TryHeartMe (Web Challenge)
🧩 Challenge Overview
- Category: Web
- Difficulty: Easy
- Goal: Purchase the hidden
ValenFlagitem
Initial Observation
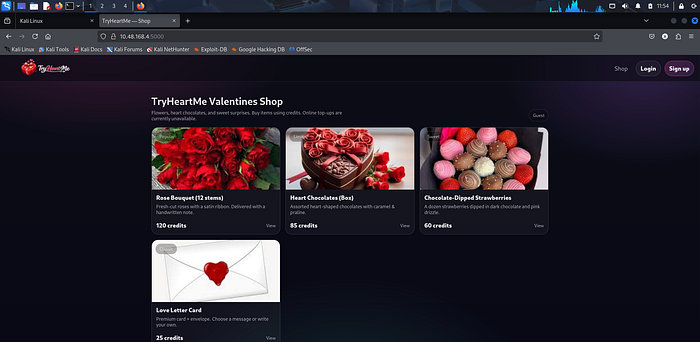
After logging into the web app:
The shop displays normal items like:
- Rose Bouquet
- Chocolates
- Love Letter
Important: ➡️ ValenFlag is NOT visible initially
This indicates:
The item is restricted or hidden based on user privileges

🧠 Enumeration
🔎 Step 1: Inspect Application Behavior
- Checked all visible routes → nothing unusual
- Tried guessing endpoints → not accessible initially
- UI did NOT show the flag item
So next step:
👉 Check client-side storage (cookies)
🍪 Step 2: Analyze JWT Cookie
In DevTools → Application → Cookies:
tryheartme_jwt = eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9...Decoded JWT reveals something like:
{
"email": "yourmail@gmail.com",
"role": "user"
}⚠️ Vulnerability Identified
🚨 The application uses JWT for role-based access control
But:
- Role is stored client-side
- Likely not properly validated
🚀 Exploitation
🔧 Step 1: Modify JWT Payload
Change role:
"role": "admin"🔧 Step 2: Re-sign / Tamper Token
- Either:
- Signature not verified ❌
- Or weak secret used
Replace cookie in browser:
tryheartme_jwt = <modified_token>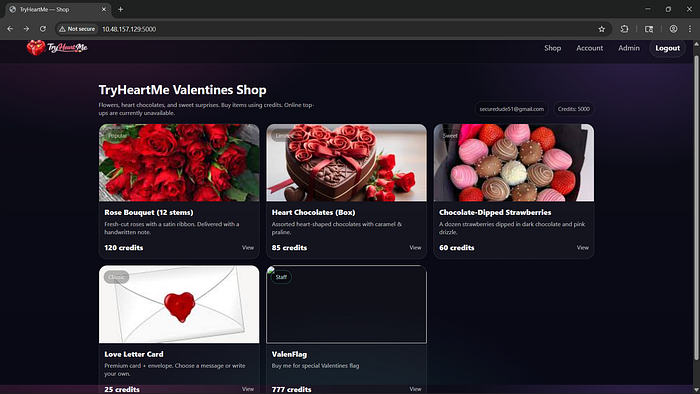
🎯 Step 3: Refresh Application
After updating the cookie:
✅ ValenFlag item becomes visible in shop
➡️ This confirms:
UI rendering depends on JWT role
🛒 Step 4: Purchase Hidden Item
- Click on ValenFlag
- Complete purchase

Redirects to:
/receipt/valenflag🏁 Flag
THM{**********************}🛡️ Root Cause Analysis
🔥 Main Vulnerabilities:
- ❌ Client-side role control (JWT)
- ❌ No proper signature validation
- ❌ Missing backend authorization checks
- ❌ Sensitive functionality exposed via UI logic
💡 Key Takeaways
- Never trust JWT payload without verification
- Always enforce server-side authorization
- Do NOT rely on frontend to hide sensitive features
- Use strong secrets & validate tokens properly
🚀 Final Insight
This challenge is of:
🔓 JWT Cookie Tampering → Privilege Escalation → Broken Access Control


