfiltration attempts. The employment of PsExec for lateral movement demonstrates their proficiency in using legitimate administrative tools to navigate the network undetected. Throughout the attack, the SectorJ Group exhibited a clear understanding of exploiting human vulnerabilities, such as weak access controls, which allowed them to escalate privileges and maintain a foothold within the environment. This incident underscores the necessity for organizations to implement robust identity security measures and enforce strict access controls to mitigate the risk posed by such advanced threat actors. The SectorJ Group's activities reflect a calculated and methodical approach to cyber intrusion, leveraging both technical exploits and social engineering techniques to achieve their objectives.
Key Characteristics of This Week's Cyber Threats
This week, various cyber threat incidents have been characterized by a wide array of technical and tactical approaches, showcasing the sophistication and diversity of modern cyberattacks. A notable trend is the exploitation of legitimate platforms and tools to distribute malware and conduct malicious activities. For instance, fake recruiter campaigns targeting JavaScript and Python developers have been identified, leveraging platforms like LinkedIn, Reddit, and Facebook to lure victims with job offers. These campaigns utilize altered npm packages and GitHub repositories to embed malicious code, leading to the execution of remote-access trojans (RATs) that communicate with command-and-control (C2) servers using token-protected commands. Malware distribution through public package repositories such as npm and PyPI is a recurring theme, with attackers embedding downloaders within dependencies to fetch final payloads. This approach highlights the modularity and persistence of the malware, often associated with state-sponsored threat actors focusing on cryptotrading. Similarly, the use of disguised malicious shortcut files (.lnk) to execute PowerShell scripts is another tactic observed this week. These scripts drop additional payloads and establish persistence through scheduled tasks, exfiltrating system and security data to GitHub. North Korean threat actors have executed complex attacks on FinTech companies in the cryptocurrency and DeFi sectors, employing social engineering tactics like compromised Telegram accounts and fake Zoom meetings. The use of deepfake AI videos and ClickFix infection vectors further illustrates the sophistication of these operations. The deployment of multiple malware families, including DEEPBREATH, SUGARLOADER, and WAVESHAPER, underscores the attackers' focus on financial theft and extended malicious campaigns. Compromises of official hosting infrastructures, such as the Notepad++ update server, have been reported, with attackers hijacking traffic to serve malicious update manifests. Techniques like DLL sideloading and Lua script injection are employed to deliver Cobalt Strike Beacon malware and backdoors. The use of Microsoft's Warbird code protection framework and custom API hashing demonstrates advanced evasion techniques aimed at intelligence gathering. Exploitation of vulnerabilities in software like SmarterMail servers and Ivanti Endpoint Manager Mobile (EPMM) has been a focal point this week. Attackers have leveraged these vulnerabilities to reset administrator passwords, gain system control, and stage ransomware operations. The use of legitimate forensic tools like Velociraptor for persistence and the emphasis on multi-step exploitation chains highlight the sophistication of these attacks. Phishing campaigns remain prevalent, with spear-phishing documents leveraging agendas from government ministries and employing macros to trigger HTTP requests. The use of QR codes in phishing attacks is also notable, with attackers exploiting these codes to bypass security measures and distribute malicious apps. Additionally, the misuse of AI-assisted website builders to create fake sites, such as a fraudulent Malwarebytes site, demonstrates the evolving tactics of cybercriminals. The deployment of information-stealing malware, such as LummaStealer and Odyssey Stealer, is a significant concern. These malware variants target sensitive data, including browser credentials and cryptocurrency wallets, often using social engineering tactics to entice users into executing infected files. The use of sophisticated loaders like CastleLoader and OysterLoader, employing in-memory execution and heavy obfuscation, further complicates detection and mitigation efforts. Ransomware-as-a-service (RaaS) models, such as Gunra and LockBit version 5.0, continue to pose significant threats, with strong encryption and strategic exclusions to ensure system functionality for ransom payments. These operations emphasize operational impact, leading to financial, operational, and reputational damages for affected organizations. Overall, this week's cyber threat landscape is marked by the strategic use of legitimate platforms, advanced evasion techniques, and sophisticated malware distribution methods. The focus on exploiting vulnerabilities, leveraging social engineering, and employing multi-stage infection chains highlights the need for robust defensive measures and heightened vigilance against evolving cyber threats.
Key Takeaways from This Week's Cyber Threat Landscape
The cyber threat landscape this week presents a complex array of sophisticated attack vectors and methodologies that underscore the evolving nature of cyber threats. The security implications for organizations are significant, as these incidents highlight vulnerabilities across various platforms and technologies, including cloud services, open-source repositories, and widely-used software applications. The exploitation of npm packages and GitHub repositories to deliver remote-access trojans (RATs) through altered software projects illustrates the persistent risk posed by supply chain attacks. This tactic not only compromises individual developers but also threatens the integrity of software used by enterprises globally. Organizations must enhance their software supply chain security by implementing rigorous code review processes, employing automated tools to detect malicious code, and fostering a culture of security awareness among developers. The use of social engineering tactics, such as fake recruiter campaigns and deepfake technology, emphasizes the need for robust user education and awareness programs. These campaigns exploit human vulnerabilities, making it crucial for organizations to train employees to recognize and report suspicious activities. Additionally, the integration of advanced threat detection systems capable of identifying anomalous behavior and unauthorized access attempts is essential to mitigate the risks associated with these sophisticated social engineering attacks. The compromise of hosting infrastructure for widely-used applications like Notepad++ and the exploitation of vulnerabilities in SmarterMail servers highlight the importance of maintaining a strong security posture for critical infrastructure. Organizations must prioritize patch management and vulnerability assessment to ensure that systems are protected against known exploits. The deployment of advanced endpoint protection solutions and the implementation of network segmentation can further reduce the attack surface and limit the impact of potential breaches. The emergence of ransomware-as-a-service (RaaS) platforms, such as Gunra, and the use of sophisticated loaders like Foxveil, demonstrate the increasing commoditization of cybercrime. This trend lowers the barrier to entry for cybercriminals, enabling less skilled actors to launch complex attacks. Organizations must adopt a multi-layered security approach, incorporating threat intelligence, intrusion detection, and incident response capabilities to effectively combat these threats. The use of encryption and secure key management practices is also critical to protect sensitive data from ransomware attacks. The exploitation of vulnerabilities in widely-used software, such as BeyondTrust's Remote Support and Ivanti Endpoint Manager Mobile (EPMM), underscores the need for continuous monitoring and assessment of third-party applications. Organizations should establish a comprehensive vulnerability management program that includes regular scanning, patching, and testing of all software components. Additionally, the implementation of application whitelisting and the use of secure configurations can help prevent unauthorized code execution and reduce the risk of exploitation. The rise of information-stealing malware, such as LummaStealer and Odyssey Stealer, highlights the importance of protecting sensitive data and credentials. Organizations must implement strong authentication mechanisms, such as multi-factor authentication (MFA), to safeguard access to critical systems and data. The use of data loss prevention (DLP) solutions and encryption can further protect sensitive information from unauthorized access and exfiltration. The increasing use of QR codes and typosquatting domains for phishing and fraud campaigns demonstrates the need for heightened vigilance and user education. Organizations should educate employees and customers about the risks associated with scanning QR codes and visiting unfamiliar websites. The deployment of web filtering solutions and the use of secure browsing practices can help mitigate the risks associated with these attack vectors. Overall, the diverse range of cyber threats observed this week underscores the need for organizations to adopt a proactive and comprehensive cybersecurity strategy. By implementing a combination of technical controls, user education, and threat intelligence, organizations can enhance their resilience against the ever-evolving cyber threat landscape.